Fortinet NSE6-FNC-8-5 Exam Questions
Questions for the NSE6-FNC-8-5 were updated on : Feb 22 ,2026
Page 1 out of 2. Viewing questions 1-15 out of 30
Question 1
What causes a host's state to change to "at risk"?
- A. The host has failed an endpoint compliance policy or admin scan.
- B. The logged on user is not found in the Active Directory.
- C. The host has been administratively disabled.
- D. The host is not in the Registered Hosts group.
Answer:
A
Explanation:
Failure – Indicates that the host has failed the scan. This option can also be set manually. When the
status is set to Failure the host is marked "At Risk" for the selected scan.
Reference:
https://docs.fortinet.com/document/fortinac/8.3.0/administration-guide/241168/host-
health-and-scanning
Question 2
By default, if more than 20 hosts are seen connected on a single port simultaneously, what will
happen to the port?
- A. The port is switched into the Dead-End VLAN.
- B. The port becomes a threshold uplink.
- C. The port is disabled.
- D. The port is added to the Forced Registration group.
Answer:
B
Question 3
When you create a user or host profile, which three criteria can you use? (Choose three.)
- A. An applied access policy
- B. Host or user attributes
- C. Administrative group membership
- D. Location
- E. Host or user group memberships
Answer:
ABD
Reference:
https://docs.fortinet.com/document/fortinac/8.3.0/administration-guide/15797/user-
host-profiles
Question 4
Which two methods can be used to gather a list of installed applications and application details from
a host? (Choose two)
- A. Portal page on-boarding options
- B. Application layer traffic inspection
- C. Agent technology
- D. MDM integration
Answer:
AD
Reference:
https://developer.apple.com/business/documentation/MDM-Protocol-Reference.pdf
https://docs.oracle.com/en/middleware/idm/identity-governance/12.2.1.3/omusg/managing-application-onboarding.html#GUID-4D0D5B18-A6F5-4231-852E-DB0D95AAE2D1
Question 5
How are logical networks assigned to endpoints?
- A. Through device profiling rules
- B. Through network access policies
- C. Through Layer 3 polling configurations
- D. Through FortiGate IPv4 policies
Answer:
D
Reference:
https://docs.fortinet.com/document/fortigate/6.2.0/cookbook/9819/viewing-and-
controlling-network-risks-via-topology-view
Question 6
In a wireless integration, how does FortiNAC obtain connecting MAC address information?
- A. MAC notification traps
- B. Link traps
- C. End station traffic monitoring
- D. RADIUS
Answer:
D
Explanation:
Intelligent Access Points (IAPs) and controllers support two methods of RADIUS based
authentication: RADIUS MAC authentication and 802.1x authentication.
Reference:
https://fortinetweb.s3.amazonaws.com/docs.fortinet.com/v2/attachments/9019f7f8-
200d-11e9-b6f6-f8bc1258b856/FortiNAC_Wireless_Integration_Overview.pdf
Question 7
Which three circumstances trigger Layer 2 polling of infrastructure devices? (Choose three.)
- A. Manual polling
- B. Scheduled poll timings
- C. A failed Layer 3 poll
- D. A matched security policy
- E. Linkup and Linkdown traps
Answer:
ABE
Question 8
In an isolation VLAN. which three services does FortiNAC supply? (Choose three.)
- A. NTP
- B. SMTP
- C. DHCP
- D. DNS
- E. Web
Answer:
CDE
Reference:
https://fortinetweb.s3.amazonaws.com/docs.fortinet.com/v2/attachments/8bec453a-
b242-11e9-a989-00505692583a/AdminGuide-860-PDF.pdf
Question 9
With enforcement for network access policies and at-risk hosts enabled, what will happen if a host
matches a network access policy and has a state of "at risk"?
- A. The host is provisioned based on the default access defined by the point of connection.
- B. The host is provisioned based on the network access policy.
- C. The host is isolated.
- D. The host is administratively disabled.
Answer:
B
Reference:
https://docs.fortinet.com/document/fortinac/8.6.0/administration-guide/49701/policy-
assignment
Question 10
Which agent can receive and display messages from FortiNAC to the end user?
- A. Persistent
- B. MDM
- C. Passive
- D. Dissolvable
Answer:
C
Reference:
https://docs.fortinet.com/document/fortinac/8.7.0/administration-guide/594507/agent-
packages
Question 11
Refer to the exhibit, and then answer the question below.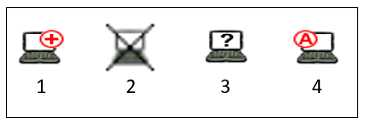
Which host is rogue?
- A. 1
- B. 3
- C. 2
- D. 4
Answer:
B
Reference:
https://docs.fortinet.com/document/fortinac/8.6.0/administration-
guide/283146/evaluating-rogue-hosts
Question 12
What capability do logical networks provide?
- A. VLAN-based inventory reporting
- B. Application of different access values from a single access policy
- C. Autopopulation of device groups based on point of connection
- D. Interactive topology view diagrams
Answer:
A
Explanation:
NTM also includes reporting utilities such as network and inventory reports. You can generate
reports for subnets, switch ports, and VLANs.
Reference:
https://logicalread.com/network-diagram/#.YBk9ZOgzbIU
Question 13
Where do you look to determine when and why the FortiNAC made an automated network access
change?
- A. The Event view
- B. The Port Changes view
- C. The Connections view
- D. The Admin Auditing view
Answer:
B
Reference:
https://docs.fortinet.com/document/fortigate/6.2.3/cookbook/536166/viewing-event-
logs
Question 14
Which command line shell and scripting language does FortiNAC use for WinRM?
- A. Linux
- B. Bash
- C. DOS
- D. Powershell
Answer:
D
Explanation:
Open Windows PowerShell or a command prompt. Run the following command to determine if you
already have WinRM over HTTPS configured.
Reference:
https://docs.fortinet.com/document/fortinac/8.7.0/administration-guide/246310/winrm-
device-profile-requirements-and-setup
Question 15
What would happen if a port was placed in both the Forced Registration and the Forced Remediation
port groups?
- A. Only rogue hosts would be impacted.
- B. Both enforcement groups cannot contain the same port.
- C. Only al-risk hosts would be impacted.
- D. Both types of enforcement would be applied.
Answer:
B
Reference:
https://docs.fortinet.com/document/fortinac/8.3.0/administration-
guide/837785/system-groups