Fortinet FCSS SDW AR 7 4 Exam Questions
Questions for the FCSS SDW AR 7 4 were updated on : Feb 22 ,2026
Page 1 out of 5. Viewing questions 1-15 out of 68
Question 1
Refer to the exhibits.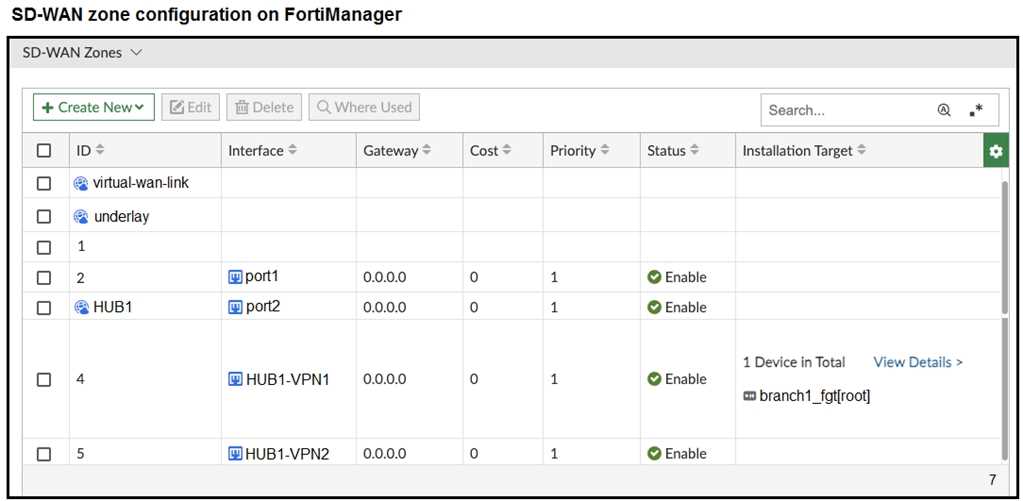
The exhibits show the SD-WAN zone configuration of an SD-WAN template prepared on
FortiManager and the policy package configuration.
When the administrator tries to install the configuration changes, FortiManager fails to commit.
What should the administrator do to fix the issue?
- A. Configure branch1_fgt as the installation target for policy 3.
- B. Configure HUB1 as the destination of policy 3.
- C. Configure a normalized interface for the IPsec tunnel HUB1-VPN1.
- D. Configure both HUB1-VPN1 and HUB1-VPN2 as the destination of policy 3
Answer:
B
Explanation:
Policy 3 points traffic To = HUB1-VPN1, which is an SD-WAN member interface. In SD-WAN you must
reference the SD-WAN zone (the logical interface) in policies, not its member tunnels. Change the
policy’s To interface to the zone HUB1, and the install will succeed.
Question 2
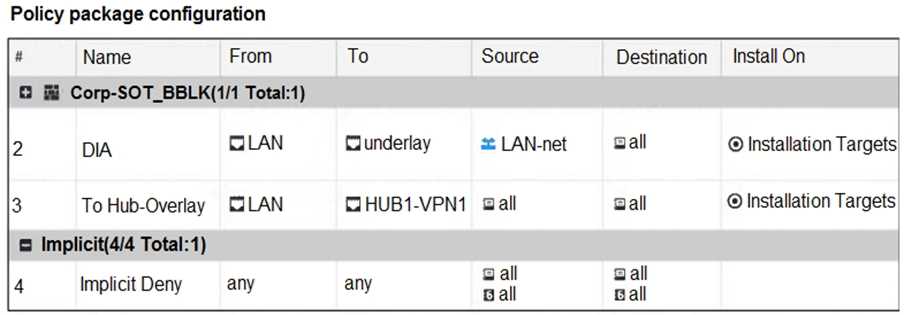
Refer to the exhibit that shows an SD-WAN zone configuration on the FortiManager GUI.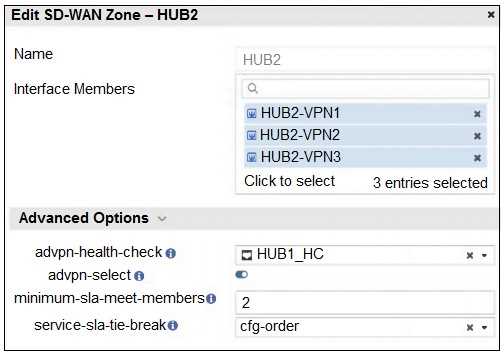
Based on the exhibit, how will the FortiGate device behave after it receives this configuration?
- A. The configuration instructs FortiGate to choose an ADVPN shortcut based on SD-WAN information.
- B. The configuration instructs FortiGate to allow ADVPN shortcuts for the tunnels of this SD-WAN zone.
- C. The configuration instructs FortiGate to establish shortcuts only when at least two members meet the SLA target.
- D. The configuration instructs FortiGate to establish shortcuts only for overlay interfaces that meet the SLA target HUB1_HC.
