Fortinet FCP FSM AN 7 2 Exam Questions
Questions for the FCP FSM AN 7 2 were updated on : Feb 22 ,2026
Page 1 out of 3. Viewing questions 1-15 out of 32
Question 1
Refer to the exhibit.
If you group the events by User, Source IP, and Count attributes, how many results will FortiSIEM
display?
- A. Two
- B. Six
- C. Three
- D. Five
- E. Four
Answer:
B
Explanation:
Grouping by User, Source IP, and Count means that each unique combination of those three
attributes will be treated as a separate result. In the table, all six rows have distinct combinations of
User, Source IP, and Count - so FortiSIEM will display 6 results.
Question 2
Refer to the exhibit.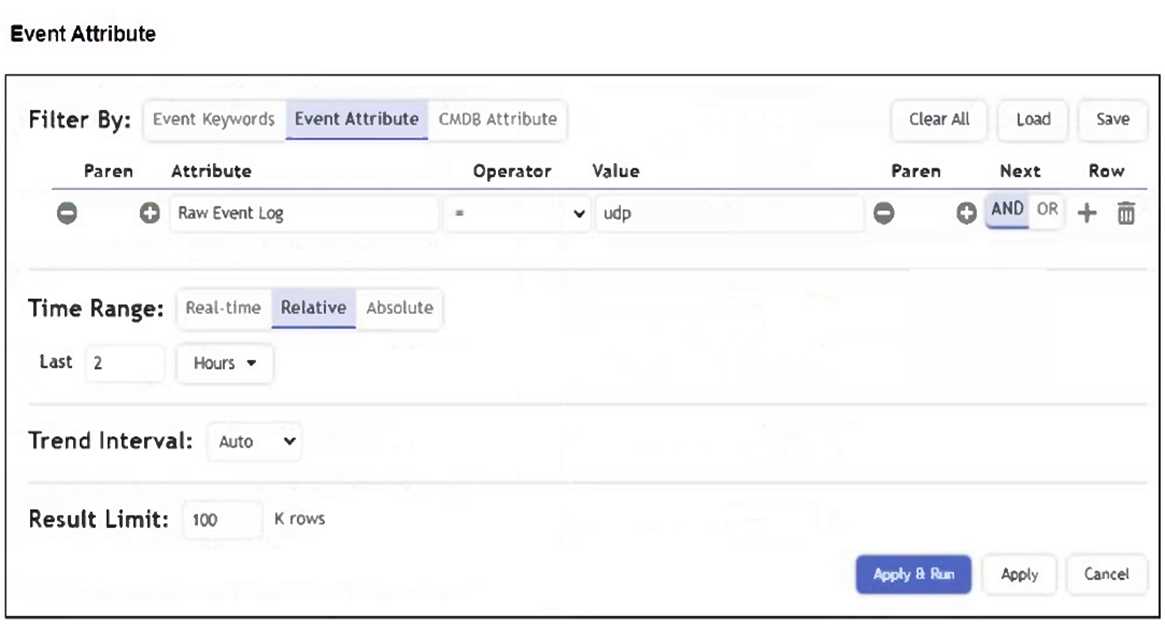
A FortiSIEM device is receiving syslog events from a FortiGate firewall. The FortiSIEM analyst is trying
to search the raw event logs for the last two hours that contain the keyword "udp". However, they
are getting no results from the search, which they know should be available. Based on the filter
shown in the exhibit, why are there no search results?
- A. The analyst selected AND in the Next column. This is the wrong Boolean operator.
- B. The Time Range value should be set to Real-Time.
- C. The keyword is case sensitive. Instead of typing udp in the Value field, the analyst should type UDP.
- D. The analyst selected = in the Operator column. That is the wrong operator.
Answer:
D
Explanation:
The operator is set to "=", which performs an exact match on the entire raw event log, not a
substring search. To find logs that contain the keyword "udp", the analyst should use the CONTAIN
operator instead. This will return all logs where "udp" appears anywhere in the raw log message.
Question 3
How does FortiSIEM update the incident table if a performance rule triggers repeatedly?
- A. FortiSIEM changes the incident status to Repeated, and updates the Last Seen timestamp.
- B. FortiSIEM updates the Incident Count value and Last Seen timestamp.
- C. FortiSIEM generates a new incident based on the Rule Frequency value, and updates the First Seen and Last Seen timestamps.
- D. FortiSIEM generates a new incident each time the rule triggers, and updates the First Seen and Last Seen timestamps.
Answer:
B
Explanation:
When a performance rule triggers repeatedly, FortiSIEM updates the existing incident by
incrementing the Incident Count and refreshing the Last Seen timestamp. This avoids flooding the
incident table with duplicates while still tracking repeated occurrences.
