Fortinet FCSS CDS AR 7 6 Exam Questions
Questions for the FCSS CDS AR 7 6 were updated on : Feb 22 ,2026
Page 1 out of 3. Viewing questions 1-15 out of 38
Question 1
What is the main advantage of using SD-WAN Transit Gateway Connect over traditional SD-WAN?
- A. You can use BGP over IPsec for maximum throughput.
- B. You can combine it with IPsec to achieve higher bandwidth.
- C. It eliminates the use of ECMP.
- D. You can use GRE-based tunnel attachments.
Answer:
D
Question 2
Refer to the exhibit.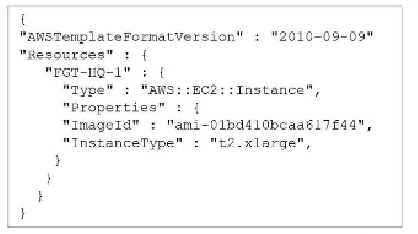
A senior administrator in a multinational organization needs to include a comment in the template
shown in the exhibit to ensure that administrators from other regions change the Amazon Machine
Image (AMI) ID to one that is valid in their location.
How can the administrator add the required comment in that section of the file?
- A. The administrator can include the comment with the aws cloudformation update-stack command.
- B. The administrator must convert the template file to YAML format to add a comment.
- C. The administrator can add the comment starting with the # character next to the "Resources" section.
- D. The administrator must update the AWSTemplateFormatVersion to the latest version.
Answer:
C
Question 3
Refer to the exhibit.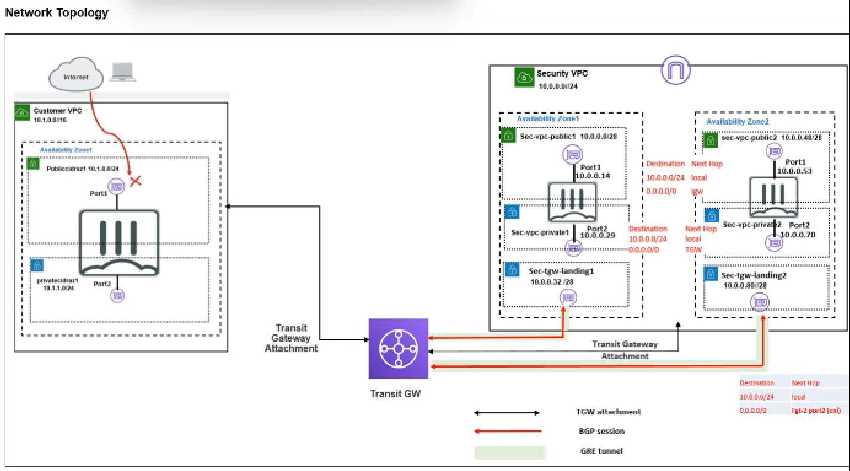
Refer to the exhibit.
In your Amazon Web Services (AWS), you must allow inbound HTTPS access to the Customer VPC
FortiGate VM from the internet. However, your HTTPS connection to the FortiGate VM in the
Customer VPC is not successful.
Also, you must ensure that the Customer VPC FortiGate VM sends all the outbound internet traffic
through the Security VPC.
How do you correct this issue with minimal configuration changes? (Choose three.)
- A. Add a route with your local internet public IP address as the destination and the internet gateway as the target.
- B. Add a route with your local internet public IP address as the destination and the transit gateway as the target.
- C. Add a route to the destination 0.0.0.0/0 with the transit gateway as the target.
- D. Deploy an internet gateway, associate an EIP with the Customer VPC private subnet, and then add a new route with destination 0.0.0.0/0 with the internet gateway as the target.
- E. Deploy an internet gateway, attach it to the Customer VPC, and then associate an EIP with port1 of the FortiGate in the Customer VPC.
Answer:
B, C, E
Question 4
Refer to the exhibit.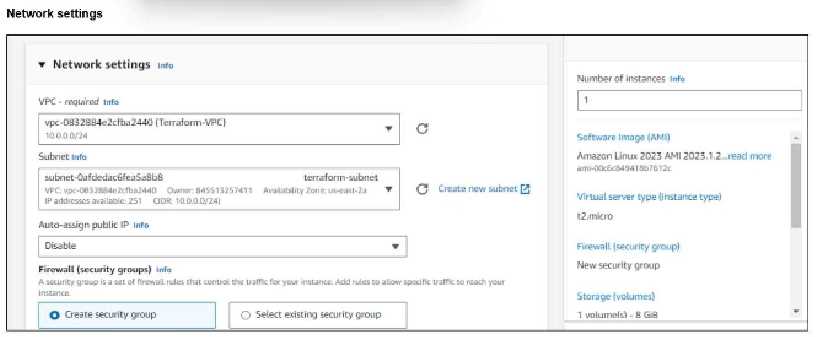
Refer to the exhibit.
