Fortinet NSE6-FWB-6-1 Exam Questions
Questions for the NSE6-FWB-6-1 were updated on : Jun 23 ,2025
Page 1 out of 2. Viewing questions 1-15 out of 30
Question 1
Which two statements about running a vulnerability scan are true? (Choose two.)
- A. You should run the vulnerability scan during a maintenance window.
- B. You should run the vulnerability scan in a test environment.
- C. Vulnerability scanning increases the load on FortiWeb, so it should be avoided.
- D. You should run the vulnerability scan on a live website to get accurate results.
Answer:
A, B
Explanation:
Should the Vulnerability Scanner allow it, SVMS will set the scan schedule (or schedules) to run in a
maintenance window. SVMS will advise Client of the scanners ability to complete the scan(s) within
the maintenance window.
Vulnerabilities on live web sites. Instead, duplicate the web site and its database in a test
environment.
Reference:
https://www.trustwave.com/media/17427/trustwave_mss_managed-3rd-party-
vulnerability-scanning.pdf
https://help.fortinet.com/fweb/552/Content/FortiWeb/fortiweb-admin/vulnerability_scans.htm
Question 2
FortiWeb offers the same load balancing algorithms as FortiGate.
Which two Layer 7 switch methods does FortiWeb also offer? (Choose two.)
- A. Round robin
- B. HTTP session-based round robin
- C. HTTP user-based round robin
- D. HTTP content routes
Answer:
A, D
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.0/administration-
guide/399384/defining-your-web-servers
http://fortinet.globalgate.com.ar/pdfs/FortiWeb/FortiWeb_DS.pdf
Question 3
Which would be a reason to implement HTTP rewriting?
- A. The original page has moved to a new URL
- B. To replace a vulnerable function in the requested URL
- C. To send the request to secure channel
- D. The original page has moved to a new IP address
Answer:
A
Explanation:
Create a new URL rewriting rule.
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.0/administration-
guide/961303/rewriting-redirecting
Question 4
Refer to the exhibit.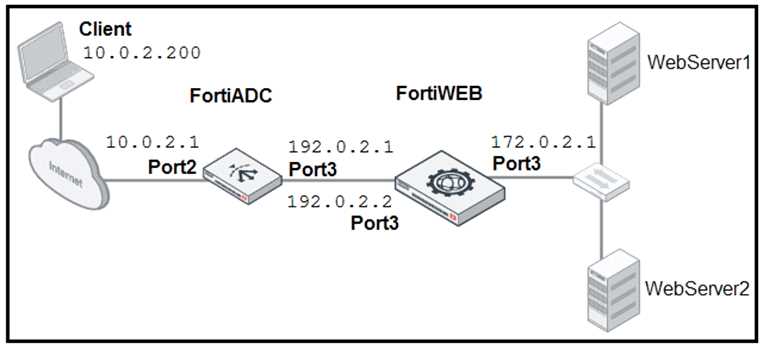
FortiADC is applying SNAT to all inbound traffic going to the servers. When an attack occurs, FortiWeb
blocks traffic based on the 192.0.2.1 source IP address, which belongs to FortiADC. The setup is
breaking all connectivity and genuine clients are not able to access the servers.
What must the administrator do to avoid this problem? (Choose two.)
- A. Enable the Use X-Forwarded-For setting on FortiWeb.
- B. No Special configuration is required; connectivity will be re-established after the set timeout.
- C. Place FortiWeb in front of FortiADC.
- D. Enable the Add X-Forwarded-For setting on FortiWeb.
Answer:
A, D
Explanation:
Configure your load balancer to insert or append to anX-Forwarded-For:,X-Real-IP:, or other HTTP X-
header. Also configureFortiWebto find the original attackers or clients IP address in that HTTP
header
Reference:
https://help.fortinet.com/fweb/560/Content/FortiWeb/fortiweb-
admin/planning_topology.htm
Question 5
Which statement about local user accounts is true?
- A. They are best suited for large environments with many users.
- B. They cannot be used for site publishing.
- C. They must be assigned, regardless of any other authentication.
- D. They can be used for SSO.
Answer:
D
Explanation:
You can configure the Remedy Single Sign-On server to authenticate TrueSight Capacity Optimization
users as local users.
