Fortinet NSE7-OTS-7-2 Exam Questions
Questions for the NSE7-OTS-7-2 were updated on : Feb 22 ,2026
Page 1 out of 5. Viewing questions 1-15 out of 69
Question 1
An administrator wants to use FortiSoC and SOAR features on a FortiAnalyzer device to detect and
block any unauthorized access to FortiGate devices in an OT network.
Which two statements about FortiSoC and SOAR features on FortiAnalyzer are true? (Choose two.)
- A. You must set correct operator in event handler to trigger an event.
- B. You can automate SOC tasks through playbooks.
- C. Each playbook can include multiple triggers.
- D. You cannot use Windows and Linux hosts security events with FortiSoC.
Answer:
A,B
Explanation:
Ref: https://docs.fortinet.com/document/fortianalyzer/7.0.0/administration-guide/268882/fortisoc
Question 2
As an OT network administrator, you are managing three FortiGate devices that each protect
different levels on the Purdue model. To increase traffic visibility, you are required to implement
additional security measures to detect exploits that affect PLCs.
Which security sensor must implement to detect these types of industrial exploits?
- A. Intrusion prevention system (IPS)
- B. Deep packet inspection (DPI)
- C. Antivirus inspection
- D. Application control
Answer:
A
Question 3
An OT administrator has configured FSSO and local firewall authentication. A user who is part of a
user group is not prompted from credentials during authentication.
What is a possible reason?
- A. FortiGate determined the user by passive authentication
- B. The user was determined by Security Fabric
- C. Two-factor authentication is not configured with RADIUS authentication method
- D. FortiNAC determined the user by DHCP fingerprint method
Answer:
A
Question 4
Refer to the exhibit.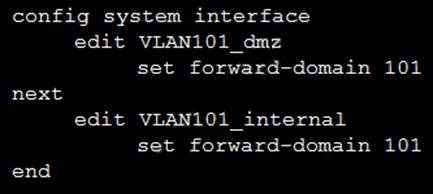
Given the configurations on the FortiGate, which statement is true?
- A. FortiGate is configured with forward-domains to reduce unnecessary traffic.
- B. FortiGate is configured with forward-domains to forward only domain controller traffic.
- C. FortiGate is configured with forward-domains to forward only company domain website traffic.
- D. FortiGate is configured with forward-domains to filter and drop non-domain controller traffic.
Answer:
A
Question 5
Which two statements about the Modbus protocol are true? (Choose two.)
- A. Modbus uses UDP frames to transport MBAP and function codes.
- B. Most of the PLC brands come with a built-in Modbus module.
- C. You can implement Modbus networking settings on internetworking devices.
- D. Modbus is used to establish communication between intelligent devices.
Answer:
B,C
Question 6
Which two statements are true when you deploy FortiGate as an offline IDS? (Choose two.)
- A. FortiGate receives traffic from configured port mirroring.
- B. Network traffic goes through FortiGate.
- C. FortiGate acts as network sensor.
- D. Network attacks can be detected and blocked.
Answer:
B,C
Question 7
Refer to the exhibit, which shows a non-protected OT environment.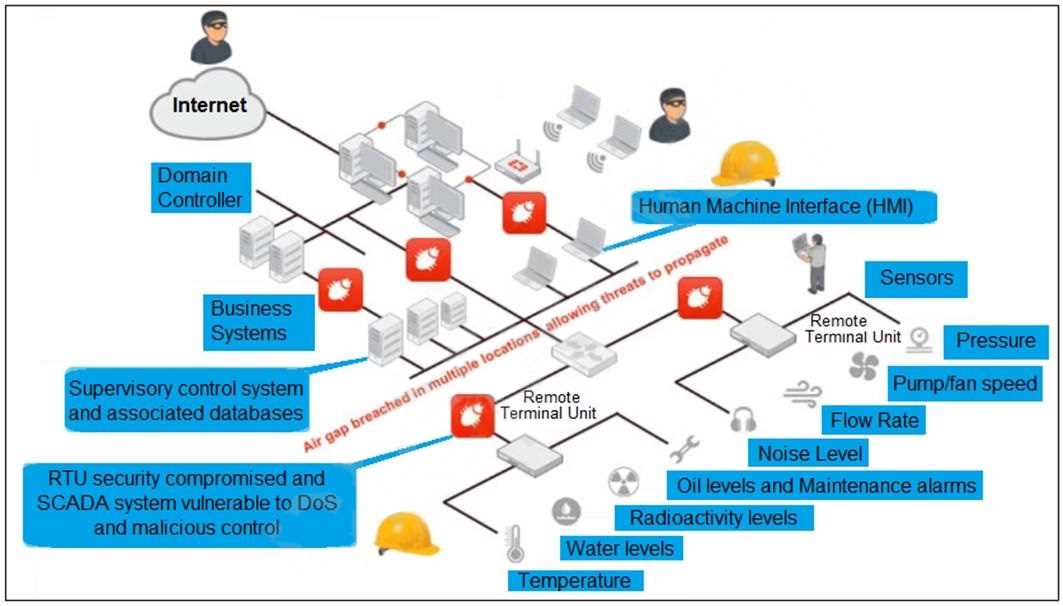
An administrator needs to implement proper protection on the OT network.