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown in
the exhibit.
What next step must the administrator take to access this instance from the internet?
- A. Allocate an Elastic IP address and assign it to the instance.
- B. Create a VIP on FortiGate to allow access.
- C. Enable SSH and allocate it to the device.
- D. Configure the user name and password.
Answer:
A
Question 5
You have deployed a FortiGate HA cluster in Azure using a Gateway Load Balancer for traffic
inspection. However, traffic is not being routed correctly through the firewalls.
What can be the cause of the issue?
- A. The Fortinet VMs have IP forwarding disabled, which is required for traffic inspection.
- B. The health probes for the Gateway Load Balancer are failing, which causes traffic to bypass the HA cluster.
- C. The Gateway Load Balancer is not associated with the correct network security group (NSG) rules, which allow traffic to pass through.
- D. The protected VMs are in a different Azure subscription, which prevents the Gateway Load Balancer from forwarding traffic.
Answer:
B
Question 6
An administrator is relying on an Azure Bicep linter to find possible issues in Bicep files.
Which problem can the administrator expect to find?
- A. The resources to be deployed exceed the quota for a region.
- B. Some resources are missing dependsOn statements.
- C. There are output statements that contain passwords.
- D. One or more modules are not using runtime values as parameters.
Answer:
B
Question 7
You need a solution to safeguard public cloud-hosted web applications from the OWASP Top 10
vulnerabilities. The solution must support the same region in which your applications reside, with
minimum traffic cost.
Which solution meets the requirements?
- A. Use FortiGate
- B. Use FortiCNP
- C. Use FortiWeb
- D. Use FortiADC
Answer:
C
Question 8
Refer to the exhibit.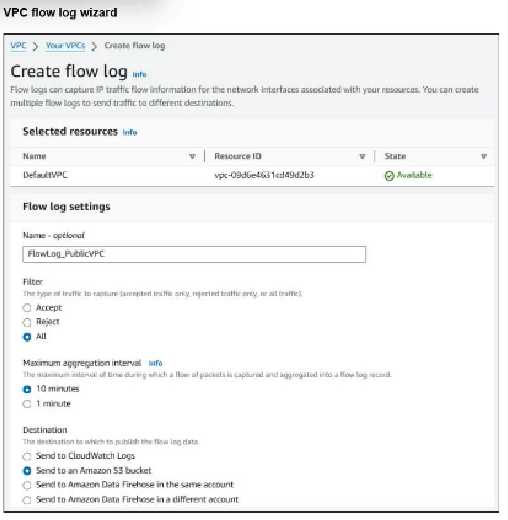
Refer to the exhibit.
An experienced AWS administrator is creating a new Virtual Private Cloud (VPC) flow log with the
settings shown in the exhibit.
What is the purpose of this configuration?
- A. To maximize the number of logs saved
- B. To monitor logs in real time
- C. To retain logs for a long term
- D. To troubleshoot a log flow issue
Answer:
C
Question 9
The cloud administration team is reviewing an AWS deployment that was done using
CloudFormation.
The deployment includes six FortiGate instances that required custom configuration changes after
being deployed. The team notices that unwanted traffic is reaching some of the FortiGate instances
because the template is missing a security group.
To resolve this issue, the team decides to update the JSON template with the missing security group
and then apply the updated template directly, without using a change set.
What is the result of following this approach?
- A. If new FortiGate instances are deployed later, they will include the updated changes.
- B. Some of the FortiGate instances may be deleted and replaced with new copies.
- C. The update is applied, and the security group is added to all instances without interruption.
- D. CloudFormation rejects the update and warns that a new full stack is required.
Answer:
B
Question 10
Your monitoring team reports performance issues with a web application hosted in Azure. You
suspect that the bottleneck might be due to unexpected inbound traffic spikes.
Which method should you use to identify and analyze the traffic pattern?
- A. Deploy Azure Firewall to log traffic by IP address.
- B. Enable Azure DDoS protection to prevent inbound traffic spikes.
- C. Use Azure Traffic Manager to visualize all traffic to the application.
