Fortinet FCP FML AD 7 4 Exam Questions
Questions for the FCP FML AD 7 4 were updated on : Feb 22 ,2026
Page 1 out of 4. Viewing questions 1-15 out of 53
Question 1
Refer to the exhibit which shows a topology diagram of a FortiMail cluster deployment.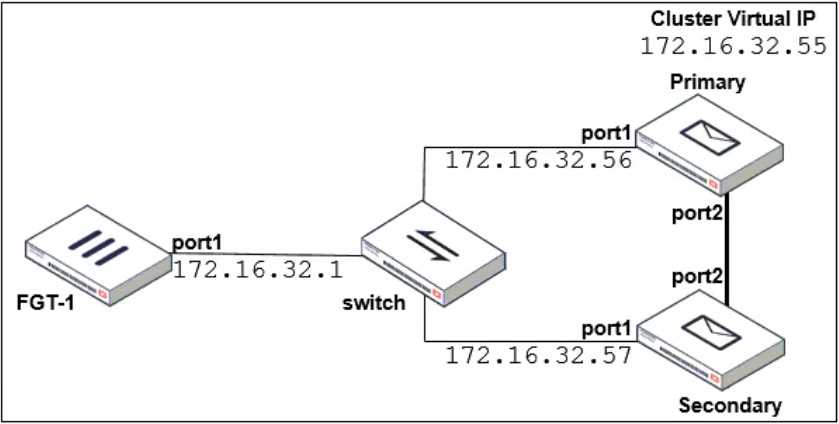
Which IP address must the DNS MX record for this organization resolve to?
- A. 1172 16 32 57
- B. 172.16.32.56
- C. 172.16.32.55
- D. 172.16.32.1
Answer:
C
Question 2
While reviewing logs, an administrator discovers that an incoming email was processed using policy
IDs 0:4:9:INTERNAL.
Which two statements describe what this policy ID means? (Choose two.)
- A. Access control policy number 9 was used.
- B. The FortiMail configuration is missing an access delivery rule.
- C. The email was processed using IP-based policy ID 4.
- D. FortiMail is applying the default behavior for relaying inbound email.
Answer:
CD
Question 3
Refer to the exhibit which shows an nslookup output of MX records of the example.com domain.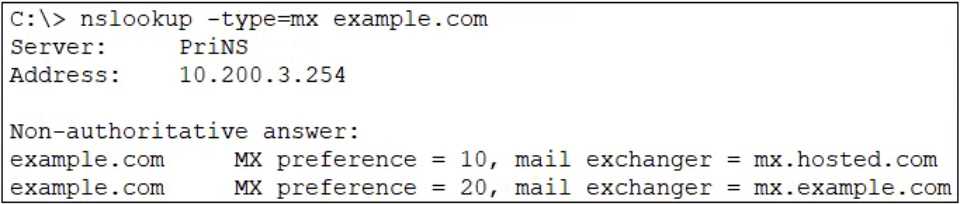
Which two MTA selection behaviors for the example.com domain are correct? (Choose two.)
- A. mx.example.com will receive approximately twice the number of email as mx.hosted.com because of its preference value.
- B. The primary MTA for the example.com domain is mx.hosted.com.
- C. The external MTAs will send email to mx.example.com only if mx.hosted.com is unreachable.
- D. The PriNS server should receive all email for the example.com domain.
Answer:
B, C
Question 4
Which statement about how impersonation analysis identifies spoofed email addresses is correct?
- A. It uses behavior analysis to detect spoofed addresses.
- B. It uses DMARC validation to detect spoofed addresses.
- C. It maps the display name to the correct recipient email address
- D. It uses SPF validation to detect spoofed addresses.
Answer:
B
Question 5
Which two FortiMail antispam techniques can you use to combat zero-day spam? (Choose two.)