Answer:
C
Explanation:
This is because the setting minimum-sla-meet-members = 2 requires at least two SD-WAN zone
members (in this case, HUB2-VPN1, HUB2-VPN2, and HUB2-VPN3) to pass the defined SLA health
check (HUB1_HC) before the FortiGate will establish ADVPN shortcuts. If fewer than two members
meet the SLA, shortcuts will not be created.
Question 3
Which three factors about SLA targets and SD-WAN rules should you consider when configuring SD-
WAN rules? (Choose three.)
- A. Member metrics are measured only if a rule uses the SLA target.
- B. SLA targets are used only by SD-WAN rules that are configured with a Lowest Cost (SLA) strategy.
- C. SD-WAN rules can use SLA targets to check whether the preferred members meet the SLA requirements.
- D. When configuring an SD-WAN rule, you can select multiple SLA targets if they are from the same performance SLA.
- E. When configuring an SD-WAN rule, you can select multiple SLA targets from different performance SLAs.
Answer:
B, C, E
Explanation:
The use of SLA targets is specific to certain SD-WAN strategies. The "Lowest Cost (SLA)" and
"Maximize Bandwidth (SLA)" strategies are explicitly designed to use the configured SLA targets to
make routing decisions. The "Best Quality" strategy uses performance metrics but does not
necessarily require or reference SLA targets in the same way, while "Manual" does not use metrics at
all for path selection.
This is a core function of SD-WAN rules with SLA targets. The purpose of configuring an SLA target
with specific thresholds for latency, jitter, and packet loss is to define what is considered "acceptable"
performance for an application. SD-WAN rules then use these targets to check if the members
(interfaces) meet these requirements before a flow is steered over them, ensuring that a preferred
path still offers a good user experience.
FortiGate allows for a single SD-WAN rule to reference multiple, different performance SLAs. This is
crucial for complex deployments where a single SD-WAN rule needs to handle traffic for multiple
applications that have distinct performance requirements. For example, a single rule might direct
VoIP traffic based on one performance SLA with strict latency/jitter targets, while simultaneously
handling general web traffic using another performance SLA with more lenient requirements.
Question 4
Refer to the exhibits.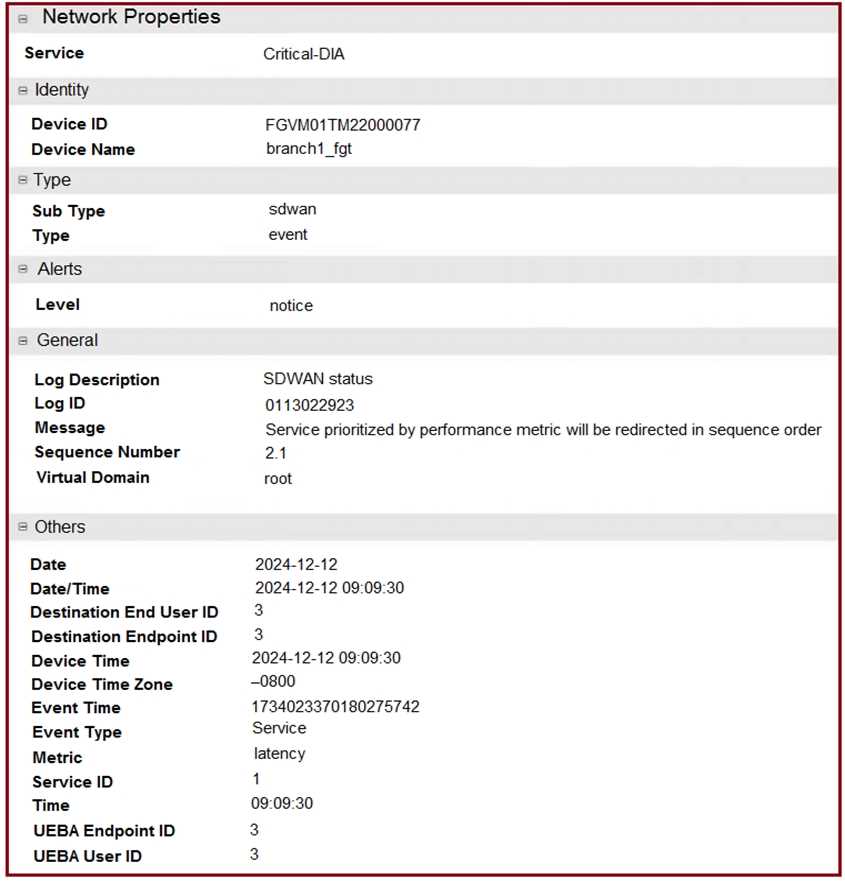
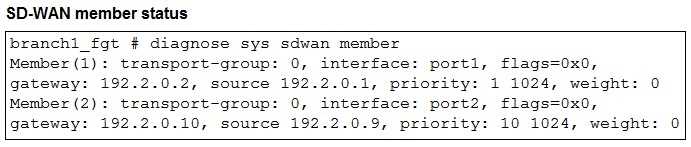
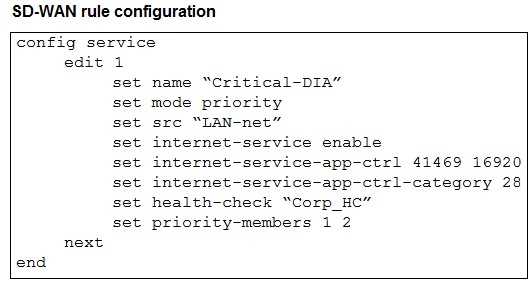
The exhibits show an SD-WAN event log, the member status, and the SD-WAN rule configuration.