Which three steps should an administrator take to protect the OT network? (Choose three.)
- A. Deploy an edge FortiGate between the internet and an OT network as a one-arm sniffer.
- B. Deploy a FortiGate device within each ICS network.
- C. Configure firewall policies with web filter to protect the different ICS networks.
- D. Configure firewall policies with industrial protocol sensors
- E. Use segmentation
Answer:
B, D, E
Question 8
Refer to the exhibit.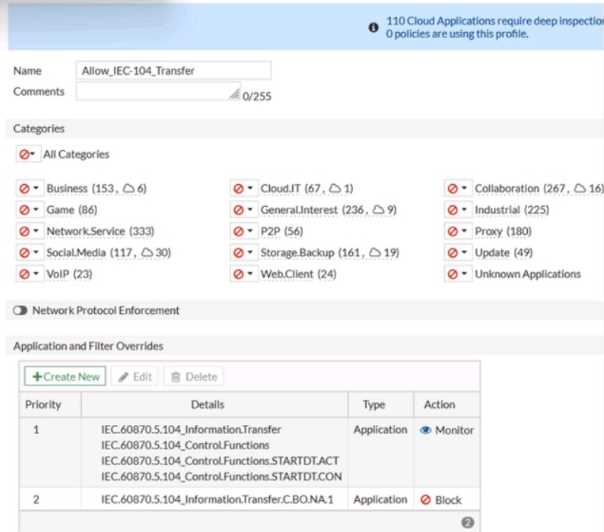
An OT network security audit concluded that the application sensor requires changes to ensure the
correct security action is committed against the overrides filters.
Which change must the OT network administrator make?
- A. Set all application categories to apply default actions.
- B. Change the security action of the industrial category to monitor.
- C. Set the priority of the C.BO.NA.1 signature override to 1.
- D. Remove IEC.60870.5.104 Information.Transfer from the first filter override.
Answer:
D
Explanation:
According to the Fortinet NSE 7 - OT Security 6.4 exam guide1, the application sensor settings allow
you to configure the security action for each application category andnetwork protocol override. The
security action determines how the FortiGate unit handles traffic that matches the application
category or network protocol override. The security action can be one of the following:
Allow: The FortiGate unit allows the traffic without any further inspection.
Monitor: The FortiGate unit allows the traffic and logs it for monitoring purposes.
Block: The FortiGate unit blocks the traffic and logs it as an attack.
The priority of the network protocol override determines the order in which the FortiGate unit
applies the security action to the traffic. The lower the priority number, the higher the priority. For
example, a priority of 1 is higher than a priority of 10.
In the exhibit, the application sensor has the following settings:
The industrial category has a security action of allow, which means that the FortiGate unit will not
inspect or log any traffic that belongs to this category.
The IEC.60870.5.104 Information.Transfer network protocol override has a security action of block,
which means that the FortiGate unit will block and log any traffic that matches this protocol.
The IEC.60870.5.104 Control.Functions network protocol override has a security action of monitor,
which means that the FortiGate unit will allow and log any traffic that matches this protocol.
The IEC.60870.5.104 Start/Stop network protocol override has a security action of allow, which
means that the FortiGate unit will not inspect or log any traffic that matches this protocol.
The IEC.60870.5.104 Transfer.C.BO.NA.1 network protocol override has a security action of block,
which means that the FortiGate unit will block and log any traffic that matches this protocol.