- A. IP reputation
- B. Spam outbreak protection
- C. DNSBL
- D. Behavior analysis
Answer:
A, B
Question 6
Refer to the exhibits, which display a topology diagram (Topology) and two FortiMail device
configurations (FML1 Configuration and FML2 Configuration).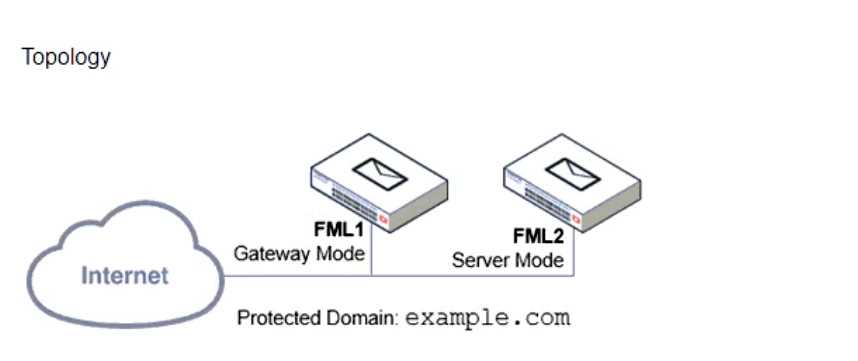
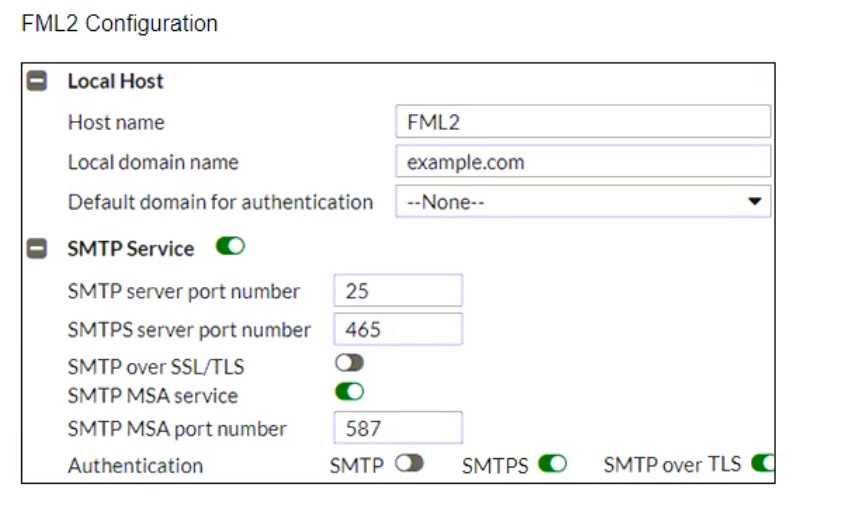
What is the expected outcome of SMTP sessions sourced from FML1 and destined for FML2?
- A. FML1 will fail to establish any connection with FML2.
- B. FML1 will attempt to establish an SMTPS session with FML2. but fail and revert to standard SMTP.
- C. FML1 will send the STARTTLS command in the SMTP session, which will be rejected by FML2.
- D. FML1 will successfully establish an SMTPS session with FML2.
Answer:
D
Question 7
Refer to the exhibit, which shows an inbound recipient policy.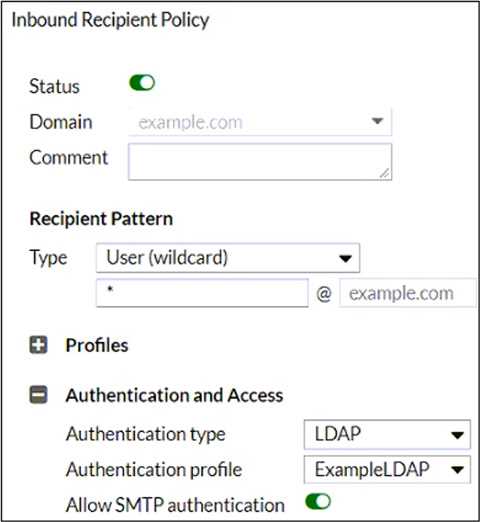
After creating the policy shown in the exhibit, an administrator discovers that clients can send
unauthenticated emails using SMTP.
What must the administrator do to enforce authentication?
- A. Move this incoming recipient policy to the top of the list.
- B. Configure a matching IP policy with the exclusive flag enabled.
- C. Configure an access delivery rule to enforce authentication.
- D. Configure an access receive rule to verify authentication status.