Which two conclusions can you draw from the information shown? (Choose two.)
- A. The administrator configured the service ID 1 with the highest priority member for port2.
- B. Port2 has a lower latency than port1.
- C. FortiGate updated the outgoing interface list on the rule so it prefers port2.
- D. The administrator configured the SD-WAN rule ID 1 with the default strategy mode.
Answer:
B, C
Explanation:
The SD-WAN rule (config service edit 1) is configured with set mode priority. This means the rule
selects the best interface based on a defined performance metric, as opposed to a simple static
priority or SLA. The event log (image_41cfb5.png) shows Metric latency and Message Service
prioritized by performance metric will be redirected in sequence order. This indicates that the rule is
using latency to determine the preferred member. Given that the log message is about a change, and
the most logical reason for a change in a priority mode is that a different member is now the best
performer, it implies that the latency on port2 has become lower than that on port1.
The log message Service prioritized by performance metric will be redirected in sequence order
confirms that FortiGate is changing the member being used for this service. Because the mode is
priority, FortiGate dynamically selects the member that currently meets the best performance
criteria, which in this case is latency. The log implies a new member has been selected as the most
optimal, and with the default configuration, the members are sorted based on their performance, so
the outgoing interface list is effectively updated to prefer the new best-performing member (port2).
Question 5
Refer to the exhibit.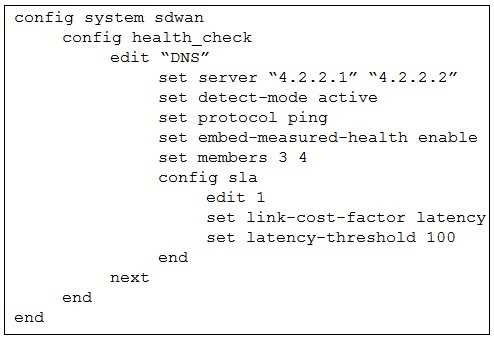
The exhibit shows the health-check configuration on a FortiGate device used as a spoke. You notice
that the hub FortiGate doesn’t prioritize the traffic as expected.
Which two configuration elements should you check on the hub? (Choose two.)
- A. The performance SLA has the parameter priority-out-sla configured.
- B. This performance SLA uses the same members.
- C. The performance SLA uses the same criteria.
- D. The performance SLA is configured with set embedded-measure accept.
Answer:
C, D
Explanation:
The hub must use a performance SLA with the same criteria as the spoke's health check. The spoke's
health check is using ping (protocol ping) and measuring latency (link-cost-factor latency). For the
hub to use the data sent by the spoke, its performance SLA must be configured to measure the same
metrics. If the hub is looking for jitter or packet loss, it will not use the latency data sent by the
spoke.
When a spoke sends embedded health data, the hub FortiGate must be configured to receive and
use it. This is done by setting set embedded-measure accept within the performance SLA
configuration on the hub. This setting explicitly tells the hub to trust and use the performance
metrics received from the remote FortiGate (the spoke). Without this setting, the hub will likely
ignore the embedded health data and rely on its own health checks, which could lead to incorrect
traffic prioritization.
Question 6
Refer to the exhibit.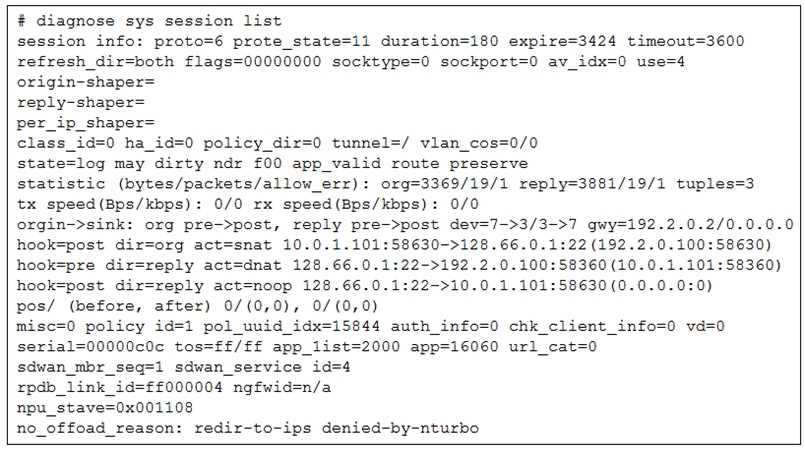
The administrator configured the SD-WAN rule ID 4 with two members (port1 and port2) and
strategy lowest cost (SLA).
