microsoft AZ-500 Exam Questions
Questions for the AZ-500 were updated on : Jul 07 ,2025
Page 1 out of 23. Viewing questions 1-15 out of 336
Question 1 Topic 1, Case Study 1Case Study Question View Case
You need to meet the identity and access requirements for Group1.
What should you do?
- A. Add a membership rule to Group1.
- B. Delete Group1. Create a new group named Group1 that has a group type of Microsoft 365. Add users and devices to the group.
- C. Modify the membership rule of Group1.
- D. Change the membership type of Group1 to Assigned. Create two groups that have dynamic memberships. Add the new groups to Group1.
Answer:
D
Explanation:
When you create dynamic groups, they can either contain users or devices. Hence here we need to create two separate
dynamic groups and assign those groups to an Assigned group.
Incorrect Answers:
A, C: You can create a dynamic group for devices or users, but you can't create a rule that contains both users and devices.
Scenario:
Litware identifies the following identity and access requirements: All San Francisco users and their devices must be
members of Group1. The tenant currently contains this group: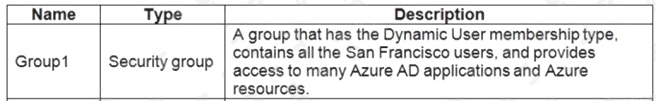
Reference: https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership
https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/active-directory-groups-create-azure-portal
Question 2 Topic 1, Case Study 1Case Study Question View Case
HOTSPOT
You need to ensure that the Azure AD application registration and consent configurations meet the identity and access
requirements.
What should you use in the Azure portal? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: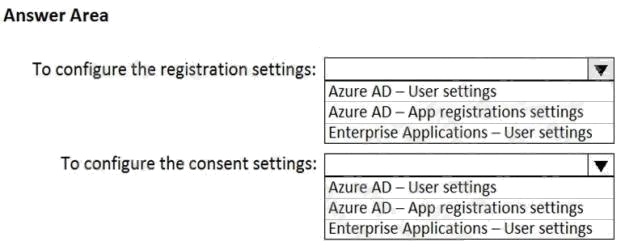
Answer:
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/configure-user-consent
Manage identity and access
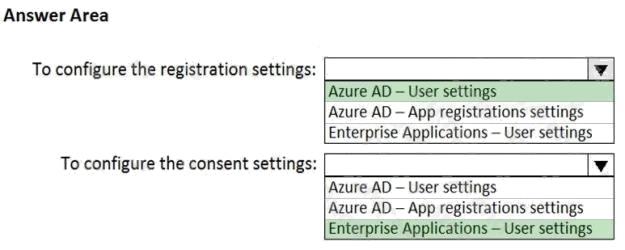
Question 3 Topic 2, Case Study 2Case Study Question View Case
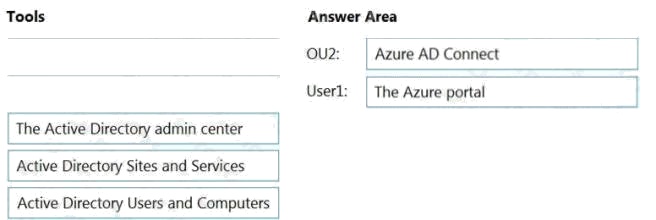
DRAG DROP
You need to perform the planned changes for OU2 and User1.
Which tools should you use? To answer, drag the appropriate tools to the correct resources. Each tool may be used once,
more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place:
Answer:
Question 4 Topic 2, Case Study 2Case Study Question View Case
You need to meet the technical requirements for the finance department users.
Which CAPolicy1 settings should you modify?
- A. Cloud apps or actions
- B. Conditions
- C. Grant
- D. Session
Answer:
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/howto-conditional-access-session-
lifetime
Question 5 Topic 2, Case Study 2Case Study Question View Case
HOTSPOT
You need to delegate the creation of RG2 and the management of permissions for RG1.
