Fortinet FCSS SASE AD 25 Exam Questions
Questions for the FCSS SASE AD 25 were updated on : Feb 22 ,2026
Page 1 out of 4. Viewing questions 1-15 out of 53
Question 1
Refer to the exhibits.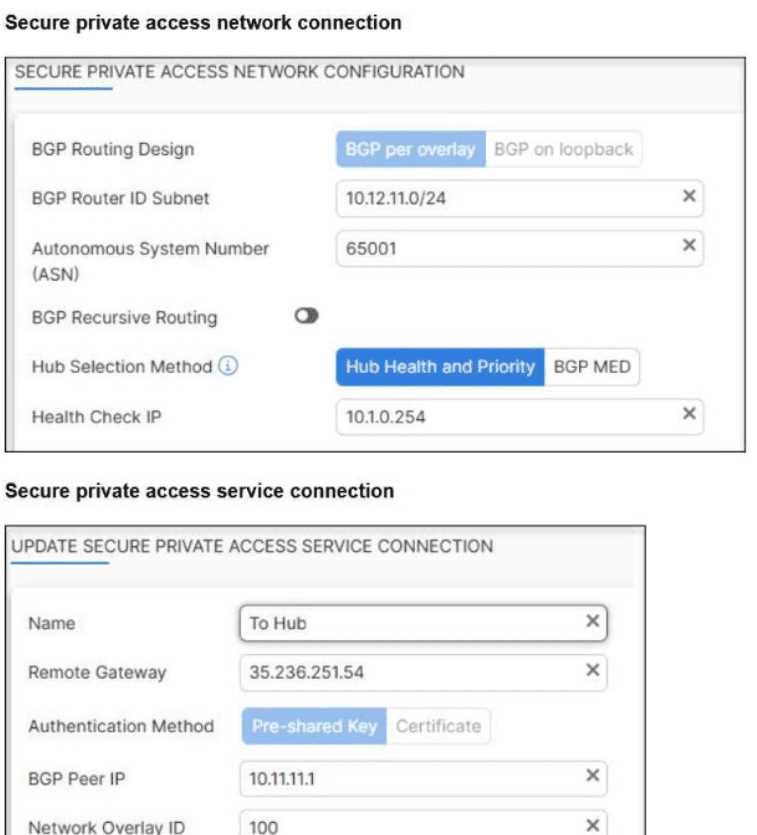
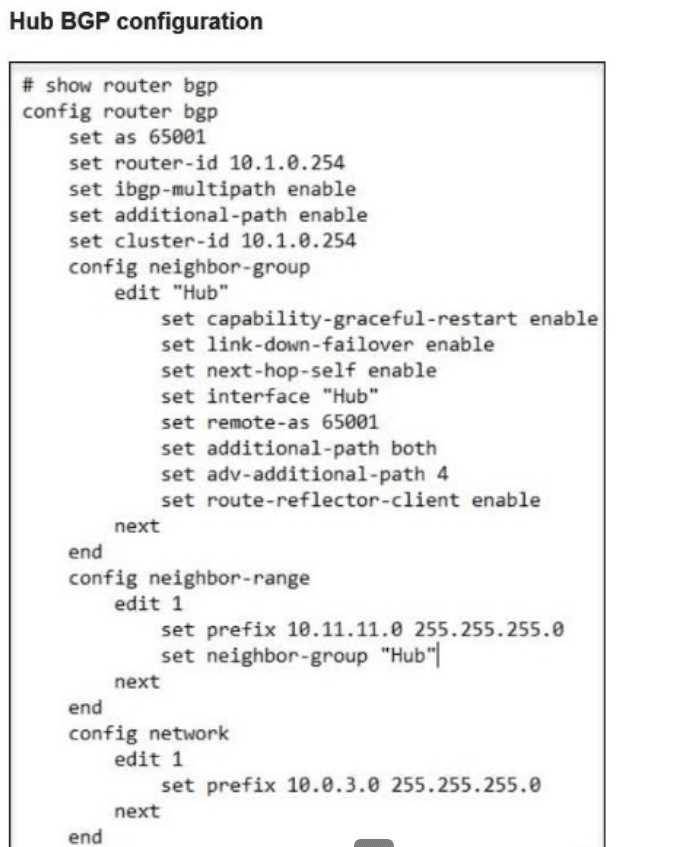

A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub.