What are the two characteristics of the session shown in the exhibit? (Choose two.)
- A. FortiGate steered this flow according to an SD-WAN rule.
- B. FortiGate will never re-evaluate this session.
- C. FortiGate steered this flow according to the application detected and the outgoing interface is port3.
- D. FortiGate will re-evaluate this session if the outgoing interface goes down.
Answer:
A, D
Explanation:
The line sdwan_mbr_seq=1 sdwan_service_id=4 indicates that this session is part of an SD-WAN
rule. sdwan_service_id=4 confirms that the session is being handled by SD-WAN rule ID 4. This
directly links the flow to the SD-WAN configuration.
The line no_offload_reason: redir-to-ips denied-by-nturbo shows that the session is not offloaded to
the NPU (Network Processing Unit) and is being processed by the main CPU. A session that is not
offloaded can be re-evaluated. If the outgoing interface (the one currently being used) goes down,
the FortiGate will re-evaluate the session against the SD-WAN rules to find a new active member to
steer the traffic through. This is a fundamental behavior of SD-WAN, which ensures network
resilience.
Question 7
The FortiGate devices are managed by ForliManager, and are configured for direct internet access
(DIA). You confirm that DIA is working as expected for each branch, and check the SD-WAN zone
configuration and firewall policies shown in the exhibits.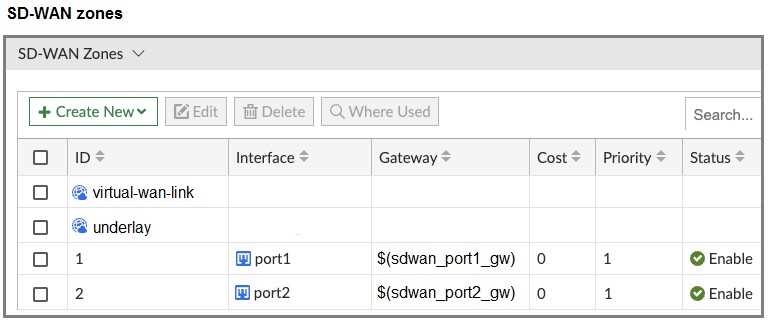
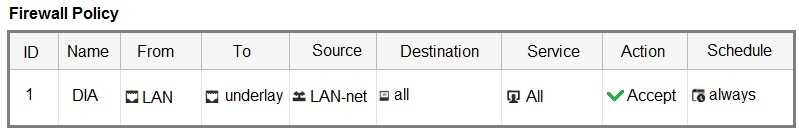
Then, you use the SD-WAN overlay template to configure the IPsec overlay tunnels. You create the
associated SD-WAN rules to connect existing branches to the company hub device and apply the
changes on the branches.
After those changes, users complain that they lost internet access. DIA is no longer working.
Based on the exhibit, which statement best describes the possible root cause of this issue?
- A. The SD-WAN overlay template defines a zone for each underlay interface and moves the interfaces into those zones.
- B. The SD-WAN overlay template didn’t configure a firewall policy to allow traffic through the overlay.
- C. The SD-WAN overlay template redefines the interface gateway addresses if they are defined with metadata variables.
- D. The SD-WAN overlay template updates the SD-WAN template and the rules.
Answer:
A
Explanation:
The SD-WAN overlay template defines a zone for each underlay interface and moves the interfaces
into those zones. This statement perfectly describes the likely sequence of events. The template,
when applied, re-organizes the interfaces and zones, causing the existing firewall policy that relies on
the old zone configuration to fail. This is the most plausible root cause.