- D. Enable NSG Flow Logs and analyze logs with Azure Monitor.
Answer:
D
Question 11
Refer to the exhibit.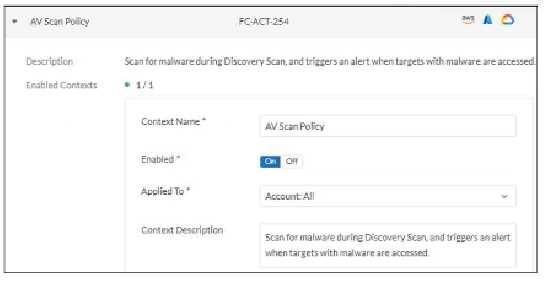
In which type of FortiCNP insights can an administrator examine the findings triggered by this policy?
- A. Data
- B. Threat
- C. Risk
- D. User activity
Answer:
B
Question 12
An administrator is trying to implement FortiCNP with Microsoft Azure Security integration.
However, FortiCNP is not able to extract any cloud integration data from Azure; therefore, real-time
cloud security monitoring is not possible.
What is causing this issue?
- A. The organization is using a free Azure AD license.
- B. The Azure account doesn't have the Global Administrator role.
- C. The administrator enabled the wrong Defender plan for servers.
- D. The FortiCNP account in Azure has the Storage Blob Data Reader role.
Answer:
D
Question 13
Refer to the exhibit.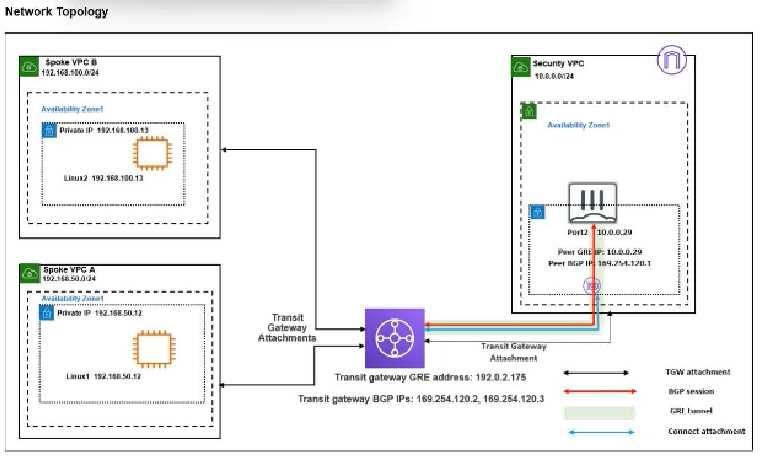
Refer to the exhibit.
You attempted to access the Linux1 EC2 instance directly from the internet using its public IP address
in AWS. However, your connection is not successful.
Given the network topology, what can be the issue?
- A. There is no connection between VPC A and VPC B.
- B. There is no Internet Gateway attached to the Spoke VPC A.
- C. The Transit Gateway BGP IP address is incorrect.
- D. There is no Elastic IP address attached to FortiGate in the Security VPC.
Answer:
B
Question 14
Refer to the exhibit.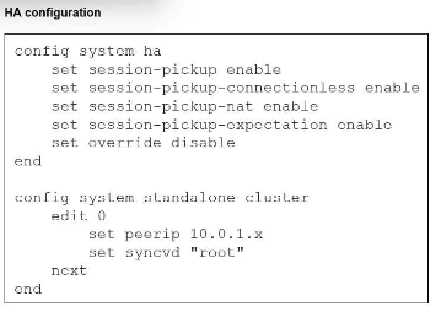
Refer to the exhibit.
You deployed an HA active-active load balance sandwich with two FortiGate VMs in Microsoft Azure.
After the deployment, you prefer to use FGSP to synchronize sessions and allow asymmetric return
traffic. In the environment, FortiGate port 1 and port 2 are facing external and internal load balancers
respectively.
What IP address must you use in the peering configuration?
- A. The opposite FortiGate port 2 IP address.
- B. The public load balancer port 2 IP address.
- C. The internal load balancer port 1 IP address.
- D. The opposite FortiGate port 1 IP address.
Answer:
D
Question 15
Which statement about Transit Gateway (TGW) in Amazon Web Services (AWS) is true?
- A. Both the TGW attachment and propagation must be in the same TGW route table.
- B. TGW can have multiple TGW route tables.
- C. A TGW attachment can be associated with multiple TGW route tables.
- D. The TGW default route table cannot be disabled.
Answer:
B