Fortinet FCP FGT AD 7 6 Exam Questions
Questions for the FCP FGT AD 7 6 were updated on : Feb 22 ,2026
Page 1 out of 4. Viewing questions 1-15 out of 50
Question 1
Which three pieces of information does FortiGate use to identify the hostname of the SSL server
when SSL certificate inspection is enabled? (Choose three.)
- A. The host field in the HTTP header.
- B. The server name indication (SNI) extension in the client hello message.
- C. The subject alternative name (SAN) field in the server certificate.
- D. The subject field in the server certificate.
- E. The serial number in the server certificate.
Answer:
B, C, D
Explanation:
When SSL certificate inspection is enabled on a FortiGate device, the system uses the following three
pieces of information to identify the hostname of the SSL server:
Server Name Indication (SNI) extension in the client hello message (B): The SNI is an extension in the
client hello message of the SSL/TLS protocol. It indicates the hostname the client is attempting to
connect to. This allows FortiGate to identify the server's hostname during the SSL handshake.
Subject Alternative Name (SAN) field in the server certificate (C): The SAN field in the server
certificate lists additional hostnames or IP addresses that the certificate is valid for. FortiGate
inspects this field to confirm the identity of the server.
Subject field in the server certificate (D): The Subject field contains the primary hostname or domain
name for which the certificate was issued. FortiGate uses this information to match and validate the
server’s identity during SSL certificate inspection.
The other options are not used in SSL certificate inspection for hostname identification:
Host field in the HTTP header (A): This is part of the HTTP request, not the SSL handshake, and is not
used for SSL certificate inspection.
Serial number in the server certificate (E): The serial number is used for certificate management and
revocation, not for hostname identification.
Reference
FortiOS 7.4.1 Administration Guide -
SSL/SSH Inspection
, page 1802.
FortiOS 7.4.1 Administration Guide -
Configuring SSL/SSH Inspection Profile
, page 1799.
Question 2
Refer to the exhibit.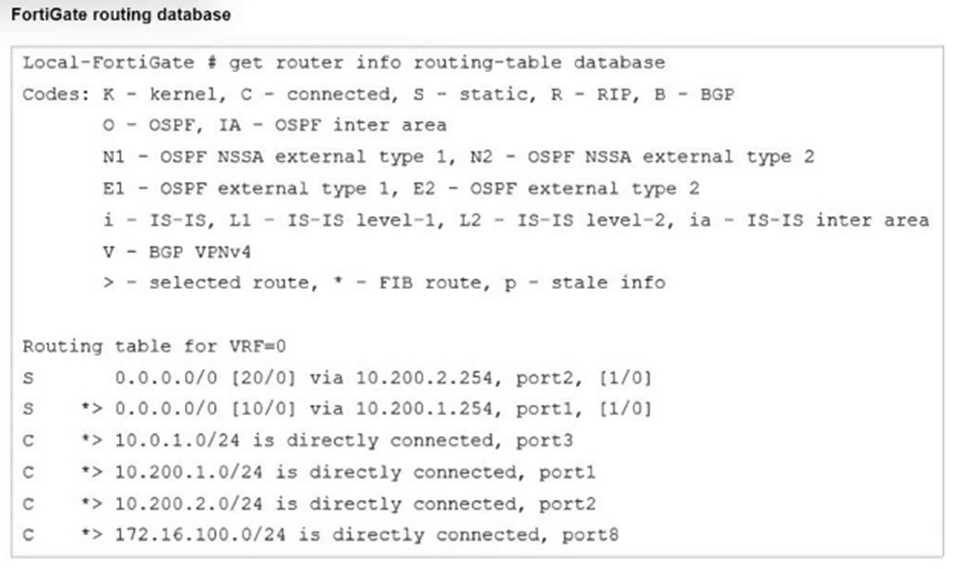
Which two statements are true about the routing entries in this database table? (Choose two.)
- A. All of the entries in the routing database table are installed in the FortiGate routing table.
- B. The port2 interface is marked as inactive.
- C. Both default routes have different administrative distances.
- D. The default route on port2 is marked as the standby route.
Answer:
C, D
Explanation:
The routing table in the exhibit shows two default routes (0.0.0.0/0) with different administrative
distances:
The default route through port2 has an administrative distance of 20.
The default route through port1 has an administrative distance of 10.
Administrative distance determines the priority of the route; a lower value is preferred. Here, the
route through port1 with an administrative distance of 10 is the preferred route. The route through
port2 with an administrative distance of 20 acts as a standby or backup route. If the primary route
(port1) fails or is unavailable, traffic will then be routed through port2.
Regarding the statement that the port2 interface is marked as inactive, there is no indication in the
routing table that port2 is inactive. Similarly, all the routes displayed are not necessarily installed in
the FortiGate routing table, as the table could include both active and backup routes.
Reference:
FortiOS 7.4.1 Administration Guide: Default route configuration
FortiOS 7.4.1 Administration Guide: Routing table explanation
Question 3
Refer to the exhibit.
Refer to the exhibits.
An administrator configured the Web Filter Profile to block access to all social networking sites
except Facebook. However, when users try to access Facebook.com, they are redirected to a
FortiGuard web filtering block page.
Based on the exhibits, which configuration change must the administrator make to allow Facebook
while blocking all other social networking sites?
- A. Change the Feature set of Web Filter Profile as Proxy-based.