Question 8
Refer to the exhibit.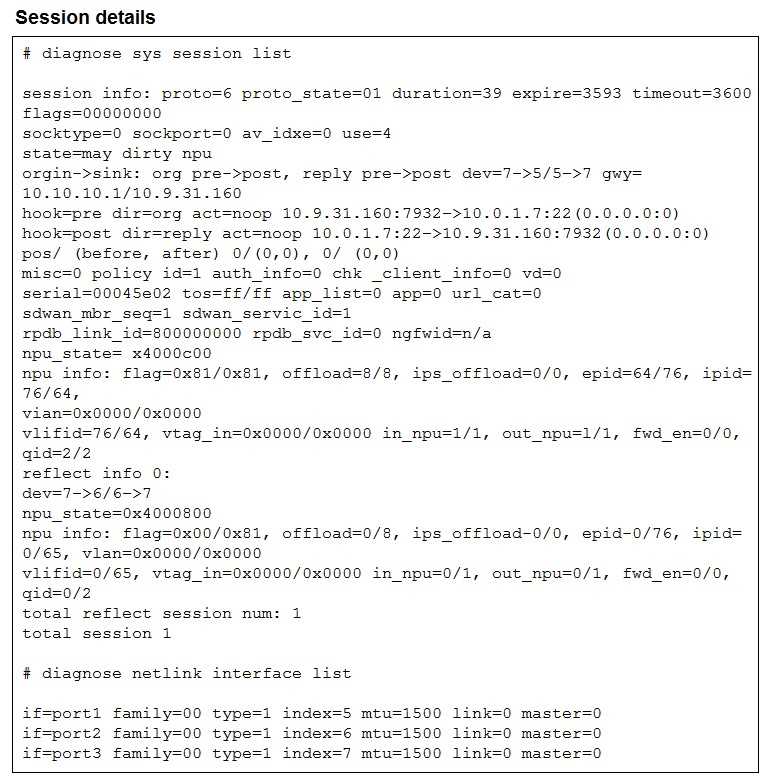
The exhibit shows the details of a session and the index numbers of some relevant interfaces on a
FortiGate device that supports hardware offloading.
Based on the information shown in the exhibits, which two conclusions can you draw? (Choose two.)
- A. By default, FortiGate offloads symmetric and asymmetric flows.
- B. The original direction of the symmetric traffic flows from port3 to port2.
- C. The reply direction of the asymmetric traffic flows from port2 to port3.
- D. The auxiliary session can be offloaded to hardware.
Answer:
B, C
Explanation:
The session details show the symmetric flow’s original direction as port3 → port2.
The asymmetric flow’s reply direction is listed as port2 → port3.
Question 9
Refer to the exhibit.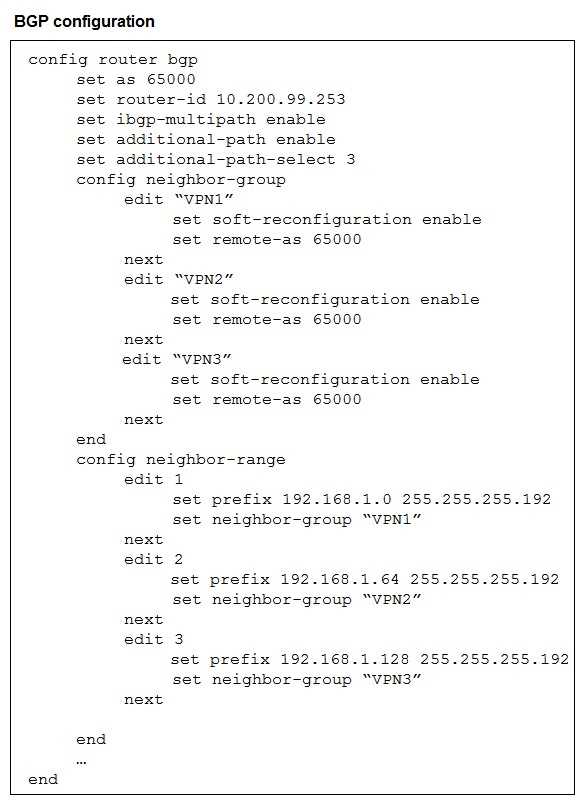
The exhibit shows the BGP configuration on the hub in a hub-and-spoke topology. The administrator
wants BGP to advertise prefixes from spokes to other spokes over the IPsec overlays, including
additional paths. However, when looking at the spoke routing table, the administrator does not see
the prefixes from other spokes and the additional paths
Which three settings must the administrator configure inside each BGP neighbor group so spokes can
learn the prefixes of other spokes and their additional paths? (Choose three.)
- A. Set additional-path to send
- B. Set additional-path to forward
- C. Enable route-reflector-server
- D. Enable route-reflector-client.
- E. Set adv-additional-path to the number of additional paths to advertise.
Answer:
A, D, E
Explanation:
The hub must send additional paths to spokes (set additional-path send).
The hub must treat each spoke as a route-reflector client so spoke routes are reflected to other
spokes.
The hub must specify how many additional paths to advertise (set adv-additional-path <n>).
Question 10
Refer to the exhibits, which show the configuration of an SD-WAN rule and the corresponding rule
status and routing table.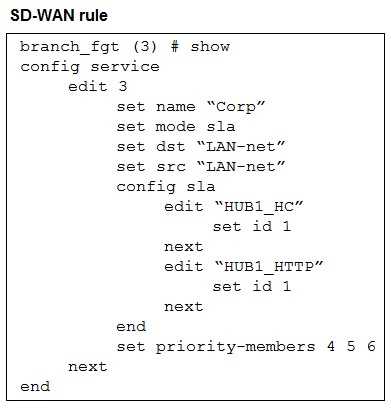
The administrator wants to understand the expected behavior for traffic matching the SD-WAN rule.
Based on the exhibits, what can the administrator expect for traffic matching the SD-WAN rule?