Question 4
Refer to the exhibit.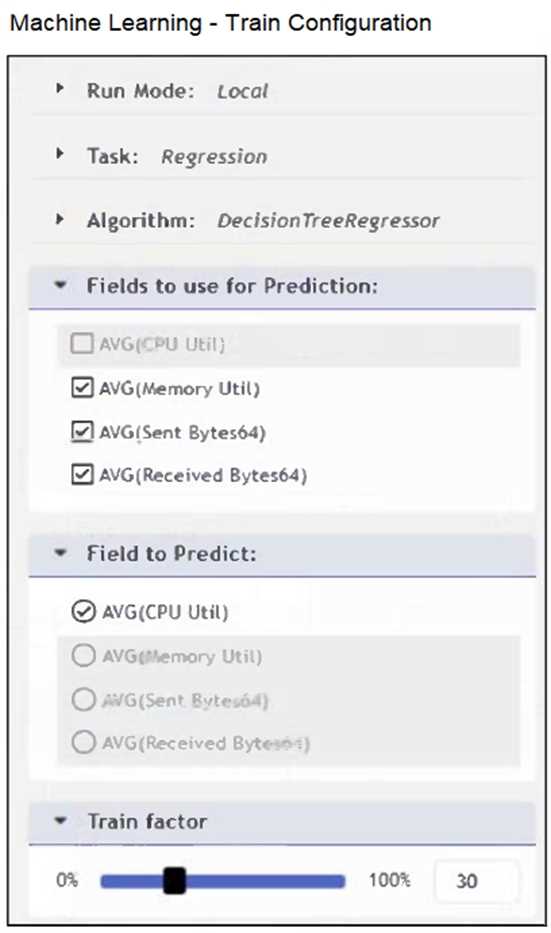
The configuration shown in the exhibit is incorrect.
What must you change to allow this configuration to be successfully applied to FortiSIEM?
- A. The Train factor must be 70% or greater.
- B. Run Mode must be set to ML.
- C. Only one AVG type field must be selected under Fields to use for Prediction.
- D. The selection in Fields to use for Prediction and Field to Predict must match.
Answer:
B
Explanation:
The Run Mode is set to Local, which is not valid for training machine learning models in FortiSIEM. To
apply this configuration correctly, the Run Mode must be set to ML, which enables proper model
training and prediction using selected fields.
Question 5
Refer to the exhibit.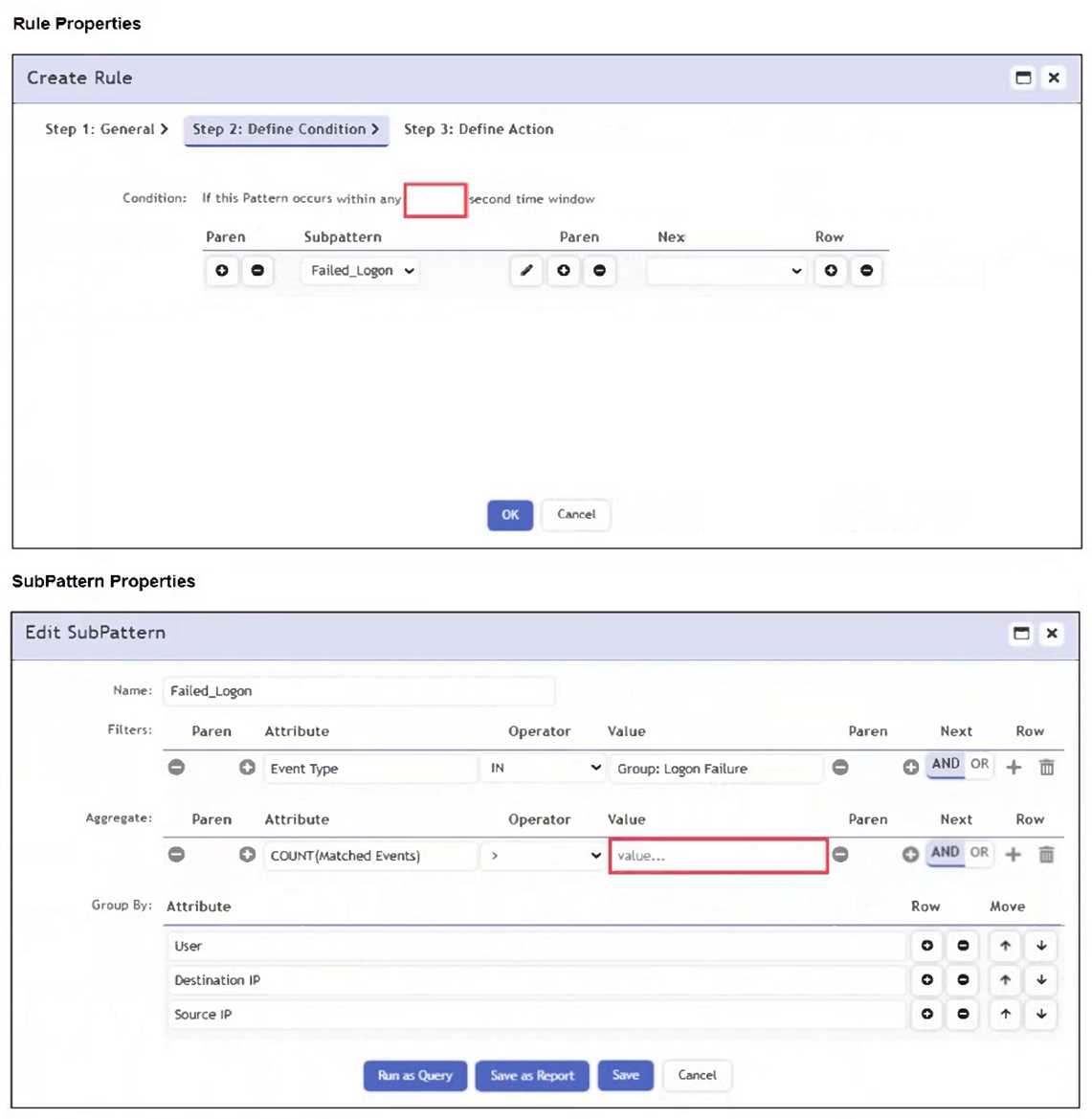
An analyst wants the rule shown in the exhibit to trigger when three failed login attempts occur
within three minutes.
What should the values be for the condition time window and aggregate count?
- A. Time window 180 seconds, aggregate count 3
- B. Time window 180 seconds, aggregate count 2
- C. Time window 90 seconds, aggregate count 3
- D. Time window 90 seconds, aggregate count 2
Answer:
A
Explanation:
To detect three failed login attempts within three minutes, you must set the aggregate count to 3 in
the subpattern and the time window to 180 seconds in the rule condition. This ensures the rule
triggers only if three or more failed logins occur in that timeframe.
Question 6
Which information can FortiSIEM retrieve from FortiClient EMS through an API connection?
- A. Host software versions
- B. FortiSIEM license
- C. Host login credentials
- D. ZTNA tags
Answer:
D
Explanation:
FortiSIEM can retrieve ZTNA tags from FortiClient EMS through an API connection, enabling dynamic
user and device classification for policy enforcement and incident response.
Question 7
Refer to the exhibit.