Which users can perform each task? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
Answer:
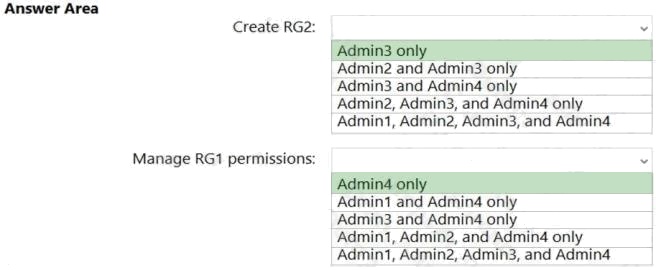
Explanation:
Box 1: Admin3 only
The Contributor role has the necessary write permissions to create the resource group.
Box 2: Admin4 only
You need Owner level access to be able to manage permissions. The Contributor role can do most things but cannot modify
permissions on existing objects.
Question 6 Topic 3, Case Study 3Case Study Question View Case
You plan to configure Azure Disk Encryption for VM4.
Which key vault can you use to store the encryption key?
- A. KeyVault1
- B. KeyVault2
- C. KeyVault3
Answer:
A
Explanation:
The key vault needs to be in the same subscription and same region as the VM.
VM4 is in West US. KeyVault1 is the only key vault in the same region as the VM.
Reference: https://docs.microsoft.com/en-us/azure/virtual-machines/windows/disk-encryption-key-vault
Question 7 Topic 3, Case Study 3Case Study Question View Case
You need to encrypt storage1 to meet the technical requirements.
Which key vaults can you use?
- A. KeyVault2 and KeyVault3 only
- B. KeyVault1 only
- C. KeyVault1 and KeyVault3 only
- D. KeyVault1, KeyVault2, and KeyVault3
Answer:
B
Explanation:
The storage account and the key vault must be in the same region and in the same Azure Active Directory (Azure AD)
tenant, but they can be in different subscriptions. Storage1 is in the West US region. KeyVault1 is the only key vault in the
same region.
Reference: https://docs.microsoft.com/en-us/azure/storage/common/customer-managed-keys-overview
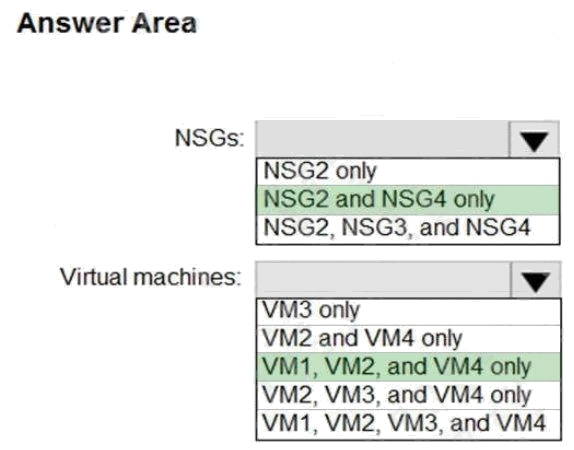
Question 8 Topic 3, Case Study 3Case Study Question View Case
HOTSPOT
You implement the planned changes for ASG1 and ASG2.
In which NSGs can you use ASG1, and the network interfaces of which virtual machines can you assign to ASG2?
Hot Area: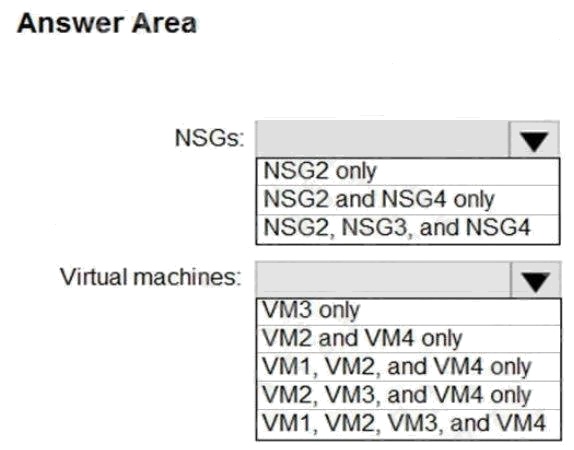
Answer:
Question 9 Topic 3, Case Study 3Case Study Question View Case
You plan to implement JIT VM access.
Which virtual machines will be supported?
- A. VM2, VM3, and VM4 only
- B. VM1, VM2, VM3, and VM4
- C. VM1 and VM3 only
- D. VM1 only
Answer:
C
Question 10 Topic 4, Case Study 4Case Study Question View Case
DRAG DROP
You need to deploy AKS1 to meet the platform protection requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the
answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.