- A. The traffic will be routed over HUB1-VPN3.
- B. The traffic will be routed over HUB1-VPN2
- C. The traffic will be routed over HUB1-VPN1.
- D. The traffic will be load balanced across all three overlays
Answer:
B
Explanation:
The rule is in SLA mode with two SLAs. From the status, HUB1-VPN2 and HUB1-VPN3 meet the SLA
(sla(0x2) and sla(0x3)), while HUB1-VPN1 does not (sla(0x0)). Among members that meet SLA,
FortiGate uses the configured order (priority-members 4 5 6) to pick the first eligible one—HUB1-
VPN2—so traffic is routed over HUB1-VPN2.
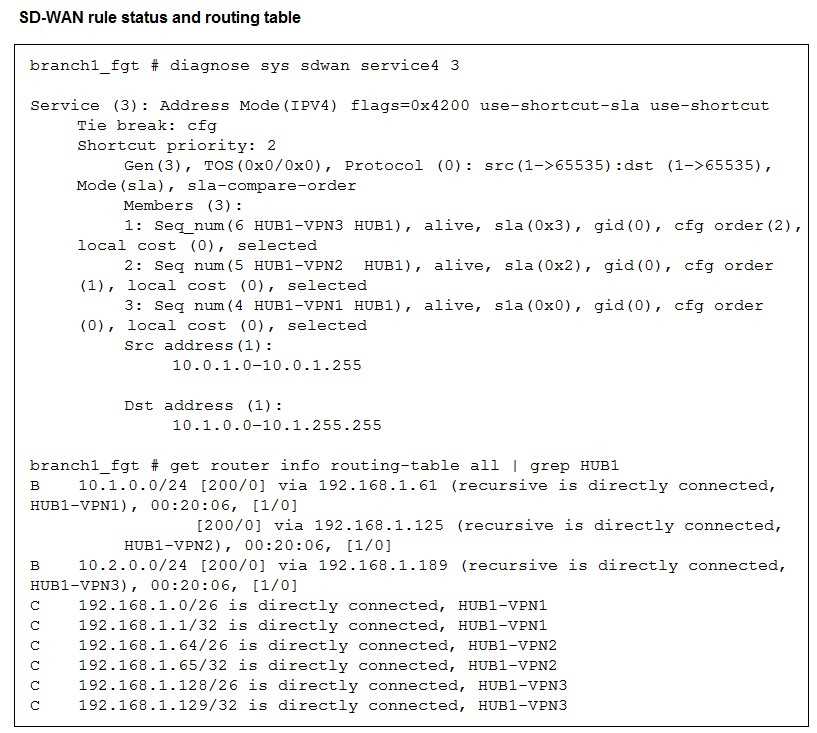
Question 11
Refer to the exhibit, which shows the SD-WAN rule status and configuration.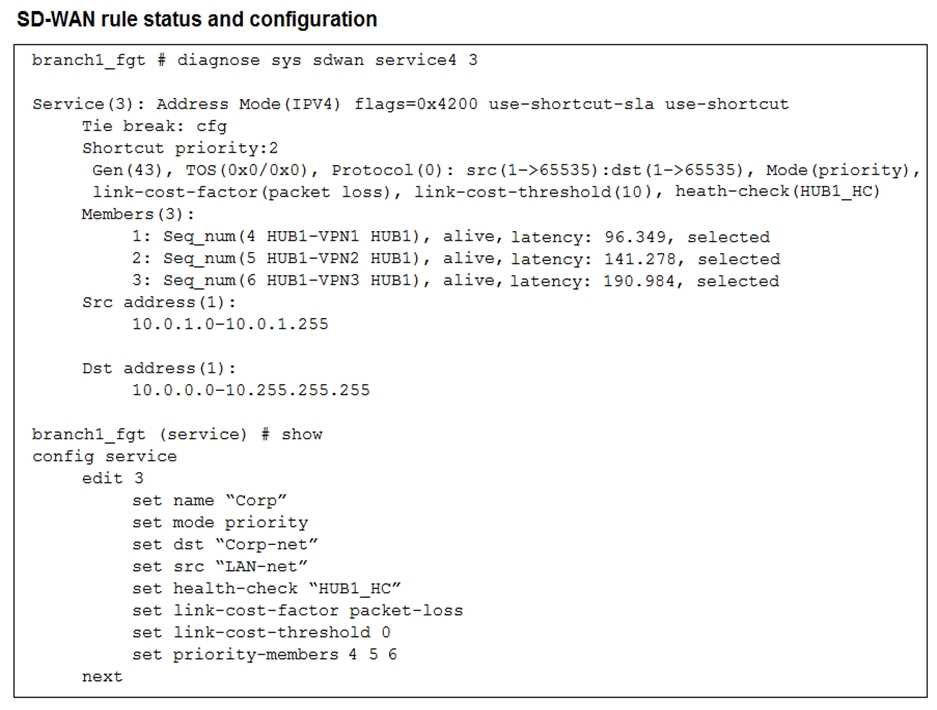
Based on the exhibit, which change in the measured latency will first make HUB1-VPN3 the new
preferred member?