Answer:
D
Question 8
Refer to the exhibit which shows a detailed history log view.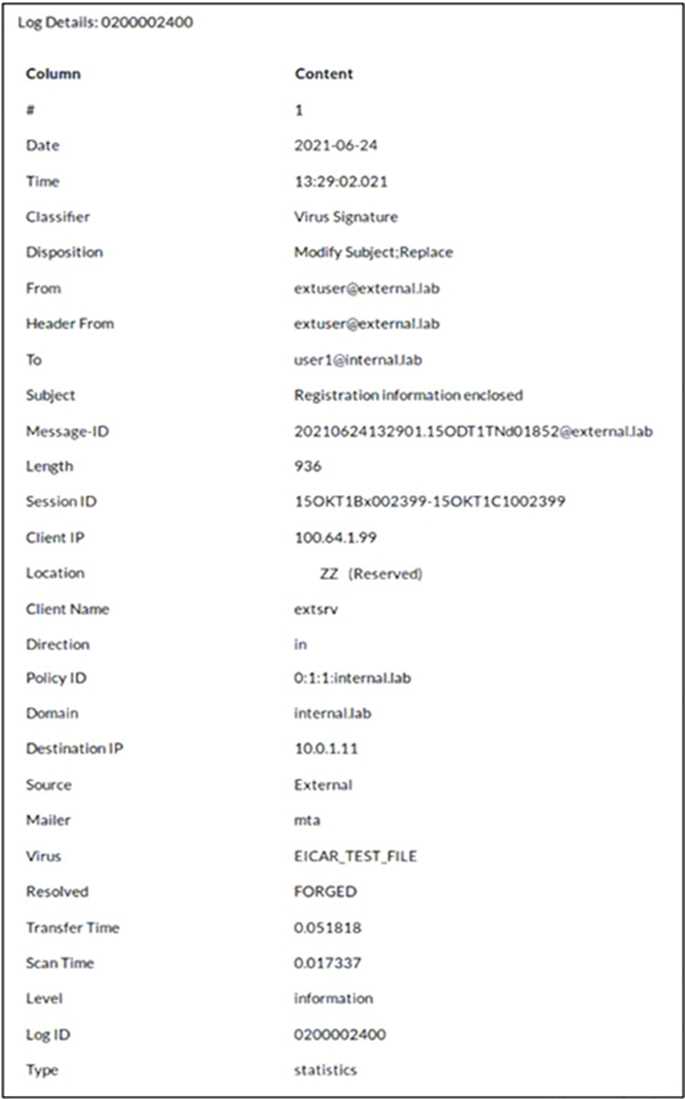
Which two actions did FortiMail take on this email message? (Choose two.)
- A. FortJMail replaced the virus content with a message
- B. FortiMail modified the subject of the email message.
- C. FortiMail forwarded the email to User 1 without scanning.
- D. FortiMail sent the email message to User 1's personal quarantine.
Answer:
A, B
Question 9
A FortiMail administrator is investigating a sudden increase in DSNs being delivered to their
protected domain. After searching the logs, the administrator identifies that the DSNs were not
generated because of any outbound email sent from their organization.
Which FortiMail antispam technique can the administrator use to prevent this scenario?
- A. FortiGuard IP Reputation
- B. Spoofed header detection
- C. Spam outbreak protection
- D. Bounce address tag validation
Answer:
D
Question 10
In which FortiMail configuration object can you assign an outbound session profile?
- A. Outbound recipient policy
- B. Inbound recipient policy
- C. IP policy
- D. Access delivery rule
Answer:
C
Question 11
What are two disadvantages of configuring the dictionary and DLP scan rule aggressiveness too high?
(Choose two.)
- A. High aggressiveness scan settings do not support executable file types.
- B. It is more resource intensive
- C. More false positives could be detected.
- D. FortiMail requires more disk space for the additional rules.
Answer:
B, C
Question 12
Which item is a supported one-time secure token for IBE authentication?
- A. FortiToken
- B. Certificate
- C. SMS
- D. Security question
Answer:
D
Question 13
In which two places can the maximum email size be overridden on FortiMail? (Choose two.)
- A. IP Policy configuration
- B. Protected Domain configuration
- C. Resource Profile configuration
- D. Session Profile configuration
Answer:
B, C
Question 14
Refer to the exhibit which displays a list of IBE users on a FortiMail device.
Which statement describes the pre-registered status of the IBE user [email protected]?
- A. The user has received an IBE notification email, but has not accessed the HTTPS URL or attachment yet.
- B. The user was registered by an administrator in anticipation of IBE participation.
- C. The user account has been de-activated, and the user must register again the next time they receive an IBE email.
- D. The user has completed the IBE registration process, but has not yet accessed their IBE email.
Answer:
A
Question 15
Refer to the exhibit which displays a topology diagram.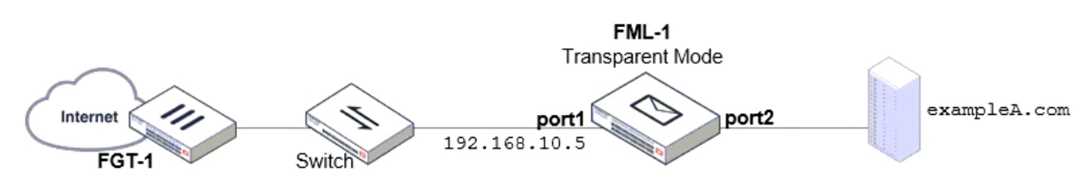
Which two statements describe the built-in bridge functionality on a transparent mode FortiMail?
(Choose two.)
- A. If port1. is required to process SMTP traffic, it must be configured as a routed interface.
- B. All bridge member interfaces belong to the same subnet as the management IP.
- C. The management IP is permanently tied to port1, and port1 cannot be removed from the bridge.
- D. Any bridge member interface can be removed from the bridge and configured as a routed interface.
Answer:
B, C