The VPN tunnel does not establish.
Which configuration needs to be modified to bring the tunnel up?
- A. FortiSASE spoke devices do not support mode config.
- B. The network overlay ID must match on FortiSASE and the hub.
- C. The BGP router ID must match on the hub and FortiSASE.
- D. Auto-discovery-sender must be disabled on IPsec phase1 settings.
Answer:
B
Explanation:
Fortinet documentation makes clear that overlay IDs must be identical on hub and spoke for ADVPN
to establish correctly:
“When configuring the root and downstream FortiGates the Fabric Overlay Orchestrator configures…
IPsec overlay configuration (hub and spoke ADVPN tunnels).”
“The Fabric root will be the hub and any first-level downstream devices from the Fabric root will be
spokes.”
In the scenario:
FortiSASE overlay ID = 100
FortiGate hub overlay ID = 101
Mismatch prevents tunnel establishment. Therefore, the fix is: B. The network overlay ID must match
on FortiSASE and the hub.
Question 2
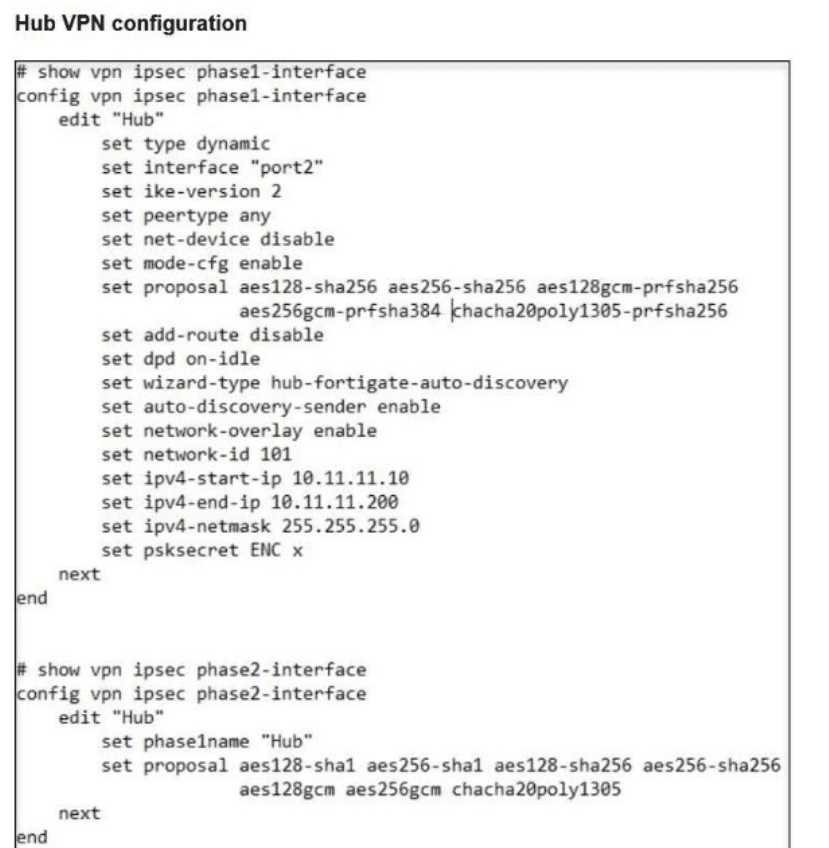
Refer to the exhibit.