- A. When HUB1-VPN3 has a lower latency than HUB1-VPN1 and HUB1-VPN2
- B. When HUB1-VPN3 has a latency of 80 ms
- C. When HUB1-VPN3 has a latency of 90 ms
- D. When HUB1-VPN1 has a latency of 200 ms
Answer:
D
Explanation:
The rule is in priority mode with HUB1-VPN1 (seq 4) as the first preferred member, HUB1-VPN2
second, and HUB1-VPN3 third. Latency itself does not cause HUB1-VPN3 to become preferred unless
a higher-priority member fails SLA. If HUB1-VPN1’s latency exceeds the SLA threshold (here
simulated by latency reaching 200 ms), FortiGate stops using it and moves down the priority list. That
is when HUB1-VPN3 could become the active path.
Question 12
As an MSSP administrator, you are asked to configure ADVPN on an existing SD-WAN topology.
FortiManager manages the customer devices in a dedicated ADOM. The previous administrator used
the SD-WAN overlay topology.
Which two statements apply to this scenario? (Choose two.)
- A. You can activate auto-discovery VPN in the SD-WAN overlay template only if it is a single hub topology.
- B. When auto-discovery VPN is enabled, FortiManager updates the IPsec and BGP templates in the hub.
- C. After you enable auto-discovery VPN in the overlay template, you must select between ADVPN 2.0 and ADVPN 1.0.
- D. You can activate auto-discovery VPN in the SD-WAN overlay template for any type of topology, including a primary-primary dual-hub topology.
Answer:
B, D
Explanation:
When you enable ADVPN (auto-discovery VPN) in the overlay template, FortiManager automatically
updates both the IPsec and BGP templates on the hub so that shortcut tunnels can be established
dynamically.
ADVPN can be activated in the SD-WAN overlay template for any supported topology, including dual-
hub primary–primary, not just single hub.
Question 13
You used the HUB IPsec_Recommended and the BRANCH IPsec_Recommended templates to define
the overlay topology. Then, you used the SD-WAN template to define the SD- WAN members, rules,
and performance SLAs.
You applied the changes to the devices and want to use the FortiManager monitors menu to get a
graphical view that shows the status of each SD-WAN member.
Which statement best explains how to obtain this graphical view?
- A. Use the SD-WAN monitor template view to get a map view of the branches, hub, and tunnel status, including the SLA pass or missed status.
- B. Use the SD-WAN monitor table view to get a donut view and a table view that shows the status of each SD-WAN member, including the SLA pass or missed status.
- C. Use the VPN monitor map view to get a map view of the branches, hub, and tunnel status, including the SLA pass or missed status.
- D. Use the SD-WAN monitor asset view to get a donut view and a table view that shows the status of each device and the SLA status of each SD-WAN member.
Answer:
B
Explanation:
The SD-WAN monitor’s table view in FortiManager provides a donut visualization plus a detailed
table that shows each SD-WAN member’s status and SLA pass/miss, giving the per-member health
view you’re after.
Question 14
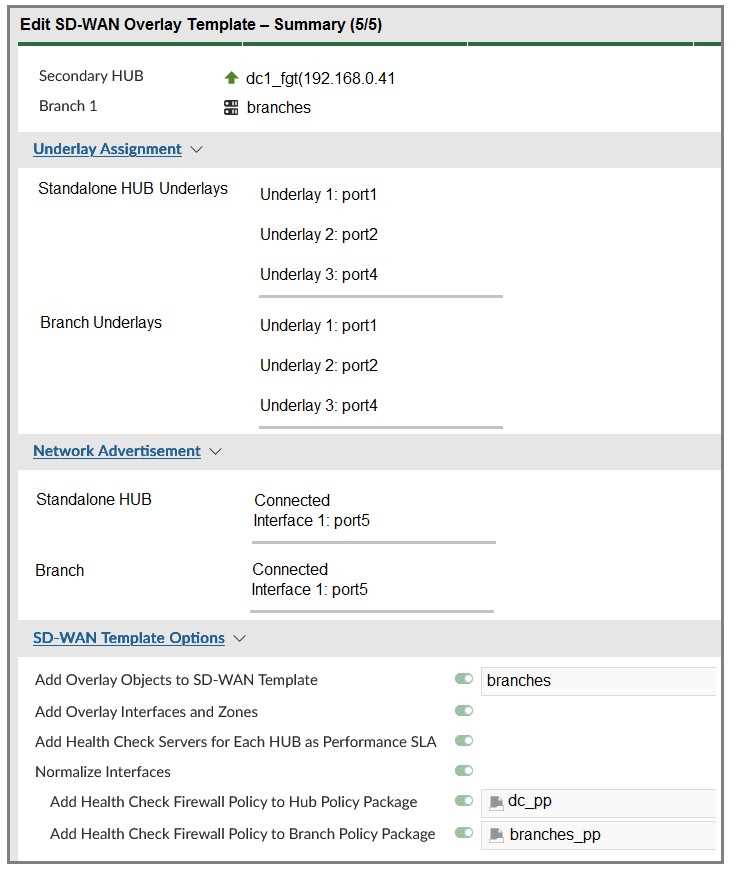
The administrator uses the FortiManager SD-WAN overlay template to prepare an SD-WAN
deployment. Using information provided through the SD-WAN overlay template wizard,
FortiManager creates templates ready to install on the spoke and hub devices.
