Fortinet FCP FWB AD 7 4 Exam Questions
Questions for the FCP FWB AD 7 4 were updated on : Feb 22 ,2026
Page 1 out of 3. Viewing questions 1-15 out of 36
Question 1
Refer to the exhibit.
FortiADC is applying SNAT to all inbound traffic going to the servers.
When an attack occurs, FortiWeb blocks traffic based on the 192.0.2.1 source IP address, which
belongs to FortiADC. This setup is breaking all connectivity and genuine clients are not able to access
the servers.
What can the administrator do to avoid this problem? (Choose two.)
- A. Enable and configure the Preserve Client IP setting on the client.
- B. No special configuration is required; connectivity will be re-established for all clients after the set timeout.
- C. Place FortiWeb in front of FortiADC.
- D. Enable and configure the Use X-Forwarded-For setting on FortiWeb.
Answer:
C, D
Explanation:
Place FortiWeb in front of FortiADC: This configuration change places FortiWeb between the client
and FortiADC, so that FortiWeb can directly inspect and protect the incoming traffic before FortiADC
applies SNAT (Source Network Address Translation). By placing FortiWeb in front, it will have access
to the real client IP addresses, and it will be able to properly identify and handle attack traffic
without blocking legitimate client traffic.
Enable and configure the Use X-Forwarded-For setting on FortiWeb: This setting allows FortiWeb to
extract the original client IP address from the X-Forwarded-For header in the HTTP request, which is
inserted by FortiADC when performing SNAT. With this setting enabled, FortiWeb will be able to
block traffic based on the original client IP address rather than the SNATed IP address (192.0.2.1),
preserving the accuracy of the security measures.
Question 2
Which three security features must you configure on FortiWeb to protect API connections? (Choose
three.)
- A. Single sign-on (SSO) authentication with Active Directory (AD)
- B. Machine learning (ML)-based API protection
- C. API schema validation
- D. API user authentication with SAML
- E. API user key enforcement
Answer:
B, C, E
Explanation:
Machine learning (ML)-based API protection: ML-based API protection helps detect and mitigate
abnormal behavior in API traffic, such as bot attacks or abuse, by learning and adapting to normal
traffic patterns.
API schema validation: API schema validation ensures that the API requests conform to the defined
schema (e.g., checking the structure, fields, and types in the API calls). This helps prevent attacks like
XML or JSON injection by ensuring only valid requests are processed.
API user key enforcement: Enforcing API user key authentication requires clients to provide valid API
keys, ensuring only authorized users can access the API. This is crucial for controlling access to the
API.
Question 3
In which two operating modes can FortiWeb modify HTTP packets? (Choose two.)
- A. True transparent proxy
- B. Virtual proxy
- C. Transparent inspection
- D. Reverse proxy
Answer:
B, D
Explanation:
Virtual proxy: In virtual proxy mode, FortiWeb acts as an intermediary between clients and the
server, and it can modify HTTP packets. It performs various security checks, such as inspecting and
filtering HTTP traffic before forwarding it to the web server.
Reverse proxy: In reverse proxy mode, FortiWeb sits between the client and the server, handling
incoming requests from clients, modifying or inspecting HTTP packets as needed, and forwarding
them to the backend servers.
Question 4
How are bot machine learning (ML) models different from API or anomaly detection models?
- A. Bot ML models analyze multiple connections overtime instead analyzing each connection as a single unit.
- B. Bot ML models detect only anomalies and not actual threats.
- C. Bot ML models inspect more types of connection properties.
- D. Bot ML models do not update models periodically from new data.
Answer:
A
Explanation:
Bot ML models analyze multiple connections over time instead of analyzing each connection as a
single unit: This is the key distinction. Bot ML models focus on analyzing patterns over a period of
time, looking at behavioral patterns across multiple requests or connections from the same source to
identify potential bot activity. Unlike traditional anomaly detection or API models that may focus on
single connections or individual transactions, bot detection typically examines aggregated behavior
to identify patterns indicative of bots, such as high-frequency requests or unusual traffic flows.
Question 5
Refer to the exhibit.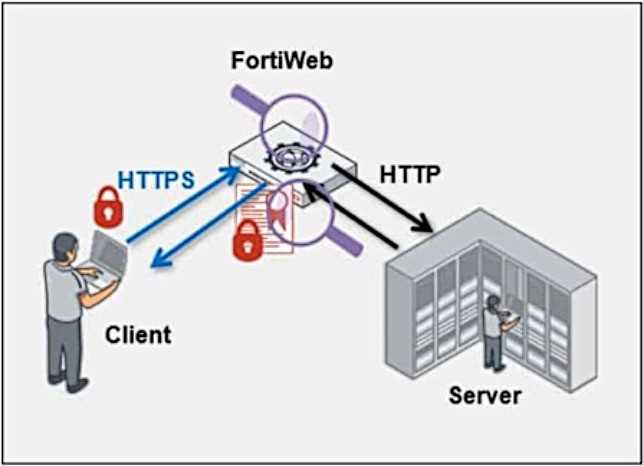
Which statement is true?