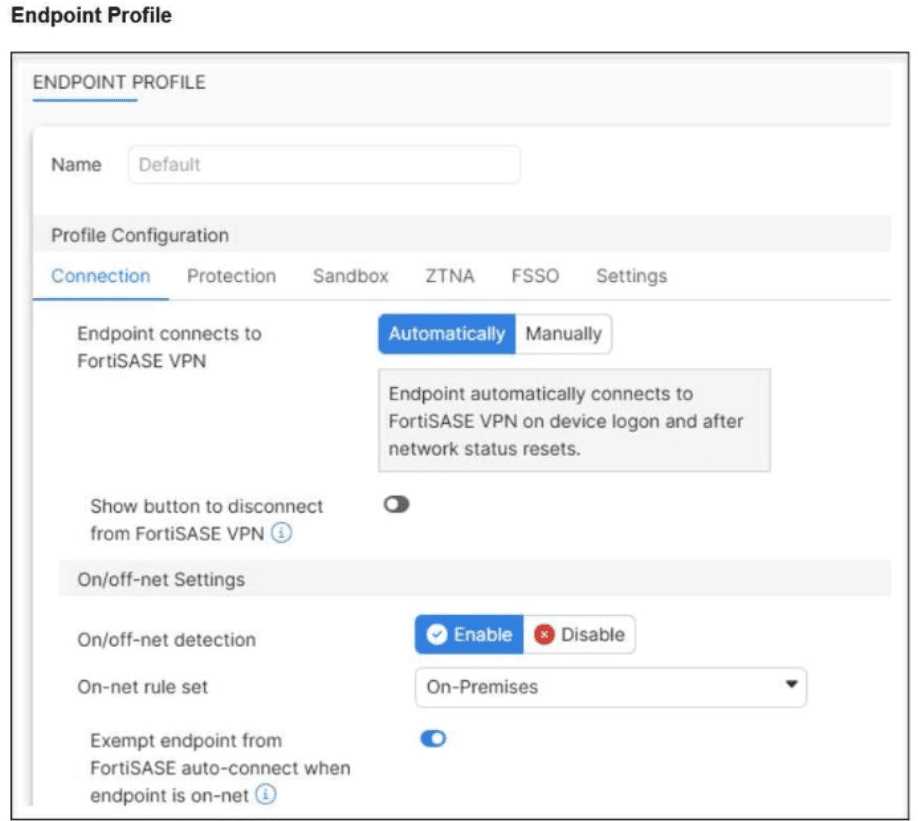
An endpoint is assigned an IP address of 192.168.13.101/24.
Which action will be run on the endpoint?
- A. The endpoint will be exempted from auto-connect to the FortiSASE tunnel.
- B. The endpoint will automatically connect to the FortiSASE tunnel.
- C. The endpoint will be detected as off-net.
- D. The endpoint will be able to bypass the on-net rule because it is connecting from a known subnet.
Answer:
A
Explanation:
The FortiClient Administration Guide states that on-net rules determine when an endpoint is in a
trusted location. If the endpoint matches the configured subnet, the client is considered on-net, and
therefore bypasses auto-connect.
“Device registration and on-net status information for a device that is running FortiClient appears
only on the FortiGate that applies the FortiClient profile to that device.”
Since 192.168.13.101 falls inside the trusted subnet 192.168.13.0/24, the endpoint is treated as on-
net → it will be exempted from auto-connect.
Question 3
Which two are required to enable central management on FortiSASE? (Choose two.)
- A. FortiSASE connector configured on FortiManager.
- B. FortiSASE central management entitlement applied to FortiManager.
- C. The FortiManager IP address in the FortiSASE central management configuration.
- D. FortiManager and FortiSASE registered under the same FortiCloud account.
Answer:
B,D
Explanation:
According to the FortiOS Administration Guide, when configuring central management, a
FortiManager Cloud entitlement must be present and the devices must share the same FortiCloud
account for registration. Specifically:
“The FortiManager Cloud button can only be selected if you have a FortiManager Cloud product
entitlement.”
“The FortiGate and FortiCloud license are registered to the same account.”
Thus, the two verified requirements are: B (entitlement) and D (same FortiCloud account).
Question 4
Refer to the exhibit.
The daily report for application usage for internet traffic shows an unusually high number of
unknown applications by category.
What are two possible explanations for this? (Choose two.)
- A. Certificate inspection is not being used to scan application traffic.
- B. Deep inspection is not being used to scan traffic.
- C. The private access policy must be to set to log Security Events.
- D. The inline-CASB application control profile does not have application categories set to Monitor.