Reference:
https://docs.bmc.com/docs/TSCapacity/110/setting-up-local-user-authentication-in-remedy-sso-743238341.html
Question 6
Refer to the exhibit.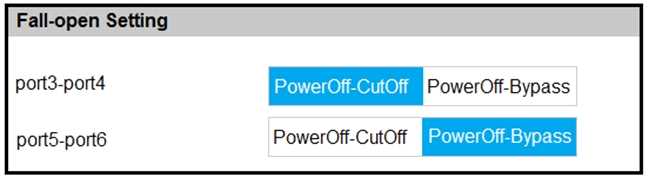
Based on the configuration, what would happen if this FortiWeb were to lose power? (Choose two.)
- A. Traffic that passes between port5 and port6 will be inspected.
- B. Traffic will be interrupted between port3 and port4.
- C. All traffic will be interrupted.
- D. Traffic will pass between port5 and port6 uninspected.
Answer:
B, D
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.10/administration-guide/33485/fail-
to-wire-for-power-loss-reboots
Question 7
Refer to the exhibit.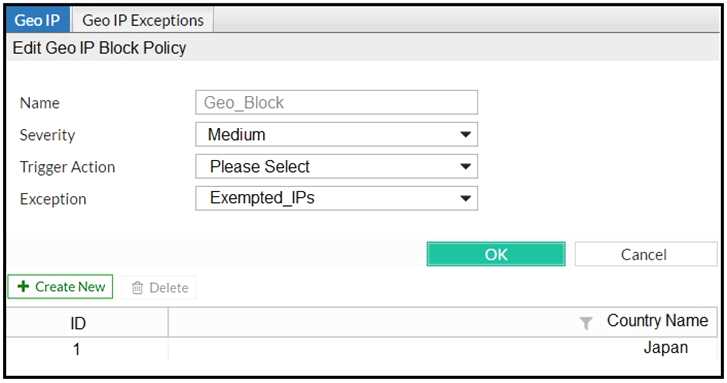
FortiWeb is configured to block traffic from Japan to your web application server. However, in the
logs, the administrator is seeing traffic allowed from one particular IP address which is geo-located in
Japan.
What can the administrator do to solve this problem? (Choose two.)
- A. Manually update the geo-location IP addresses for Japan.
- B. If the IP address is configured as a geo reputation exception, remove it.
- C. Configure the IP address as a blacklisted IP address.
- D. If the IP address is configured as an IP reputation exception, remove it.
Answer:
A, C
Explanation:
IP reputation leverages many techniques for accurate, early, and frequently updated identification of
compromised and malicious clients so you can block attackersbeforethey target your servers.
IP blacklisting is a method used to filter out illegitimate ormalicious IP addresses from accessing
your networks. Blacklists are lists containing ranges of or individual IP addresses that you want to
block.
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.5/administration-
guide/137271/blacklisting-whitelisting-clients
https://www.imperva.com/learn/application-security/ip-blacklist/
Question 8
Which algorithm is used to build mathematical models for bot detection?
- A. HCM
- B. SVN
- C. SVM
- D. HMM
Answer:
C
Explanation:
FortiWeb uses SVM (Support Vector Machine) algorithm to build up the bot detection model
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.7/administration-
guide/193258/machine-learning
Question 9
A client is trying to start a session from a page that would normally be accessible only after the client
has logged in.
When a start page rule detects the invalid session access, what can FortiWeb do? (Choose three.)
- A. Display an access policy message, then allow the client to continue
- B. Redirect the client to the login page
- C. Allow the page access, but log the violation
- D. Prompt the client to authenticate
- E. Reply with a 403 Forbidden HTTP error
Answer:
B, C, E
Reference:
https://help.fortinet.com/fweb/607/Content/FortiWeb/fortiweb-
admin/specify_urls_to_initiate.htm
Question 10
Refer to the exhibit.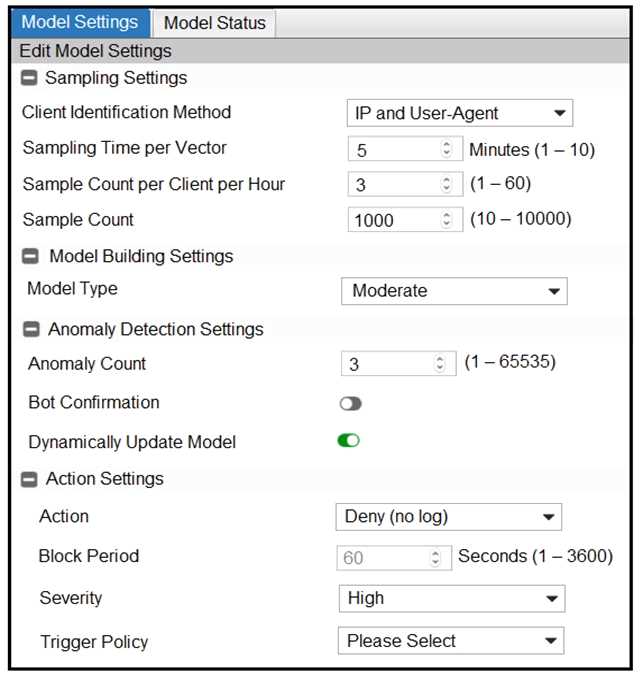
Many legitimate users are being identified as bots. FortiWeb bot detection has been configured with
the settings shown in the exhibit. The FortiWeb administrator has already verified that the current
model is accurate.
