microsoft SC-200 Exam Questions
Questions for the SC-200 were updated on : Jul 20 ,2024
Page 1 out of 8. Viewing questions 1-15 out of 110
Question 1 Topic 1, Case Study 1Case Study Question View Case
The issue for which team can be resolved by using Microsoft Defender for Endpoint?
- A. executive
- B. sales
- C. marketing
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/microsoft-defender-
atp-ios
Question 2 Topic 1, Case Study 1Case Study Question View Case
The issue for which team can be resolved by using Microsoft Defender for Office 365?
- A. executive
- B. marketing
- C. security
- D. sales
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/atp-for-spo-odb-and-
teams?view=o365-worldwide
Question 3 Topic 2, Case Study 2Case Study Question View Case
You need to implement the Azure Information Protection requirements.
What should you configure first?
- A. Device health and compliance reports settings in Microsoft Defender Security Center
- B. scanner clusters in Azure Information Protection from the Azure portal
- C. content scan jobs in Azure Information Protection from the Azure portal
- D. Advanced features from Settings in Microsoft Defender Security Center
Answer:
D
Explanation:
Reference: https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/information-
protection-in-windows-overview
Question 4 Topic 2, Case Study 2Case Study Question View Case
You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements and resolve the
reported problem.
Which policy should you modify?
- A. Activity from suspicious IP addresses
- B. Activity from anonymous IP addresses
- C. Impossible travel
- D. Risky sign-in
Answer:
C
Explanation:
Reference: https://docs.microsoft.com/en-us/cloud-app-security/anomaly-detection-policy
Question 5 Topic 2, Case Study 2Case Study Question View Case
DRAG DROP
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the
answer area and arrange them in the correct order.
Select and Place: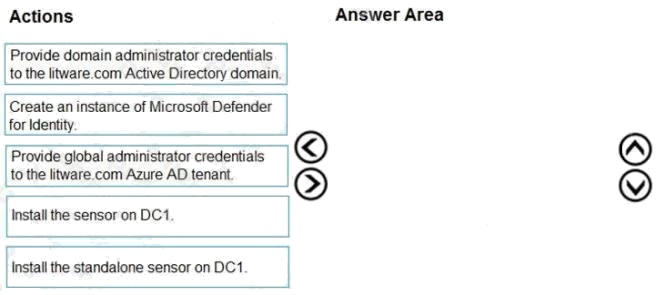
Answer:
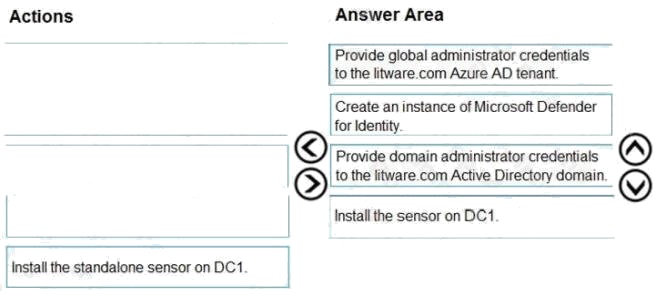
Explanation:
Step 1: log in to https://portal.atp.azure.com as a global admin
Step 2: Create the instance Step 3. Connect the instance to Active Directory Step 4. Download and install the sensor.
Reference: https://docs.microsoft.com/en-us/defender-for-identity/install-step1 https://docs.microsoft.com/en-us/defender-for-
identity/install-step4
Question 6 Topic 3, Case Study 3Case Study Question View Case
HOTSPOT
You need to recommend remediation actions for the Azure Defender alerts for Fabrikam.
What should you recommend for each threat? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: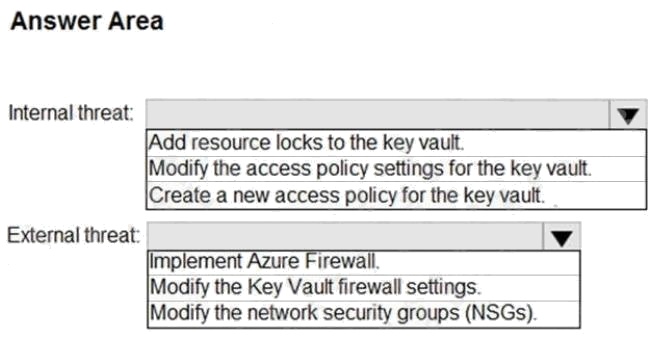
Answer:
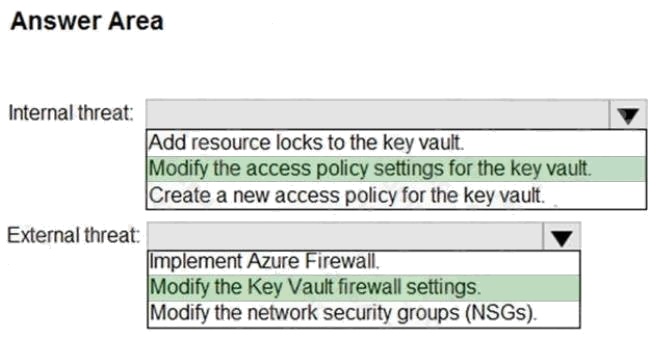
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/key-vault/general/security-features https://docs.microsoft.com/en-
us/azure/key-vault/general/secure-your-key-vault
Question 7 Topic 3, Case Study 3Case Study Question View Case
You need to recommend a solution to meet the technical requirements for the Azure virtual machines.