Answer:
A,B
Question 5
Your organization is currently using FortiSASE for its cybersecurity. They have recently hired a
contractor who will work from the HQ office and who needs temporary internet access in order to
set up a web-based point of sale (POS) system.
What is the recommended way to provide internet access to the contractor?
- A. Use zero trust network access (ZTNA) and tag the client as an unmanaged endpoint.
- B. Use the self-registration portal on FortiSASE to grant internet access.
- C. Use a tunnel policy with a contractors user group as the source on FortiSASE to provide internet access.
- D. Use a proxy auto-configuration (PAC) file and provide secure web gateway (SWG) service as an explicit web proxy.
Answer:
B
Explanation:
The self-registration portal is the recommended method for granting temporary internet access to
contractors or guests. It provides a simple and secure way for the contractor to authenticate and
access the internet without requiring full endpoint management or policy configuration.
Question 6
Which two of the following can release the network lockdown on the endpoint applied by FortiSASE?
(Choose two.)\
- A. When the endpoint connects to the FortiSASE tunnel
- B. When the endpoint is determined as on-net
- C. When the endpoint is rebooted
- D. When the endpoint is determined as compliant using ZTNA tags
Answer:
A,D
Explanation:
FortiSASE releases network lockdown when the endpoint re-establishes the tunnel connection or
when it is verified as compliant through ZTNA tag evaluation, ensuring it meets security posture
requirements.
Question 7
Refer to the exhibits.
How will the application vulnerabilities be patched, based on the exhibits provided?
- A. The vulnerability will be patched automatically based on the endpoint profile configuration.
- B. The vulnerability will be patched by installing the patch from the vendor’s website.
- C. The end user will patch the vulnerabilities using the FortiClient software.
- D. An administrator will patch the vulnerability remotely using FortiSASE.
Answer:
B
Question 8
What are two benefits of deploying secure private access with SD-WAN? (Choose two.)
- A. a direct access proxy tunnel from FortiClient to the on-premises FortiGate
- B. ZTNA posture check performed by the hub FortiGate
- C. support of both TCP and UDP applications
- D. inline security inspection by FortiSASE
Answer:
B,C
Explanation:
Deploying secure private access with SD-WAN enables the hub FortiGate to perform ZTNA posture
checks, and supports both TCP and UDP applications over the tunnel, allowing for flexible and secure
access to internal resources.
Question 9
Which statement applies to a single sign-on (SSO) deployment on FortiSASE?
- A. SSO users can be imported into FortiSASE and added to user groups.
- B. SSO is recommended only for agent-based deployments.
- C. SSO overrides any other previously configured user authentication.
- D. SSO identity providers can be integrated using public and private access types.
Answer:
C
Explanation:
In FortiSASE, Single Sign-On (SSO) takes precedence and overrides other configured user
authentication methods, ensuring a centralized and streamlined authentication process across
services.
Question 10
When accessing the FortiSASE portal for the first time, an administrator must select data center
locations for which three FortiSASE components? (Choose three.)
- A. Identity & access management (IAM)
- B. Points of presence
- C. Endpoint management
- D. Logging
- E. Sandbox
Answer:
B,C,D
Question 11
What is required to enable the MSSP feature on FortiSASE?
- A. Role-based access control (RBAC) must be assigned to identity and access management (IAM) users using the FortiCloud IAM portal.
- B. The MSSP add-on license must be applied to FortiSASE.
- C. MSSP user accounts and permissions must be configured on the FortiSASE portal.
- D. Multi-tenancy must be enabled on the FortiSASE portal.
Answer:
A
Explanation:
To enable the MSSP feature on FortiSASE, you must use the FortiCloud IAM portal to assign RBAC
permissions to users. This grants appropriate access to manage multiple tenants or customer
accounts securely.
Question 12
What happens to the logs on FortiSASE that are older than the configured log retention period?
- A. The logs are deleted from FortiSASE.
- B. The logs are indexed and can be stored in a SQL database.
- C. The logs are backed up on FortiCloud.
- D. The logs are compressed and archived.