If a rule containing the automation policy shown in the exhibit triggers, what will happen?
- A. Associated source IP addresses will be blocked on devices in the Aviation organization.
- B. Associated source IP addresses will be blocked on all FortiGate firewalls.
- C. Associated source IP addresses will be blocked on devices in the Network CMDB group.
- D. Associated source IP addresses will be blocked on two FortiGate firewalls.
Answer:
D
Explanation:
The automation policy is configured to run a remediation script named "Fortinet FortiOS - Block
Source IP FortiOS via API". It specifies enforcement on two FortiGate devices: FortiGate508 and
FortiGate90D. Therefore, associated source IP addresses will be blocked on those two FortiGate
firewalls only.
Question 8
When configuring anomaly detection machine learning, in which step must you select the fields to
analyze?
- A. Design
- B. Schedule
- C. Prepare Data
- D. Train
Answer:
C
Explanation:
In the Prepare Data step of configuring anomaly detection in FortiSIEM, you must select the fields to
analyze. This step defines the input features that the machine learning model will evaluate during
training and detection.
Question 9
Refer to the exhibit.
According to the automation policy configuration shown in the exhibit, what happens if an
associated rule triggers?
- A. FortiSIEM runs the remediation script, because that takes precedence over all other options.
- B. FortiSIEM performs all selected actions.
- C. FortiSIEM fails to the integration policy, because no policy is defined.
- D. FortiSIEM sends an email, because that is first on the list.
Answer:
B
Explanation:
When an associated rule triggers, FortiSIEM performs all selected actions in the automation policy. In
this case, it will send an email/SMS/webhook, run the remediation script, invoke the integration
policy (even if none is currently defined), and create a case. All checked actions are executed.