The problem with these settings is that the IEC.60870.5.104 Transfer.C.BO.NA.1 network protocol
override has a lower priority than the IEC.60870.5.104 Information.Transfer network protocol
override. This means that if the traffic matches both protocols, the FortiGate unit will apply the
security action of the higher priority override, which is block. However, the IEC.60870.5.104
Transfer.C.BO.NA.1 protocol is used to transfer binary outputs, which are essential for controlling OT
devices. Therefore, blocking this protocol could have negative consequences for the OT network.
To fix this issue, the OT network administrator must set the priority of the IEC.60870.5.104
Transfer.C.BO.NA.1 network protocol override to 1, which is higher than the priority of the
IEC.60870.5.104 Information.Transfer network protocol override. This way, the FortiGate unit will
apply the security action of the lower priority override, which is allow, to the traffic that matches
both protocols. This will ensure that the FortiGate unit does not block the traffic that is used to
transfer binary outputs, while still blocking the traffic that is used to transfer information.
1: NSE 7 Network Security Architect - Fortinet
Question 9
An OT administrator deployed many devices to secure the OT network. However, the SOC team is
reporting that there are too many alerts, and that many of the alerts are false positive. The OT
administrator would like to find a solution that eliminates repetitive tasks, improves efficiency, saves
time, and saves resources.
Which products should the administrator deploy to address these issues and automate most of the
manual tasks done by the SOC team?
- A. FortiSIEM and FortiManager
- B. FortiSandbox and FortiSIEM
- C. FortiSOAR and FortiSIEM
- D. A syslog server and FortiSIEM
Answer:
C
Question 10
Refer to the exhibit.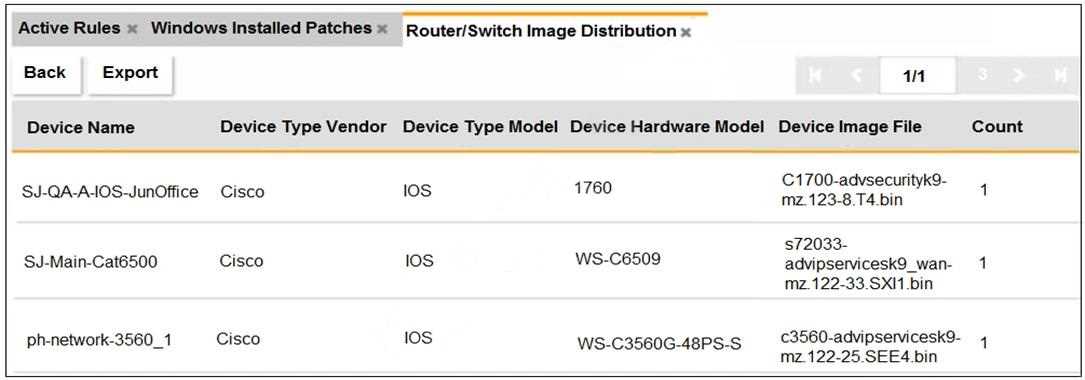
An OT administrator ran a report to identify device inventory in an OT network.
Based on the report results, which report was run?
- A. A FortiSIEM CMDB report
- B. A FortiAnalyzer device report
- C. A FortiSIEM incident report
- D. A FortiSIEM analytics report
Answer:
A
Question 11
An OT supervisor needs to protect their network by implementing security with an industrial
signature database on the FortiGate device.
Which statement about the industrial signature database on FortiGate is true?
- A. A supervisor must purchase an industrial signature database and import it to the FortiGate.
- B. An administrator must create their own database using custom signatures.
- C. By default, the industrial database is enabled.
- D. A supervisor can enable it through the FortiGate CLI.
Answer:
D
Question 12
An OT administrator is defining an incident notification policy using FortiSIEM and would like to
configure the system with a notification policy. If an incident occurs, the administrator would like to
be able to intervene and block an IP address or disable a user in Active Directory from FortiSIEM.
Which step must the administrator take to achieve this task?
- A. Configure a fabric connector with a notification policy on FortiSIEM to connect with FortiGate.
- B. Create a notification policy and define a script/remediation on FortiSIEM.
- C. Define a script/remediation on FortiManager and enable a notification rule on FortiSIEM.
- D. Deploy a mitigation script on Active Directory and create a notification policy on FortiSIEM.
