microsoft 98-367 Exam Questions
Questions for the 98-367 were updated on : Jul 07 ,2025
Page 1 out of 12. Viewing questions 1-15 out of 168
Question 1
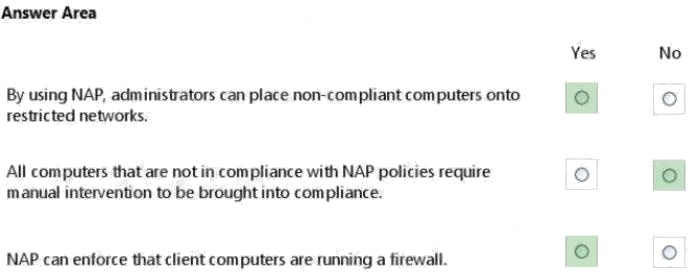
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. Each correct selection is
worth one point.
Hot Area: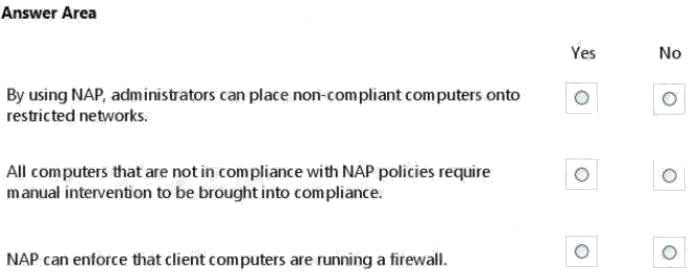
Answer:
Question 2
You are trying to establish communications between a client computer and a server. The server is not responding.
You confirm that both the client and the server have network connectivity.
Which should you check next?
- A. Microsoft Update
- B. Data Execution Prevention
- C. Windows Firewall
- D. Active Directory Domains and Trusts
Answer:
D
Question 3
The process of creating a barrier between domain members and non-domain members by using IPsec policies is referred to
as:
- A. server filtering
- B. domain filtering
- C. domain isolation
- D. server isolation
Answer:
C
Explanation:
References:
https://blogs.msdn.microsoft.com/james_morey/2005/04/21/what-the-heck-is-domain-isolation/
Question 4
Windows Server Update Services (WSUS) is a tool that:
- A. Updates data stored in Windows servers
- B. Manages the services that run on a server
- C. Updates licensing for Windows servers
- D. Manages updates for Microsoft software
Answer:
D
Explanation:
Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft
product updates to computers that are running the Windows operating system. By using WSUS, administrators can fully
manage the distribution of updates that are released through Microsoft Update to computers in their network.
Reference: http://technet.microsoft.com/en-us/windowsserver/bb332157.aspx
Question 5
The Graphic Design Institute hires you to help them set up a server for their 20-person team.
As a general practice of hardening the server, you start by performing which two tasks? (Choose two.)
- A. Disable the guest account.
- B. Rename the admin account.
- C. Remove the account lockout policy.
- D. Format partitions with FAT32.
Answer:
A B
Question 6
You need to grant a set of users write access to a file on a network share. You should add the users to:
- A. A security group
- B. The Authenticated Users group
- C. The Everyone group
- D. A distribution group
Answer:
B
Question 7
You have a Windows 7 desktop computer, and you create a Standard User account for your roommate so that he can use
the desktop from time to time. Your roommate has forgotten his password.
Which two actions can you take to reset the password? (Choose two.)
- A. Use your password reset disk.
- B. Use your administrator account.
- C. Boot into Safe Mode with your roommate's account.
- D. From your roommate's account press CTRL+ALT+DELETE, and then click Change a password.
Answer:
A B
Question 8
Which networking protocol provides centralized authentication, authorization, and accounting?
- A. HTTPS
- B. OpenID
- C. SMTP
- D. RADIUS
Answer:
B
Explanation:
OpenID is an open standard and decentralized authentication protocol.
References:
https://en.wikipedia.org/wiki/OpenID
Question 9
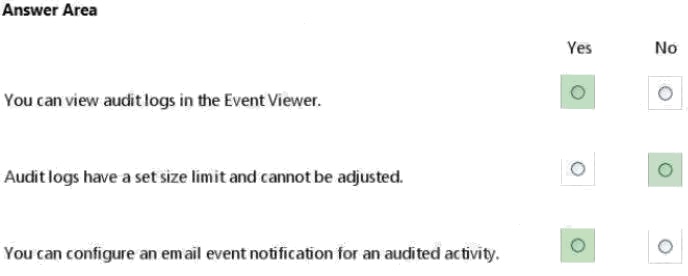
For each of the following statements, select Yes if the statement is true. Otherwise, select No. Each correct selection is
worth one point.
Hot Area: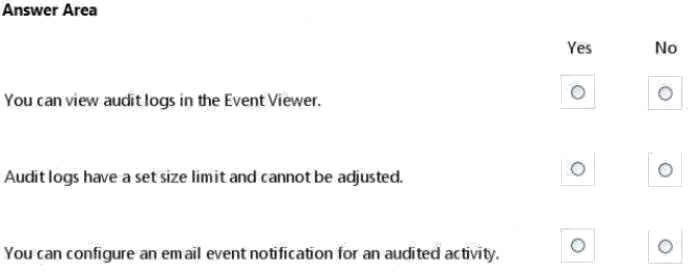
Answer:
Question 10
You create a web server for your school. When users visit your site, they get a certificate error that says your site is not
trusted.
What should you do to fix this problem?
- A. Install a certificate from a trusted Certificate Authority (CA).
- B. Use a digital signature.
- C. Generate a certificate request.
- D. Enable Public Keys on your website.
Answer:
A
Question 11
The certificate of a secure public Web server on the Internet should be:
- A. Issued by a public certificate authority (CA)
- B. Signed by using a 4096-bit key
- C. Signed by using a 1024-bit key
- D. Issued by an enterprise certificate authority (CA)
Answer:
A
Question 12
A user who receives a large number of emails selling prescription medicine is probably receiving pharming mail.
Select the correct answer if the underlined text does not make the statement correct. Select "No change is needed" if the
underlined text makes the statement correct.
- A. Malware
- B. Spoofed mail
- C. Spam
- D. No change is needed.
Answer:
C
Question 13
The WPA2 PreShared Key (PSK) is created by using a passphrase (password) and salting it with the WPS PIN.
Select the correct answer if the underlined text does not make the statement correct. Select "No change is needed" if the
underlined text makes the statement correct.
- A. Service Set Identifier (SSID)
- B. Admin password
- C. WEP key
- D. No change is needed
Answer:
A
Question 14
You have an application that uses IPsec to secure communications between an Internet client and a server on the internal
network.
To which network security service must the IPsec client connect?
- A. SFTP
- B. SSH
- C. VPN
- D. RADIUS
Answer:
C
Question 15
Media Access Control (MAC) filtering enables you to:
- A. limit access to a network based on the client computer’s network adapter.
- B. set access permissions to a shared folder.
- C. prevent communications between specific IP addresses.
- D. restrict communications to a specific website.
Answer:
A