Select and Place: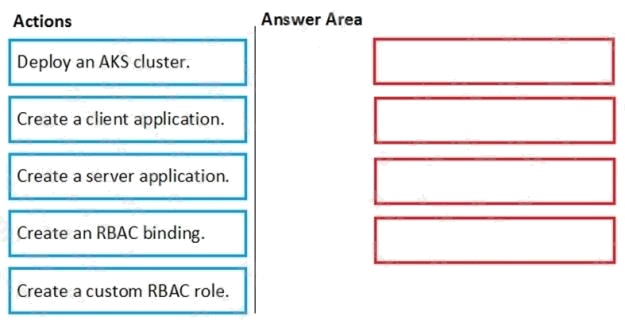
Answer:
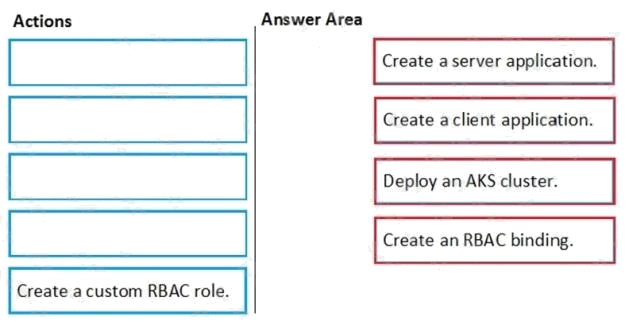
Explanation:
Scenario: Azure AD users must be to authenticate to AKS1 by using their Azure AD credentials. Litewire plans to deploy
AKS1, which is a managed AKS (Azure Kubernetes Services) cluster.
Step 1: Create a server application
To provide Azure AD authentication for an AKS cluster, two Azure AD applications are created. The first application is a
server component that provides user authentication.
Step 2: Create a client application
The second application is a client component that's used when you're prompted by the CLI for authentication. This client
application uses the server application for the actual authentication of the credentials provided by the client.
Step 3: Deploy an AKS cluster.
Use the az group create command to create a resource group for the AKS cluster. Use the az aks create command to deploy
the AKS cluster.
Step 4: Create an RBAC binding.
Before you use an Azure Active Directory account with an AKS cluster, you must create role-binding or cluster role-binding.
Roles define the permissions to grant, and bindings apply them to desired users. These assignments can be applied to a
given namespace, or across the entire cluster.
Reference:
https://docs.microsoft.com/en-us/azure/aks/azure-ad-integration
Question 11 Topic 4, Case Study 4Case Study Question View Case
You need to ensure that users can access VM0. The solution must meet the platform protection requirements.
What should you do?
- A. Move VM0 to Subnet1.
- B. On Firewall, configure a network traffic filtering rule.
- C. Assign RT1 to AzureFirewallSubnet.
- D. On Firewall, configure a DNAT rule.
Answer:
A
Explanation:
Azure Firewall has the following known issue:
Conflict with Azure Security Center (ASC) Just-in-Time (JIT) feature.
If a virtual machine is accessed using JIT, and is in a subnet with a user-defined route that points to Azure Firewall as a
default gateway, ASC JIT doesnt work. This is a result of asymmetric routing a packet comes in via the virtual machine
public IP (JIT opened the access), but the return path is via the firewall, which drops the packet because there is no
established session on the firewall.
Solution: To work around this issue, place the JIT virtual machines on a separate subnet that doesnt have a user-defined
route to the firewall.