- A. FortiWeb cannot perform content inspection on the traffic because it is encrypted.
- B. FortiWeb is decrypting and re-encrypting the traffic.
- C. The server is not performing any cryptography on the traffic.
- D. The server is encrypting traffic being sent to the client.
Answer:
B
Explanation:
In the diagram, FortiWeb is positioned between the client and the server, handling encrypted HTTPS
traffic from the client and sending unencrypted HTTP traffic to the server. This indicates that
FortiWeb is performing SSL offloading, which means it is decrypting the HTTPS traffic from the client,
inspecting it, and then re-encrypting the traffic before forwarding it to the server.
Question 6
When is it possible to use a self-signed certificate, rather than one purchased from a commercial
certificate authority?
- A. If you are an enterprise whose employees use only mobile devices
- B. If you are a small business or home office
- C. If you are an enterprise whose computers all trust the active directory or CA server that signed the certificate
- D. If you are an enterprise whose resources do not need security or https connections
Answer:
C
Explanation:
A self-signed certificate is useful when all the devices in your network can be configured to trust it. In
this case, if your enterprise's computers trust the internal Active Directory or Certificate Authority
(CA) server that signed the certificate, the self-signed certificate can be used internally for HTTPS
connections without raising trust issues.
Question 7
Which two objects are required to configure a server policy in reverse proxy mode without content
routing? (Choose two.)
- A. Site publishing
- B. Protected hostname
- C. Virtual server
- D. Server pool
Answer:
B, C
Explanation:
Protected hostname: In reverse proxy mode, the protected hostname refers to the domain or
hostname that FortiWeb will protect. It specifies which hostname FortiWeb is acting as a reverse
proxy for, and is required for the server policy configuration.
Virtual server: A virtual server is a logical representation of a web server that FortiWeb handles. It's
required to configure how traffic is routed to the protected resources in reverse proxy mode.
Question 8
What are two results of enabling monitor mode on FortiWeb? (Choose two.)
- A. It does not affect denial-of-service (DoS) protection profile actions to rate limit traffic.
- B. It uses the default action for all profiles and, depending on the configuration, blocks or allows traffic.
- C. It does not affect any HTML rewriting or redirection actions in web protection profiles.
- D. It overrides all usual profile actions. FortiWeb accepts all requests and generates alert email or log messages only for violations.
Answer:
A, D
Explanation:
It does not affect denial-of-service (DoS) protection profile actions to rate limit traffic: Monitor mode
allows FortiWeb to monitor traffic without impacting the protection profile actions, including rate
limiting in the DoS protection profiles. Traffic will still be subjected to DoS protection actions like rate
limiting, but FortiWeb will not block traffic unless a violation occurs.
It overrides all usual profile actions. FortiWeb accepts all requests and generates alert email or log
messages only for violations: In monitor mode, FortiWeb will allow all traffic through and generate
logs or alerts for any violations, but it will not take active actions like blocking requests or redirecting
traffic. This allows you to observe the traffic patterns and potential threats without disrupting normal
operations.
Question 9
Refer to the exhibit.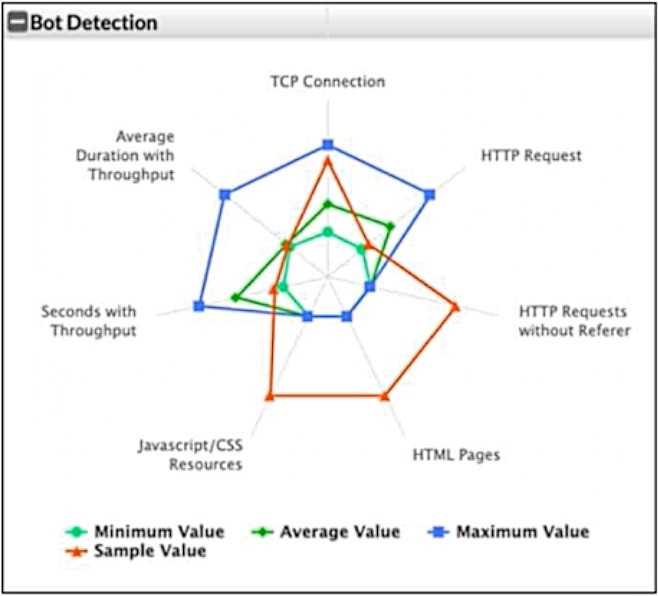
What can you conclude from this support vector machine (SVM) plot of a potential bot connection?
- A. The connection is normal and within the expected averages.
- B. The connection uses too much bandwidth.
- C. The connection uses an excessive amount of TCP connections, but is harmless.
- D. The connection is possibly a bot.
