Fortinet NSE6-FNC-7-2 Exam Questions
Questions for the NSE6-FNC-7-2 were updated on : Feb 22 ,2026
Page 1 out of 4. Viewing questions 1-15 out of 57
Question 1
When configuring isolation networks in the configuration wizard, why does a Layer 3 network type
allow for more than one DHCP scope for each isolation network type?
- A. There can be more than one isolation network of each type.
- B. Any scopes beyond the first scope are used if the Initial scope runs out of IP addresses.
- C. Configuring more than one DHCP scope allows for DHCP server redundancy.
- D. The Layer 3 network type allows for one scope for each possible host status.
Answer:
A
Question 2
During an evaluation of state-based enforcement, an administrator discovers that ports that should
not be under enforcement have been added to enforcement groups. In which view would the
administrator be able to determine who added the ports to the groups?
- A. The Alarms view
- B. The Admin Auditing view
- C. The Event Management view
- D. The Security Events view
Answer:
B
Question 3
Refer to the exhibit.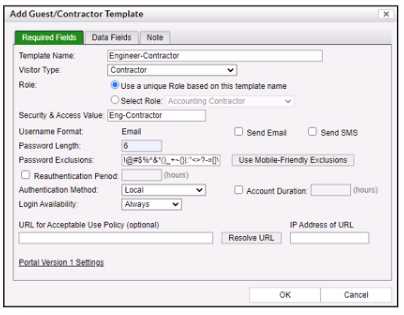
When a contractor account is created using this template, what value will be set in the accounts Rote
field?
- A. Accounting Contractor
- B. Eng-Contractor
- C. Engineer-Contractor
- D. Conti actor
Answer:
C
Question 4
Which three capabilities does FortiNAC Control Manager provide? (Choose three.)
- A. Global visibility
- B. Global authentication security policies
- C. Global infrastructure device inventory
- D. Global version control
- E. Pooled licenses
Answer:
A, D, E
Question 5
When FortiNAC is managing VPN clients connecting through FortiGate. why must the clients run a
FortiNAC agent?
- A. To collect user authentication details
- B. To meet the client security profile rule for scanning connecting clients
- C. To collect the client IP address and MAC address
- D. To transparently update the client IP address upon successful authentication
Answer:
B
Question 6
Two FortiNAC devices have been configured in an HA configuration. After five failed heartbeats
between the primary device and secondary device, the primary device fail to ping the designated
gateway. What happens next?
- A. The primary device continues to operate as the in-control device and changes the status or secondary device to contact lost.
- B. The primary device changes its designation to secondary, and the secondary device changes to primary.
- C. The primary device shuts down NAC processes and changes to a management down status.
- D. The primary device waits 3 minutes and attempts to re-establish the HA heartbeat before attempting a second ping of the gateway.
Answer:
C
Question 7
How does FortiGate update FortiNAC about VPN session information?
- A. API calls to FortiNAC
- B. Syslog messages
- C. SNMP traps
- D. Security Fabric Integration
Answer:
B
Question 8
View the output.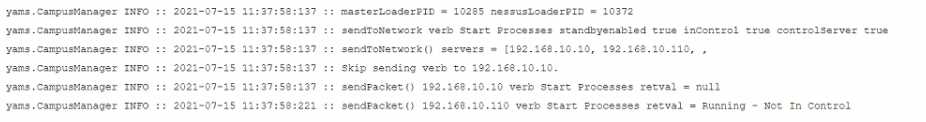
Examine the communication between a primary FortiNAC (192.168.10.10) and a secondary FortiNAC
(192.166.10.110) configured as an HA pair What is the current state of the FortiNAC HA pair?
- A. The primary server Is running and in control.
- B. The database replication failed.
- C. The secondary server is running and in control.
- D. Fallover from the primary server to the secondary server is in progress.
Answer:
A
Question 9
What method of communication does FortiNAC use to control VPN host access on FortiGate?
- A. RSSO
- B. Security Fabric
- C. RADIUS accounting
- D. SAMLSSO
Answer:
B
Question 10
Which two are required for endpoint compliance monitors? (Choose two.}
- A. Custom scan
- B. ZTNA agent
- C. Persistent agent
- D. MDM integration
Answer:
A, C
Question 11
What causes a host's state to change to "at risk"?
- A. The host has failed an endpoint compliance policy or admin scan.
- B. The logged on user is not found in the Active Directory.
- C. The host has been administratively disabled.
- D. The host is not in the Registered Hosts group.
Answer:
A
Explanation:
Failure – Indicates that the host has failed the scan. This option can also be set manually. When the
status is set to Failure the host is marked "At Risk" for the selected scan.
Reference:
https://docs.fortinet.com/document/fortinac/8.3.0/administration-guide/241168/host-
health-and-scanning
p. 244 of the Study Guide, "A state of at-risk indicates the host has failed a scan. This could be a
compliance scan or an administrative scan."
Question 12
By default, if more than 20 hosts are seen connected on a single port simultaneously, what will
happen to the port?
- A. The port is switched into the Dead-End VLAN.
- B. The port becomes a threshold uplink.
- C. The port is disabled.
- D. The port is added to the Forced Registration group.
Answer:
B
Explanation:
Admin Guide p. 754: Threshold Uplink—The Uplink mode has been set as Dynamic and FortiNAC has
determined that the number of MAC addresses on the port exceeds the System Defined Uplink
count. All hosts read on this port are ignored.
Question 13
When you create a user or host profile; which three criteria can you use? (Choose three.)
- A. An applied access policy
- B. Administrative group membership
- C. Location
- D. Host or user group memberships
- E. Host or user attributes
Answer:
CDE
Explanation:
Fortinac-admin-operations, P. 391
Question 14
Which three circumstances trigger Layer 2 polling of infrastructure devices? (Choose three.)
- A. Manual polling
- B. Scheduled poll timings
- C. A failed Layer 3 poll
- D. A matched security policy
- E. Linkup and Linkdown traps
Answer:
ABE
Explanation:
A . Manual Polling: This is when an administrator or network operator initiates a poll manually to
gather information or check the status of the network devices. This can be done for immediate
troubleshooting or assessment.
B . Scheduled Poll Timings: Network management systems often have the capability to schedule
regular polls of devices to check their status or monitor their performance. These scheduled polls can
be set at regular intervals (such as every few minutes, hours, or daily) depending on the
requirements of the network.
E . Linkup and Linkdown Traps: SNMP (Simple Network Management Protocol) traps, like Linkup and
Linkdown, are automated notifications sent from network devices to a management system. A
Linkup trap indicates that a particular interface has become active (up), while a Linkdown trap
indicates that an interface has become inactive (down). These traps can trigger Layer 2 polling to
ascertain the current status of network interfaces and devices.
Question 15
With enforcement for network access policies and at-risk hosts enabled, what will happen if a host
matches a network access policy and has a state of "at risk"?
- A. The host is provisioned based on the default access defined by the point of connection.
- B. The host is provisioned based on the network access policy.
- C. The host is isolated.
- D. The host is administratively disabled.
Answer:
C
Explanation:
https://training.fortinet.com/pluginfile.php/1912463/mod_resource/content/26/FortiNAC_7.2_Stud
y_Guide-Online.pdf C. Page 327 - moved to the quarantine isolation network