Answer:
B
Explanation:
https://fusecommunity.fortinet.com/blogs/silviu/2022/04/12/fortisiempublishingscript
Question 13
As an OT network administrator you are required to generate reports that primarily use the same
type of data sent to FortiSlEM These reports are based on the preloaded analytic searches
Which two actions can you take on FortiSlEM to enhance running reports for future use? (Choose
two.)
- A. Automate running these reports upon receiving new logs
- B. Export the preloaded analytics searches to an external syslog server
- C. Create custom reports to process additional analytic searches
- D. Save the analytic searches and turn them into report definitions
Answer:
C,D
Question 14
Refer to the exhibit.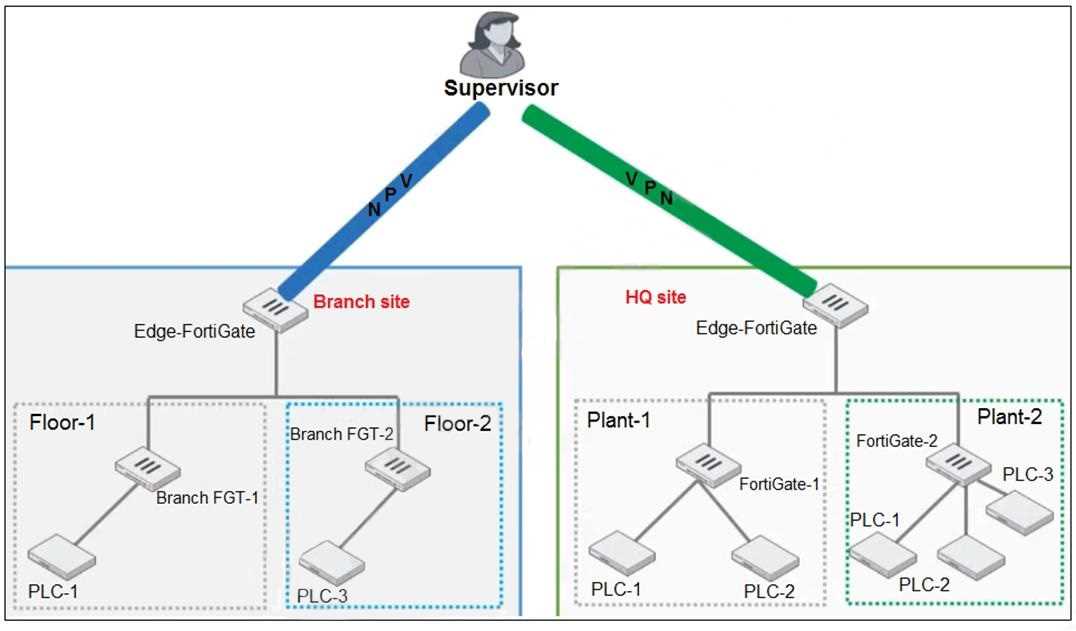
You need to configure VPN user access for supervisors at the breach and HQ sites using the same soft
FortiToken. Each site has a FortiGate VPN gateway.
What must you do to achieve this objective?
- A. You must use a FortiAuthenticator.
- B. You must register the same FortiToken on more than one FortiGate.
- C. You must use the user self-registration server.
- D. You must use a third-party RADIUS OTP server.
Answer:
A
Question 15
An OT architect has deployed a Layer 2 switch in the OT network at Level 1 the Purdue model-process
control. The purpose of the Layer 2 switch is to segment traffic between PLC1 and PLC2 with two
VLANs. All the traffic between PLC1 and PLC2 must first flow through the Layer 2 switch and then
through the FortiGate device in the Level 2 supervisory control network.
What statement about the traffic between PLC1 and PLC2 is true?
- A. The Layer 2 switch rewrites VLAN tags before sending traffic to the FortiGate device.
- B. The Layer 2 switches routes any traffic to the FortiGate device through an Ethernet link.
- C. PLC1 and PLC2 traffic must flow through the Layer-2 switch trunk link to the FortiGate device.
- D. In order to communicate, PLC1 must be in the same VLAN as PLC2.
Answer:
C
Explanation:
The statement that is true about the traffic between PLC1 and PLC2 is that PLC1 and PLC2 traffic must
flow through the Layer-2 switch trunk link to the FortiGate device.