What should you include in the recommendation?
- A. just-in-time (JIT) access
- B. Azure Defender
- C. Azure Firewall
- D. Azure Application Gateway
Answer:
B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/security-center/azure-defender
Question 8 Topic 4, Case Study 4Case Study Question View Case
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
- A. Security alerts in Azure Security Center
- B. Activity log in Azure
- C. Azure Advisor
- D. the query windows of the Log Analytics workspace
Answer:
D
Question 9 Topic 4, Case Study 4Case Study Question View Case
You need to remediate active attacks to meet the technical requirements.
What should you include in the solution?
- A. Azure Automation runbooks
- B. Azure Logic Apps
- C. Azure Functions
- D. Azure Sentinel livestreams
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/automate-responses-with-playbooks
Question 10 Topic 4, Case Study 4Case Study Question View Case
HOTSPOT
You need to create an advanced hunting query to investigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: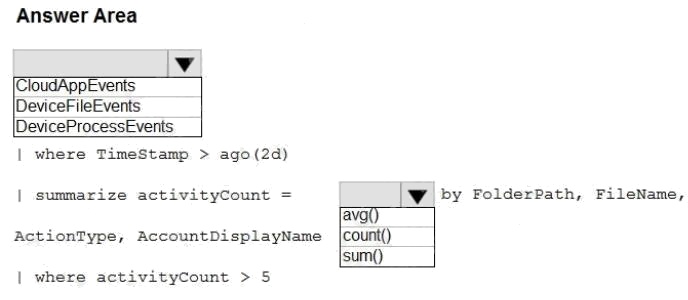
Answer:
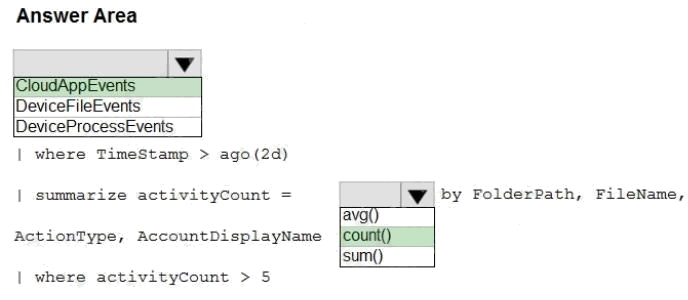
Explanation:
Mitigate threats using Azure Sentinel
Question 11 Topic 4, Case Study 4Case Study Question View Case
HOTSPOT
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: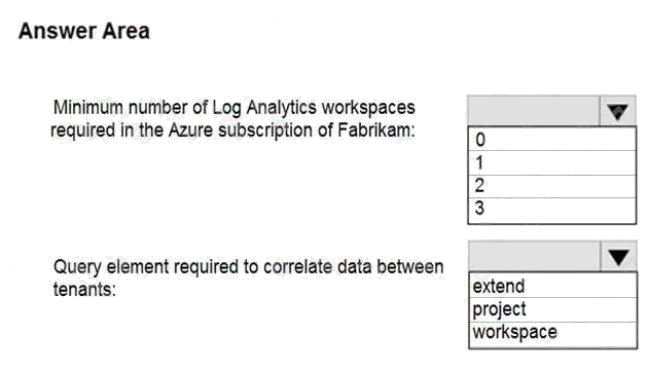
Answer:
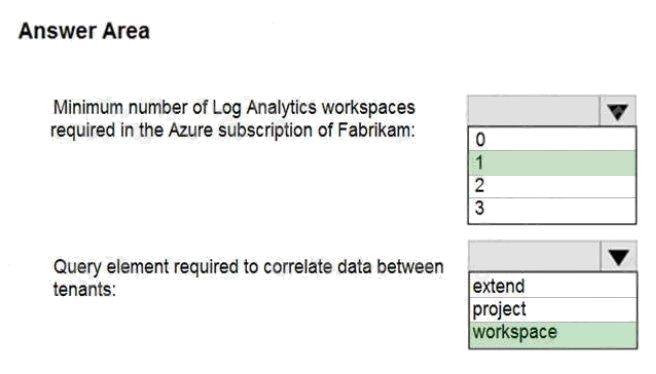
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/extend-sentinel-across-workspaces-tenants
Question 12 Topic 5, Case Study 5Case Study Question View Case
You need to restrict cloud apps running on CLIENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answer present part of the solution.