What are the three templates created by the SD-WAN overlay template for a spoke device? (Choose
three.)
- A. Static route template
- B. Rules template
- C. CLI template
- D. BGP template
- E. IPsec tunnel template
Answer:
B, D, E
Explanation:
Rules template → Defines the SD-WAN rules for traffic steering.
BGP template → Configures dynamic routing for overlay tunnels.
IPsec tunnel template → Builds the IPsec VPN tunnels from the spoke to the hubs.
Question 15
Refer to the exhibits.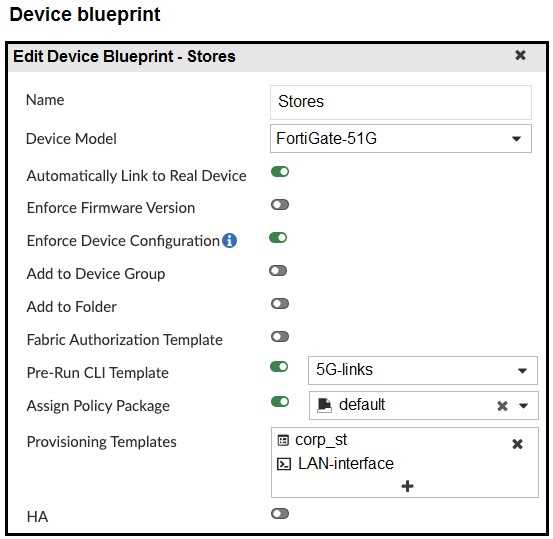
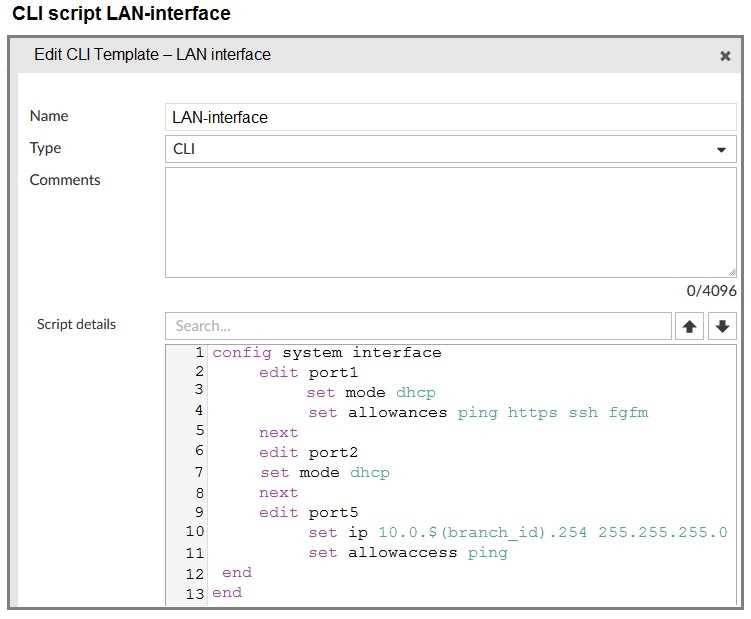
The administrator configured a device blueprint and CLI scripts as shown in the exhibits, to prepare
for onboarding FortiGate devices in the company’s stores. Later, a technician prepares a FortiGate
51G with a basic configuration and connects it to the network. The basic configuration contains the
port1 configuration and the minimal configuration required to allow the device to connect to
FortiManager.
After the device first connects to FortiManager, FortiManager updates the device configuration.
Based on the exhibits, which actions does FortiManager perform?
- A. FortiManager updates the device configuration according to the selected templates. It applies the corp_st template first.
- B. FortiManager does not update the port1 configuration because FortiManager does not change the configuration of interfaces with fgfm access.
- C. FortiManager updates access rights only for port1. FortiManager cannot update the IP address because it was already set manually.
- D. FortiManager updates the configuration of port1, port2, and port5. The three ports might get new IP addresses.
Answer:
D
Explanation:
Enforce Device Configuration is enabled and the blueprint applies the provisioning CLI templates.
The LAN-interface script sets port1 and port2 to DHCP and assigns a static IP to port5 (using the
branch_id variable). Therefore, when FortiManager pushes the blueprint, it updates the
configurations of port1, port2, and port5 - and their IP addresses may change accordingly.