Question 10
Refer to the exhibit.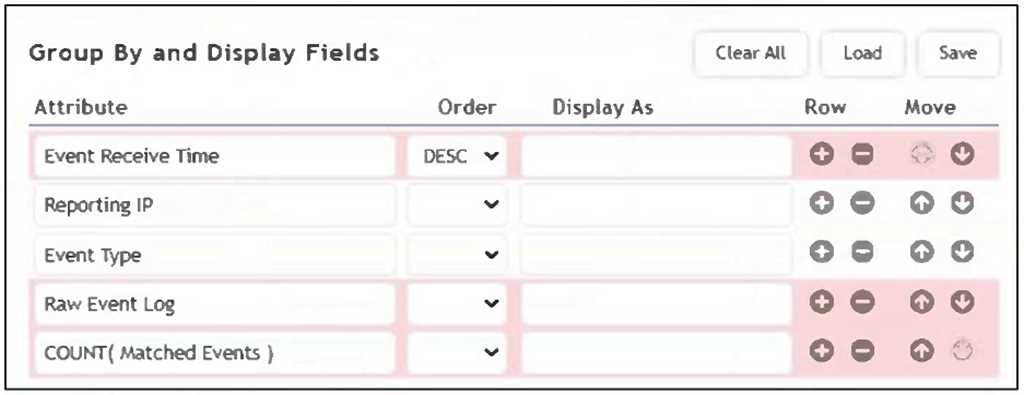
As shown in the exhibit, why are some of the fields highlighted in red?
- A. Unique values cannot be grouped B.
- B. The attribute COUNT(Matched Events) is an invalid expression.
- C. No RAW Event Log attribute information is available.
- D. The Event Receive Time attribute is not available for logs.
Answer:
A
Explanation:
The fields are highlighted in red because unique values such as Event Receive Time and Raw Event
Log cannot be used in group-by operations. Grouping requires aggregatable or consistent values
across events, while these fields are unique to each event, making them incompatible for grouping.
Question 11
How can you query the configuration management database (CMDB) in an analytics search?
- A. Click Value > Select from CMDB.
- B. On the CMDB tab, select an entry, and then click Create Search.
- C. On the Admin tab, click CMDB Search.
- D. Click Attribute > Select from CMDB.
Answer:
A
Explanation:
In an analytics search, you can query the CMDB by clicking Value > Select from CMDB, which allows
you to choose values directly from CMDB entries for the selected attribute, enabling precise filtering
based on asset data.
Question 12
Refer to the exhibit.
Which two conditions will match this rule and subpatterns? (Choose two.)
- A. A user using RDP over SSL VPN fails to log in to an application five times.
- B. A user runs a brute force password cracker against an RDP server.
- C. A user fails twice to log in when connecting through RDP.
- D. A user connects to the wrong IP address for an RDP session five times.
Answer:
A, B
Explanation:
The user initiates an RDP session (Subpattern 1) and then fails to log in multiple times (Subpattern 2
with COUNT(Matched Events) >= 3) - both from the same Source IP and User within 300 seconds.
The brute force attempts typically involve a successful RDP connection followed by multiple failed
logins, satisfying the sequence and grouping conditions in the rule.
Question 13
Refer to the exhibit.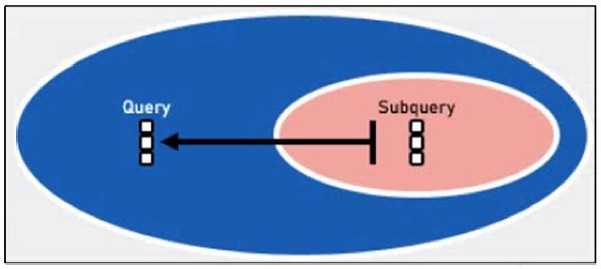
Which two lookup types can you reference as the subquery in a nested analytics query? (Choose
two.)
- A. LDAP Query
- B. CMDB Query
- C. SNMP Query
- D. Event Query
Answer:
C, D
Explanation:
In FortiSIEM nested analytics queries, you can reference both CMDB Queries and Event Queries as
subqueries. These allow correlation between CMDB data and event data for advanced detection use
cases.
Question 14
Which items are used to define a subpattern?
- A. Filters, Aggregate, Group By definitions
- B. Filters, Aggregate, Time Window definitions
- C. Filters, Group By, Threshold definitions
- D. Filters, Threshold, Time Window definitions
Answer:
A
Explanation:
A subpattern in FortiSIEM is defined using Filters to match specific events, Aggregate conditions to
apply statistical thresholds (e.g., COUNT), and Group By attributes to segment data for evaluation.
These three components collectively determine how the subpattern functions.
Question 15
Refer to the exhibit.
An analyst is trying to identify an issue using an expression based on the Expression Builder settings
shown in the exhibit; however, the error message shown in the exhibit indicates that the expression
is invalid.
What is the correct syntax to create an expression that generates a total count of matched events?
- A. COUNT(Matched Events)
- B. (COUNT) Matched Events
- C. Matched Events (COUNT)
- D. Matched Events COUNT()
Answer:
A
Explanation:
The correct syntax is COUNT(Matched Events) - with proper capitalization and spacing - to generate a
total count of matched events. The error in the exhibit likely stems from a formatting issue (e.g.,
lowercase count() or incorrect spacing), not the logical structure of the expression.