Fortinet FCP FWF AD 7 4 Exam Questions
Questions for the FCP FWF AD 7 4 were updated on : Feb 22 ,2026
Page 1 out of 2. Viewing questions 1-15 out of 30
Question 1
Which benefit does 802.1X authentication offer when securing a wireless network?
- A. Authentication and authorization m enterprise networks
- B. Allows administrators to gain elevated privilege to access resources
- C. Makes wireless access at home protected and secured
- D. Simplifies public Wi-Fi hotspots for guest access
Answer:
A
Question 2
You must design a wireless network to accommodate wireless stations to access local resources and
the internet The access level of these stations will vary based on the type of device and users
Which design must you use to provide wireless access that will fulfill these requirements?
- A. Create user groups to assign wireless stations once connected to an SSID
- B. Create multiple SSIDs for each level of network access
- C. Create an SSID and enable dynamic wireless VLAN
- D. Create an SSID and enable integrated wireless NAC
Answer:
B
Question 3
Exhibit.
Refer to the exhibit of FortiAP performance diagnostics
The wireless users are having issues with wireless network speed while connecting to the only
FortiAP device As an administrator you accessed the FortiAP diagnostics and tools to explore
performance graphs
The label shows that the transmission bandwidth should be at least 150 Mbps. however the
bandwidth graph shows that the transmission only hit 3 Mbps maximum within the last 5 minutes
What can you observe from this?
- A. Resources on FortiAP are overloaded which limits speed rates for all users
- B. Label values are historical and provide average bandwidth
- C. FortiAP is dual band and is transmitting data faster with a higher frequency band
- D. Bandwidth is shared with other SSID signals broadcasting for nearby AP devices
Answer:
C
Question 4
Refer to the exhibit.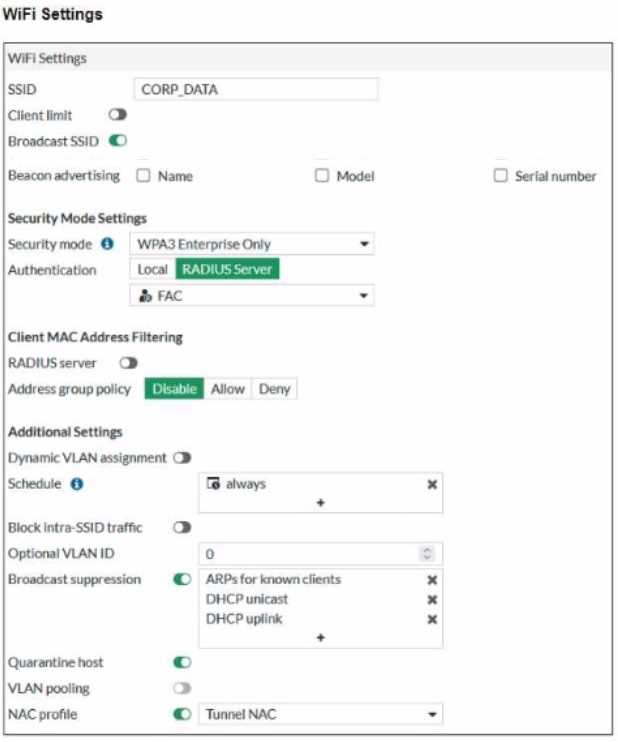
FortiGate sends logs to FortiAnalyzer using the default settings to report security events for all
wireless stations as part of the Security Fabric configuration
Which security action will FortiGate take when it detects a compromised wireless station in the
CORP_DATASSlD?
- A. CORP_DATA is in NAC mode and onboards compromised stations for a period until malicious activity stops
- B. FortiGate disassociates compromised stations and prevents them from connecting again
- C. FortiAnalyzer generates security reports to inform security operations to further Investigate the compromised stations
- D. FortiAP devices broadcasting CORP_DATA wireless network place compromised stations in quarantine
Answer:
A
Question 5
Which action does a wireless client or the access point take when the wireless client moves away
from an associated AP until the signal drops?
- A. The wireless client disconnects and connects to a different, available AP
- B. The associated AP marks the wireless client as disconnected and must not reconnect
- C. The associated AP sends an alert message to the wireless client about the signal drop
- D. The wireless client increases its signal power to continue connecting to the same AP
Answer:
A
Question 6
You plan to deploy a wireless network at various remote sites with no on-site IT available. The
remote sites must have access points to broadcast the wireless networks You can manage the access
points using any Fortinet control and management option
Which two items must you consider in addition to deploying the wireless network and enforcing
Fortinet UTM on all wireless traffic? (Choose two.)
- A. To install the access points designed to provide Fortinet UTM services
- B. To power the access points with a UIM capable FortSwitch device
- C. To deploy the SSlDs in bridge mode bridged to the access points subnet
- D. To manage the access points by FortiLAN Cloud and create a tunnel between access points
Answer:
C, D
Question 7
Which two management services support connecting FortiAPs to the FortiPresence cloud? (Choose
two.
- A. FortiSASE
- B. FortiGate
- C. FortiLAN Cloud
- D. FortiSwitch Manager
Answer:
B, C
Question 8
A FortiAP device is connected directly to a FortiGate interlace. What discovery method will be used
to provision the FortiAP device?
- A. FortiGate discovers the FortiAP IP address from DHCP option 138.
- B. FortiGate discovers the FortiAP through the received broadcast packets.
- C. FortiAP discovers FortiGate by reviewing the vendor class value.
- D. FortiAP discovers FortiGate by connecting to FortiLAN Cloud to verify its management license.