Answer:
D
Explanation:
In the SVM plot of potential bot activity, you can see that the sample value (orange) is significantly
different from the average value (green) and the maximum value (blue) in most of the metrics. This
suggests unusual or abnormal behavior, indicating that the connection might be a bot. Typically, bots
exhibit patterns that diverge from normal user activity, such as higher frequencies of certain types of
requests, abnormal throughput, or an unusual pattern of HTTP requests (such as requests without
referers or excessive TCP connections).
Question 10
Review the following configuration: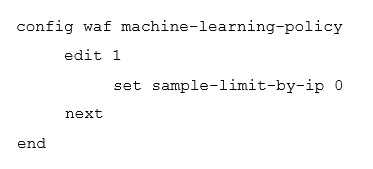
Which result would you expect from this configuration setting?
- A. When machine learning (ML) is in its running phase, FortiWeb will accept a set number of samples from the same source IP address.
- B. When ML is in its running phase, FortiWeb will accept an unlimited number of samples from the same source IP address.
- C. When ML is in its collecting phase, FortiWeb will accept an unlimited number of samples from the same source IP address.
- D. When ML is in its collecting phase, FortiWeb will not accept any samples from any IP addresses.
Answer:
B
Explanation:
In the configuration, the command set sample-limit-by-ip 0 disables the sample limit for any specific
IP address. This means that during the machine learning (ML) running phase, FortiWeb will not limit
the number of samples it accepts from the same IP address. Setting this to 0 effectively removes any
restrictions on the number of samples from a given IP address.
Question 11
An administrator notices multiple IP addresses attempting to log in to an application frequently,
within a short time period. They suspect attackers are attempting to guess user passwords for a
secure application.
What is the best way to limit this type of attack on FortiWeb, while still allowing legitimate traffic
through?
- A. Blocklist any suspected IPs.
- B. Configure a brute force login custom policy.
- C. Rate limit all connections from suspected IP addresses.
- D. Block the IP address at the border router.
Answer:
B
Explanation:
The best way to limit brute force login attacks on FortiWeb is to configure a brute force login custom
policy. FortiWeb provides the ability to detect and mitigate brute force login attempts by
automatically limiting the number of failed login attempts within a specific time period. This
approach allows you to block or rate limit suspicious IP addresses while still allowing legitimate users
access, based on your configuration.
Question 12
Which two statements about running a vulnerability scan are true? (Choose two.)
- A. You should run the vulnerability scan during a maintenance window.
- B. You should run the vulnerability scan multiple times so it can automatically update the scan parameters.
- C. You should run the vulnerability scan in a test environment.
- D. You should run the vulnerability scan on the live website to get accurate results.
Answer:
A, C
Explanation:
You should run the vulnerability scan during a maintenance window: Running a vulnerability scan
during a maintenance window minimizes the risk of affecting normal operations. Scans can be
resource-intensive and may cause disruptions if run during peak hours or when the system is in use.
You should run the vulnerability scan in a test environment: It is important to run the vulnerability
scan in a test environment first to avoid unintended disruptions on the live system. This helps to
identify potential issues or false positives without impacting production systems.
Question 13
Which two items can be defined in a FortiWeb XML Protection Rule? (Choose two.)
- A. API key
- B. IXML Schema
- C. Web protection profile
- D. Request URL
Answer:
B, D
Explanation:
XML Schema: In FortiWeb, XML protection rules allow you to define an XML Schema to validate the
structure and content of incoming XML documents. This helps protect against attacks like XML
injection by ensuring that only well-formed XML requests are processed.
Request URL: You can define a request URL as part of an XML protection rule to specify the URL
pattern for which the rule should apply. This allows you to apply different XML protection rules to
different endpoints or resources based on the URL.
Question 14
What are two possible impacts of a DoS attack on your web server? (Choose two.)
- A. The web application starts accepting unencrypted traffic.
- B. The web application is unable to accept any more connections because of network socket exhaustion.
- C. The web application server is unable to accept new client sessions due to memory exhaustion.
- D. The web application server database is compromised with data theft.
Answer:
B, C
Explanation:
The web application is unable to accept any more connections because of network socket
exhaustion: A Denial of Service (DoS) attack often floods the web server with an overwhelming
number of requests, leading to network socket exhaustion. This can prevent the server from
accepting new legitimate connections, effectively disrupting service.
The web application server is unable to accept new client sessions due to memory exhaustion: DoS
attacks can consume a significant amount of server memory, causing memory exhaustion. This
results in the web application being unable to accept new client sessions or handle requests
properly.
Question 15
In SAML deployments, which server contains user authentication credentials (username/password)?
- A. Identity provider
- B. Service provider
- C. User database
- D. Authentication client
Answer:
A
Explanation:
In SAML (Security Assertion Markup Language) deployments, the Identity Provider (IdP) is
responsible for storing and managing user authentication credentials, such as usernames and
passwords. The IdP authenticates the user and then issues a SAML assertion to the Service Provider
(SP), which allows the user to access services without needing to re-enter credentials.