Scenario: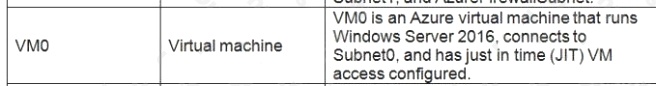
Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.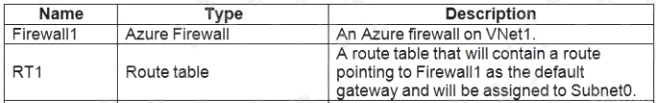
References: https://docs.microsoft.com/en-us/azure/firewall/overview
Question 12 Topic 4, Case Study 4Case Study Question View Case
HOTSPOT
You need to deploy Microsoft Antimalware to meet the platform protection requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: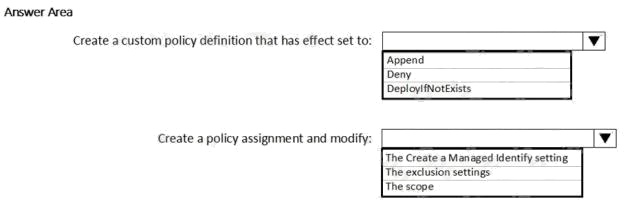
Answer:
Explanation:
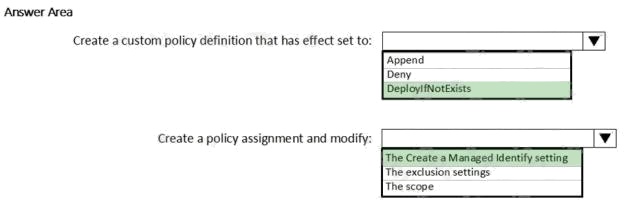
Scenario: Microsoft Antimalware must be installed on the virtual machines in RG1. RG1 is a resource group that contains
Vnet1, VM0, and VM1.
Box 1: DeployIfNotExists
DeployIfNotExists executes a template deployment when the condition is met. Azure policy definition Antimalware
Incorrect Answers:
Append:
Append is used to add additional fields to the requested resource during creation or update. A common example is adding
tags on resources such as costCenter or specifying allowed IPs for a storage resource.
Deny:
Deny is used to prevent a resource request that doesn't match defined standards through a policy definition and fails the
request.
Box 2: The Create a Managed Identity setting
When Azure Policy runs the template in the deployIfNotExists policy definition, it does so using a managed identity. Azure
Policy creates a managed identity for each assignment, but must have details about what roles to grant the managed
identity.
Reference:
https://docs.microsoft.com/en-us/azure/governance/policy/concepts/effects
Implement platform protection
Question 13 Topic 5, Case Study 5Case Study Question View Case
HOTSPOT
What is the membership of Group1 and Group2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: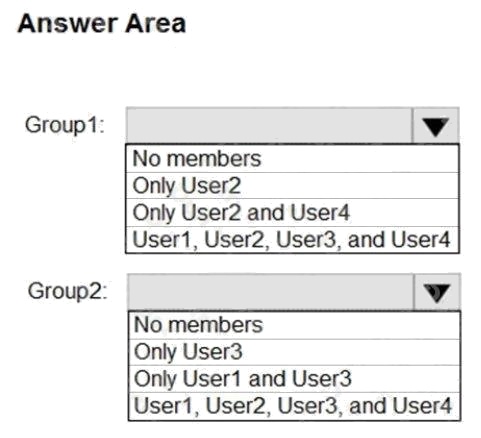
Answer:
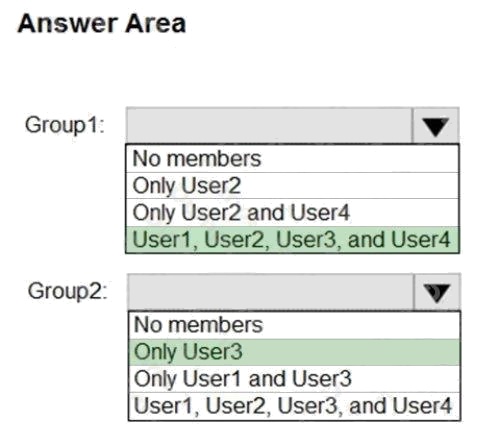
Explanation:
Box 1: User1, User2, User3, User4
Contains "ON" is true for Montreal (User1), MONTREAL (User2), London (User 3), and Ontario (User4) as string and regex
operations are not case sensitive.
Box 2: Only User3
Match "*on" is only true for London (User3) as London is the only word that ends with on.