What can the administrator do to fix this problem, making sure that real bots are not allowed
through FortiWeb?
- A. Change Model Type to Strict
- B. Change Action under Action Settings to Alert
- C. Disable Dynamically Update Model
- D. Enable Bot Confirmation
Answer:
D
Explanation:
Bot Confirmation
If the number of anomalies from a user has reached theAnomaly Count, the system executesBot
Confirmationbefore taking actions.
TheBot Confirmationis to confirm if the user is indeed a bot. The system sends RBE (Real Browser
Enforcement) JavaScript or CAPTCHA to the client to double check if it's a real bot.
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.1/administration-
guide/600188/configuring-bot-detection-profiles
Question 11
What can an administrator do if a client has been incorrectly period blocked?
- A. Nothing, it is not possible to override a period block.
- B. Manually release the ID address from the temporary blacklist.
- C. Force a new IP address to the client.
- D. Disconnect the client from the network.
Answer:
B
Explanation:
Block Period
Enter the number of seconds that you want to block the requests. The valid range is 13,600
seconds. The default value is 60 seconds.
This option only takes effect when you choosePeriod BlockinAction.
Note: Thats a temporary blacklist so you can manually release them from the blacklist.
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.1/administration-
guide/600188/configuring-bot-detection-profiles
Question 12
Which regex expression is the correct format for redirecting the URL
http://www.example.com
?
- A. www\.example\.com B. www.example.com
- C. www\example\com
- D. www/.example/.com
Answer:
B
Explanation:
\1://www.company.com/\2/\3
Reference:
https://learn.akamai.com/en-us/webhelp/edge-redirector/edge-redirector-guide/GUID-0C22DFC2-DCC4-42AF-BDB2-9537FBEE03FD.html
Question 13
When FortiWeb triggers a redirect action, which two HTTP codes does it send to the client to inform
the browser of the new URL? (Choose two.)
- A. 403
- B. 302
- C. 301
- D. 404
Answer:
B, C
Reference:
https://developer.mozilla.org/en-US/docs/Web/HTTP/Status/302
Question 14
True transparent proxy mode is best suited for use in which type of environment?
- A. New networks where infrastructure is not yet defined
- B. Flexible environments where you can easily change the IP addressing scheme
- C. Small office to home office environments
- D. Environments where you cannot change the IP addressing scheme
Answer:
D
Explanation:
Does not require changes to the IP address scheme of the network. Requests are destined for a web
server and not theFortiWebappliance. This operation mode supports the same feature set as True
Transparent Proxy mode.
Reference:
https://docs.fortinet.com/document/fortiweb/6.3.0/administration-
guide/211763/planning-the-network-topology
Question 15
Review the following configuration: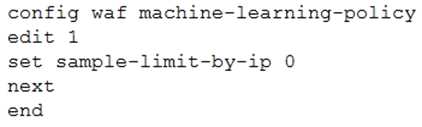
What is the expected result of this configuration setting?
- A. When machine learning (ML) is in its collecting phase, FortiWeb will accept an unlimited number of samples from the same source IP address.
- B. When machine learning (ML) is in its running phase, FortiWeb will accept an unlimited number of samples from the same source IP address.
- C. When machine learning (ML) is in its collecting phase, FortiWeb will not accept any samples from any source IP addresses.
- D. When machine learning (ML) is in its running phase, FortiWeb will accept a set number of samples from the same source IP address.
Answer:
A