Fortinet NSE5-EDR-5-0 Exam Questions
Questions for the NSE5-EDR-5-0 were updated on : Feb 22 ,2026
Page 1 out of 2. Viewing questions 1-15 out of 30
Question 1
Which two statements about the FortiEDR solution are true? (Choose two.)
- A. It provides pre-infection and post-infection protection
- B. It is Windows OS only
- C. It provides central management
- D. It provides pant-to-point protection
Answer:
A, D
Question 2
Which security policy has all of its rules disabled by default?
- A. Device Control
- B. Ransomware Prevention
- C. Execution Prevention
- D. Exfiltration Prevention
Answer:
B
Question 3
Which FortiEDR component is required to find malicious files on the entire network of an
organization?
- A. FortiEDR Aggregator
- B. FortiEDR Central Manager
- C. FortiEDR Threat Hunting Repository
- D. FortiEDR Core
Answer:
A
Question 4
Which scripting language is supported by the FortiEDR action managed?
- A. TCL
- B. Python
- C. Perl
- D. Bash
Answer:
A
Question 5
A FortiEDR security event is causing a performance issue with a third-parry application. What must
you do first about the event?
- A. Contact Fortinet support
- B. Terminate the process and uninstall the third-party application
- C. Immediately create an exception
- D. Investigate the event to verify whether or not the application is safe
Answer:
C
Question 6
An administrator finds a third party free software on a user's computer mat does not appear in me
application list in the communication control console
Which two statements are true about this situation? (Choose two)
- A. The application is allowed in all communication control policies
- B. The application is ignored as the reputation score is acceptable by the security policy
- C. The application has not made any connection attempts
- D. The application is blocked by the security policies
Answer:
A, D
Question 7
Refer to the exhibit.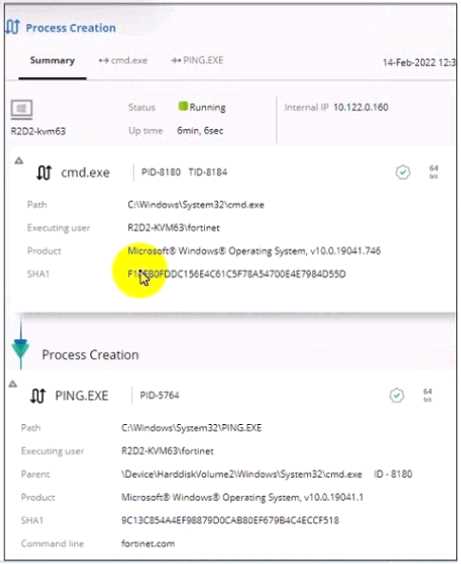
Based on the threat hunting event details shown in the exhibit, which two statements about the
event are true? (Choose two.)
- A. The PING EXE process was blocked
- B. The user fortinet has executed a ping command
- C. The activity event is associated with the file action
- D. There are no MITRE details available for this event
Answer:
A, D
Question 8
What is the role of a collector in the communication control policy?
- A. A collector blocks unsafe applications from running
- B. A collector is used to change the reputation score of any application that collector runs
- C. A collector records applications that communicate externally
- D. A collector can quarantine unsafe applications from communicating
Answer:
A
Question 9
Refer to the exhibit.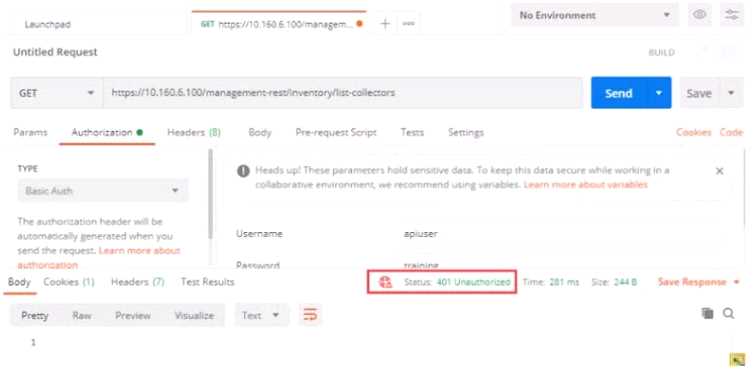
Based on the postman output shown in the exhibit why is the user getting an unauthorized error?
- A. The user has been assigned Admin and Rest API roles
- B. FortiEDR requires a password reset the first time a user logs in
- C. Postman cannot reach the central manager
- D. API access is disabled on the central manager
Answer:
A
Question 10
FortiXDR relies on which feature as part of its automated extended response?
- A. Playbooks
- B. Security Policies
- C. Forensic
- D. Communication Control
Answer:
B
Question 11
Which two types of remote authentication does the FortiEDR management console support?
(Choose two.)
- A. Radius
- B. SAML
- C. TACACS
- D. LDAP
Answer:
A, D
Question 12
Which threat hunting profile is the most resource intensive?
- A. Comprehensive
- B. Inventory
- C. Default
- D. Standard Collection
Answer:
A
Question 13
The FortiEDR axe classified an event as inconclusive, out a few seconds later FCS revised the
classification to malicious. What playbook actions ate applied to the event?
- A. Playbook actions applied to inconclusive events
- B. Playbook actions applied to handled events
- C. Playbook actions applied to suspicious events
- D. Playbook actions applied to malicious events
Answer:
D
Question 14
Exhibit.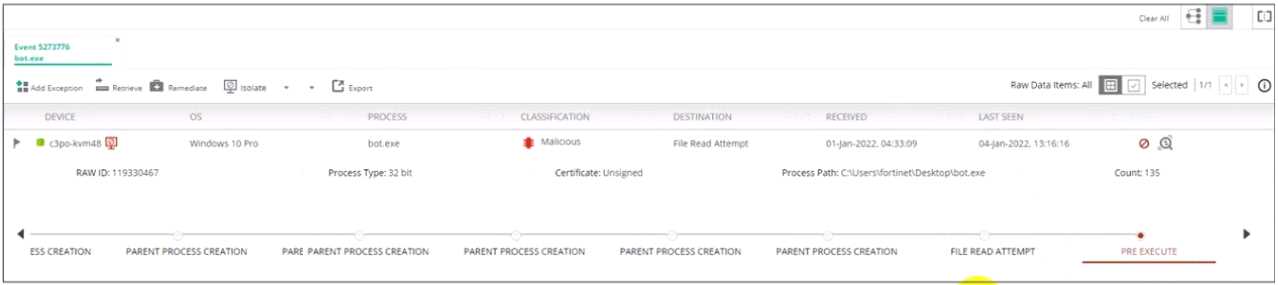
Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)
- A. An exception has been created for this event
- B. The forensics data is displayed m the stacks view
- C. The device has been isolated
- D. The exfiltration prevention policy has blocked this event
Answer:
C, D
Question 15
Which two statements are true about the remediation function in the threat hunting module?
(Choose two.)
- A. The file is removed from the affected collectors
- B. The threat hunting module sends the user a notification to delete the file
- C. The file is quarantined
- D. The threat hunting module deletes files from collectors that are currently online.
Answer:
B, C