Answer:
A
Explanation:
Once the configured log retention period expires, FortiSASE automatically deletes the older logs to
free up storage and maintain compliance with retention policies.
Question 13
Refer to the exhibit.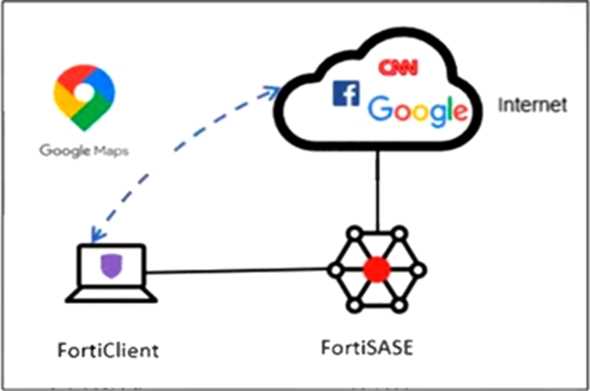
An organization must inspect all the endpoint internet traffic on FortiSASE, and exclude Google Maps
traffic from the FortiSASE VPN tunnel and redirect it to the endpoint physical interface.
Which configuration must you apply to achieve this requirement?
- A. Configure a steering bypass tunnel firewall policy using Google Maps FQDN to exclude and redirect the traffic.
- B. Add the Google Maps URL in the zero trust network access (ZTNA) TCP access proxy forwarding rule.
- C. Add the Google Maps URL as a steering bypass destination in the endpoint profile.
- D. Exempt Google Maps in URL filtering in the web filter profile.
Answer:
C
Explanation:
To exclude specific internet traffic (such as Google Maps) from being tunneled through FortiSASE and
instead direct it out the local endpoint interface, you must configure it as a steering bypass
destination in the FortiClient endpoint profile. This ensures traffic matching the URL bypasses the
FortiSASE tunnel.
Question 14
Refer to the exhibit.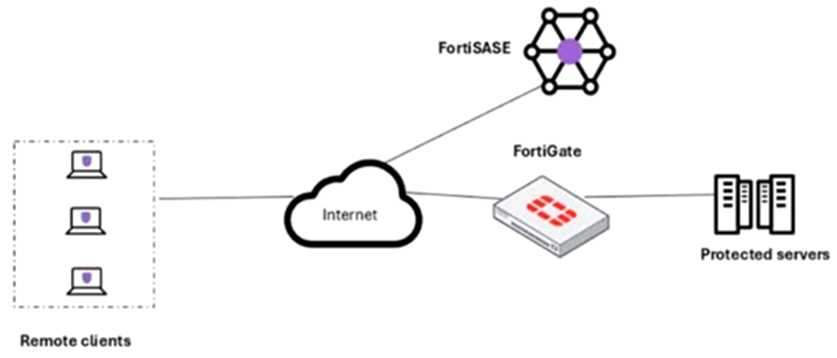
A customer needs to implement device posture checks for their remote endpoints while accessing
the protected server. They also want the TCP traffic between the remote endpoints and the
protected servers to be processed by FortiGate.
In this scenario, which two setups will achieve these requirements? (Choose two.)
- A. Configure ZTNA servers and ZTNA policies on FortiGate.
- B. Configure FortiGate as a zero trust network access (ZTNA) access proxy.
- C. Configure ZTNA tags on FortiGate.
- D. Configure private access policies on FortiSASE with ZTNA.
Answer:
A,B
Explanation:
To enforce device posture checks and ensure that TCP traffic flows through FortiGate, the FortiGate
must act as a ZTNA access proxy and host the ZTNA servers and policies. This setup allows posture
validation via FortiSASE while routing traffic securely to protected servers through FortiGate.
Question 15
An organization must block user attempts to log in to non-company resources while using Microsoft
Office 365 to prevent users from accessing unapproved cloud resources.
Which FortiSASE feature can you implement to meet this requirement?
- A. application control with inline-CASB
- B. data loss prevention (DLP) with Microsoft Purview Information Protection (MPIP)
- C. web filter with inline-CASB
- D. DNS filter with domain filter
Answer:
C