Answer:
B
Question 9
Refer to the exhibit.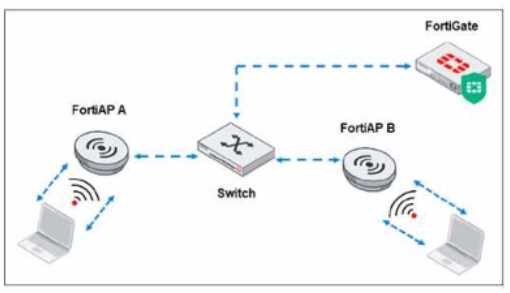
Which traffic is crucial between the FortiAP devices and FortiGate to support AP configuration
updates and management services?
- A. Control traffic
- B. Layer 2 traffic
- C. Data traffic
- D. License management traffic
Answer:
A
Question 10
Refer to the exhibit.
The wireless client connects to the wireless network on WLAN_NET tunnel mode interface The
exhibit stows the client exchange communication with the wireless controller and the RADIUS server
Which two issues can you observe in the wireless station debug outputs (Choose two.)
- A. The wireless client has an unsuccessful association with the wireless controller
- B. The wireless client has failed to complete the four-way handshake process.
- C. The wireless client has denied the connection after many failed trials
- D. The wireless client has incorrect credentials to authenticate with the authentication server
Answer:
B, C
Question 11
Refer to the exhibit.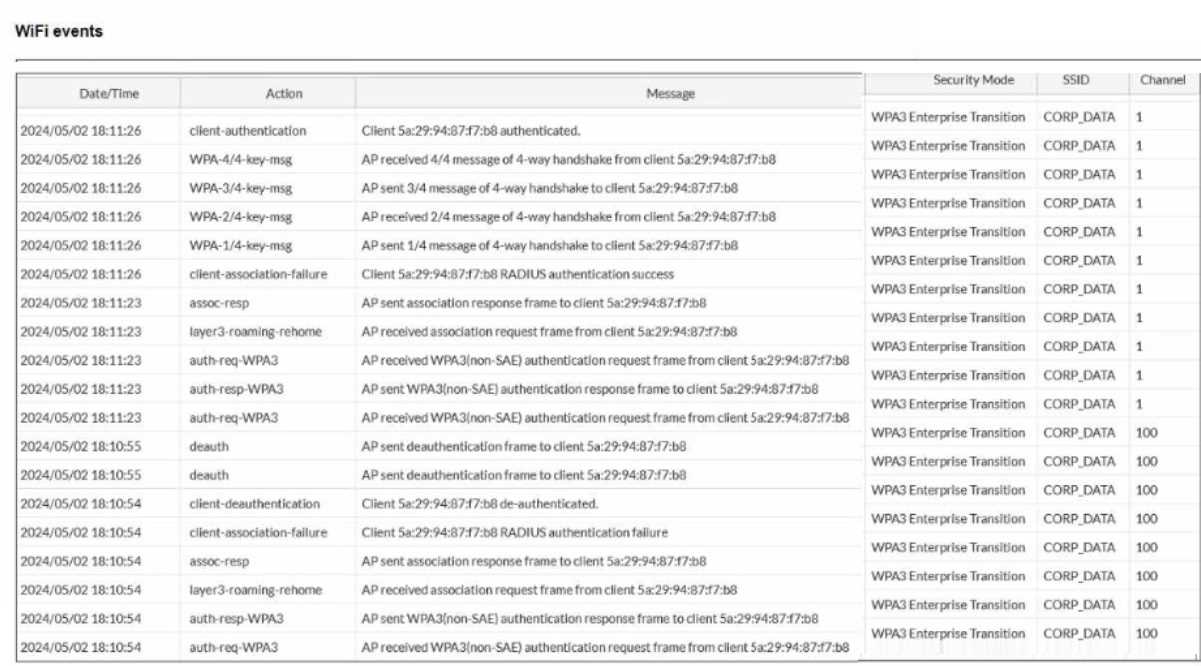
The wireless station with MAC address 5a:29:94:87:f7:b8 has made multiple attempts to connect to
the CORP.DATA SSID Despite client-association-failure event logs the wireless station connects on the
final attempt
Why did the wireless station fail to connect initially?
- A. The wireless station connected to SSID but failed RADIUS authentication
- B. The wireless controller unauthenticated the wireless station to prevent evil twin attacks
- C. The wireless station was incompatible with the 5 GHz radio band.
- D. The wireless station used invalid credentials on the failed attempt
Answer:
A
Question 12
What is the relationship between wireless channels and data transmission?
- A. The wider the channel the more data it can carry
- B. Data is transmitted over only one wireless channel at a time
- C. The more wireless channels, the more power consumption is required
- D. A wireless channel is allocated to transmit data unidirectionally
Answer:
A
Question 13
What protection does WPA3 wireless encryption provide over WPA2 for securing wireless networks?
- A. WPA3 uses 128-bit session key size
- B. WPA3 enforces only enterprise security mode
- C. WPA3 addresses the KRACK vulnerability
- D. WPA3 prevents legacy and deprecated wireless protocols from being used
Answer:
C
Question 14
Which security solution can you implement in the Security Fabric to identify and prevent threats?
- A. Integrated wireless network access
- B. Endpoint detection and response
- C. Compromised wireless client quarantine
- D. Indicator of attack system
Answer:
D
Question 15
Which wireless monitoring metric is required to optimize a wireless network?
- A. FortiAP running firmware status
- B. Amount of event togs generated
- C. Users count on the network
- D. Wireless channel utilization
Answer:
D