Scenario:
Contoso.com contains the users shown in the following table.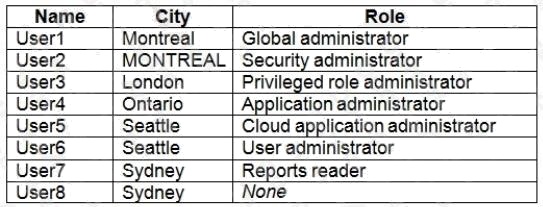
Contoso.com contains the security groups shown in the following table.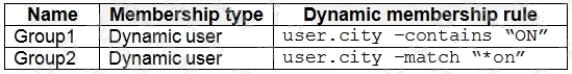
References:
https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership
Question 14 Topic 5, Case Study 5Case Study Question View Case
HOTSPOT
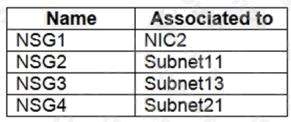
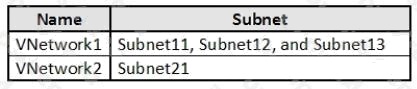
You are evaluating the security of the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area: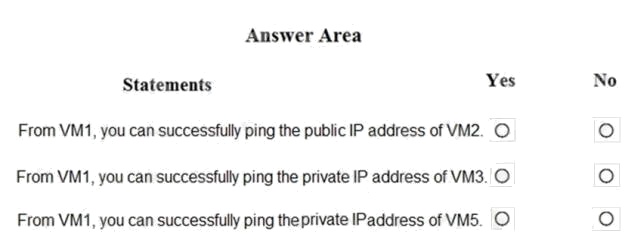
Answer:
Explanation:
Box 1: Yes. All traffic is allowed out to the Internet so you can ping the public IP.
NSG1, NSG2, NSG3, and NSG4 have the outbound security rules shown in the following table.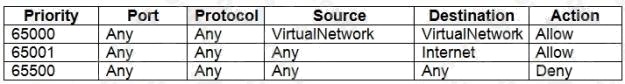
Box 2: Yes. VM3 is on Subnet12. There is no NSG attached to Subnet12 so the traffic will be allowed by default.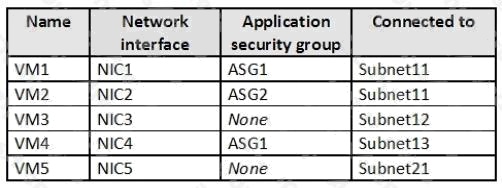
Box 3: No (because VM5 is in a separate VNet).
Note: Sub2 contains the virtual machines shown in the following table.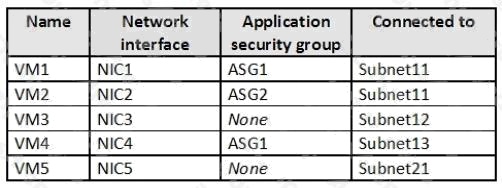
Question 15 Topic 5, Case Study 5Case Study Question View Case
HOTSPOT
You are evaluating the effect of the application security groups on the network communication between the virtual machines
in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area: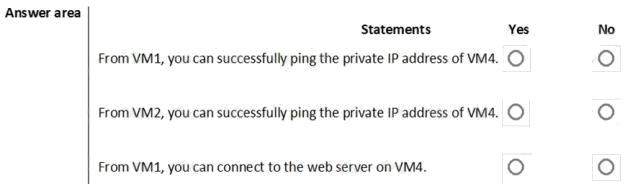
Answer:
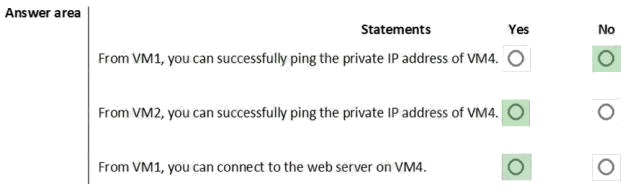
Explanation:
Box 1: No. VM4 is in Subnet13 which has NSG3 attached to it.
VM1 is in ASG1. NSG3 would only allow ICMP pings from ASG2 but not ASG1. Only TCP traffic is allowed from ASG1.
NSG3 has the inbound security rules shown in the following table.
Box 2: Yes.
VM2 is in ASG2. Any protocol is allowed from ASG2 so ICMP ping would be allowed.
Box3. VM1 is in ASG1. TCP traffic is allowed from ASG1 so VM1 could connect to the web server as connections to the web
server would be on ports TCP 80 or TCP 443.