NOTE: Each correct selection is worth one point.
- A. the Onboarding settings from Device management in Microsoft Defender Security Center
- B. Cloud App Security anomaly detection policies
- C. Advanced features from Settings in Microsoft Defender Security Center
- D. the Cloud Discovery settings in Cloud App Security
Answer:
C D
Explanation:
All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for
Endpoint.
Reference: https://docs.microsoft.com/en-us/cloud-app-security/mde-govern
Question 13 Topic 5, Case Study 5Case Study Question View Case
DRAG DROP
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the
answer area and arrange them in the correct order.
Select and Place: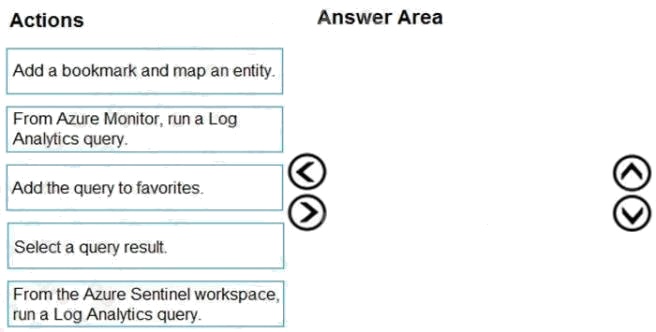
Answer:
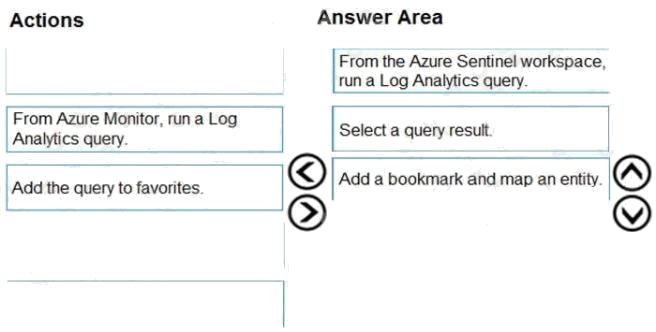
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/bookmarks
Question 14 Topic 5, Case Study 5Case Study Question View Case
HOTSPOT
You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: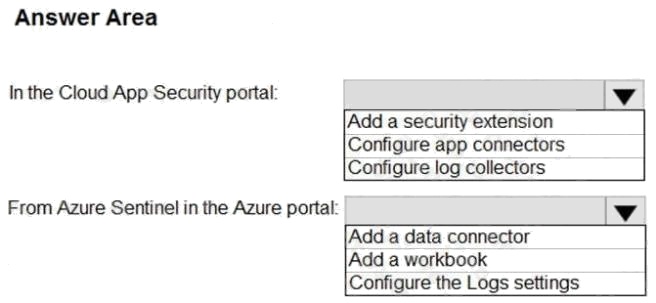
Answer:
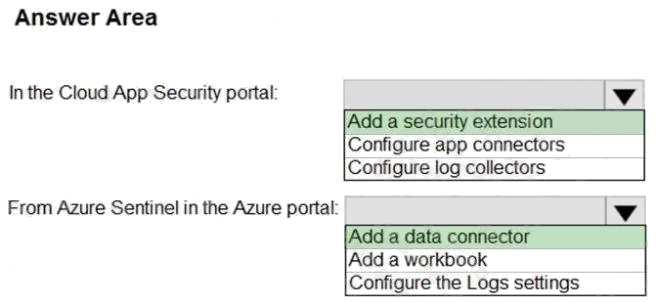
Explanation:
Reference: https://docs.microsoft.com/en-us/cloud-app-security/siem-sentinel
Question 15 Topic 5, Case Study 5Case Study Question View Case
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the
business requirements.
Which role should you assign?
- A. Automation Operator
- B. Automation Runbook Operator
- C. Azure Sentinel Contributor
- D. Azure Sentinel Responder
Answer:
C
Explanation:
Litware must meet the following requirements:
Ensure that a user named admin1 can configure Azure Sentinel playbooks. The principle of least privilege must be used

whenever possible.
Azure Sentinel Contributor can view data, incidents, workbooks, and other Azure Sentinel resources, manage incidents
(assign, dismiss, etc.), create and edit workbooks, analytics rules, and other Azure Sentinel resources.
Reference: https://docs.microsoft.com/en-us/azure/sentinel/roles