- B. Set the Action as Exempt for www.facebook.com in the Static URL Filter.
- C. Change the type as Simple in the Static URL Filter section.
- D. Set the Social Networking action as warning in the FortiGuard Category Based Filter.
Answer:
B
Question 4
You are encountering connectivity problems caused by intermediate devices blocking IPsec traffic.
In which two ways can you effectively resolve the problem? (Choose two.)
- A. You should use the protocol IKEv2.
- B. You can use SSL VPN tunnel mode to prevent problems with blocked ESP and UDP ports (500 or 4500).
- C. You can configure a hub-and-spoke topology with SSL VPN tunnels to bypass blocked UDP ports.
- D. You can turn on fragmentation to fix large certificate negotiation problems.
Answer:
B, D
Question 5
Refer to the exhibit.
Refer to the exhibits.
You have implemented the application sensor and the corresponding firewall policy as shown in the
exhibits.
Which two factors can you observe from these configurations? (Choose two.)
- A. YouTube search is allowed based on the Google Application and Filter override settings.
- B. YouTube access is blocked based on Excessive-Bandwidth Application and Filter override settings.
- C. Facebook access is allowed but you cannot play Facebook videos based on Video/Audio category filter settings.
- D. Facebook access is blocked based on the category filter settings.
Answer:
B, D
Question 6
Refer to the exhibit.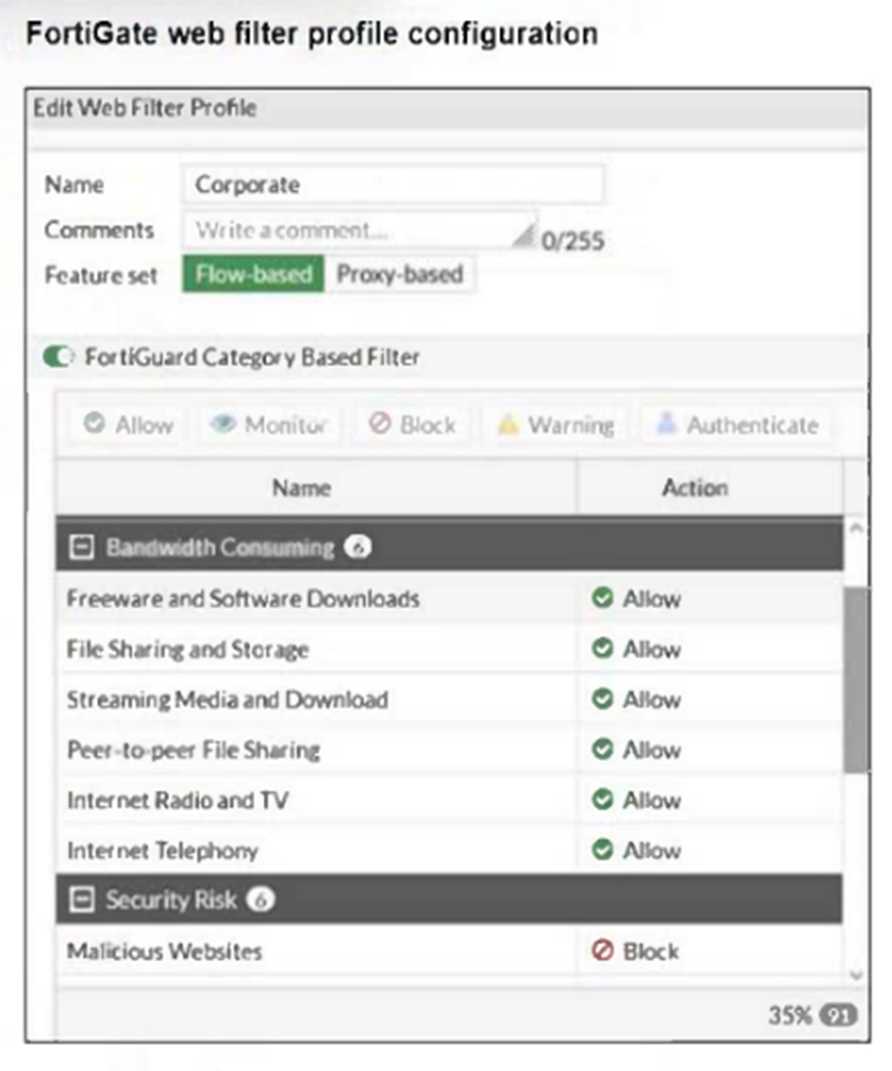
The exhibit shows the FortiGuard Category Based Filter section of a corporate web filter profile.
An administrator must block access to download.com, which belongs to the Freeware and Software
Downloads category. The administrator must also allow other websites in the same category.
What are two solutions for satisfying the requirement? (Choose two.)
- A. Configure a static URL filter entry for download.com with Type and Action set to Wildcard and Block, respectively.
- B. Configure a web override rating for download.com and select Malicious Websites as the subcategory.
- C. Configure a separate firewall policy with action Deny and an FQDN address object for*.download.com as destination address.
- D. Set the Freeware and Software Downloads category Action to Warning.
Answer:
A, C
Explanation:
Creating a static URL filter to block download.com specifically allows blocking that site without
affecting the entire category.
Using a separate firewall policy with a Deny action for an FQDN address object matching
download.com can also block the site while allowing others in the same category.
Question 7
Refer to the exhibits.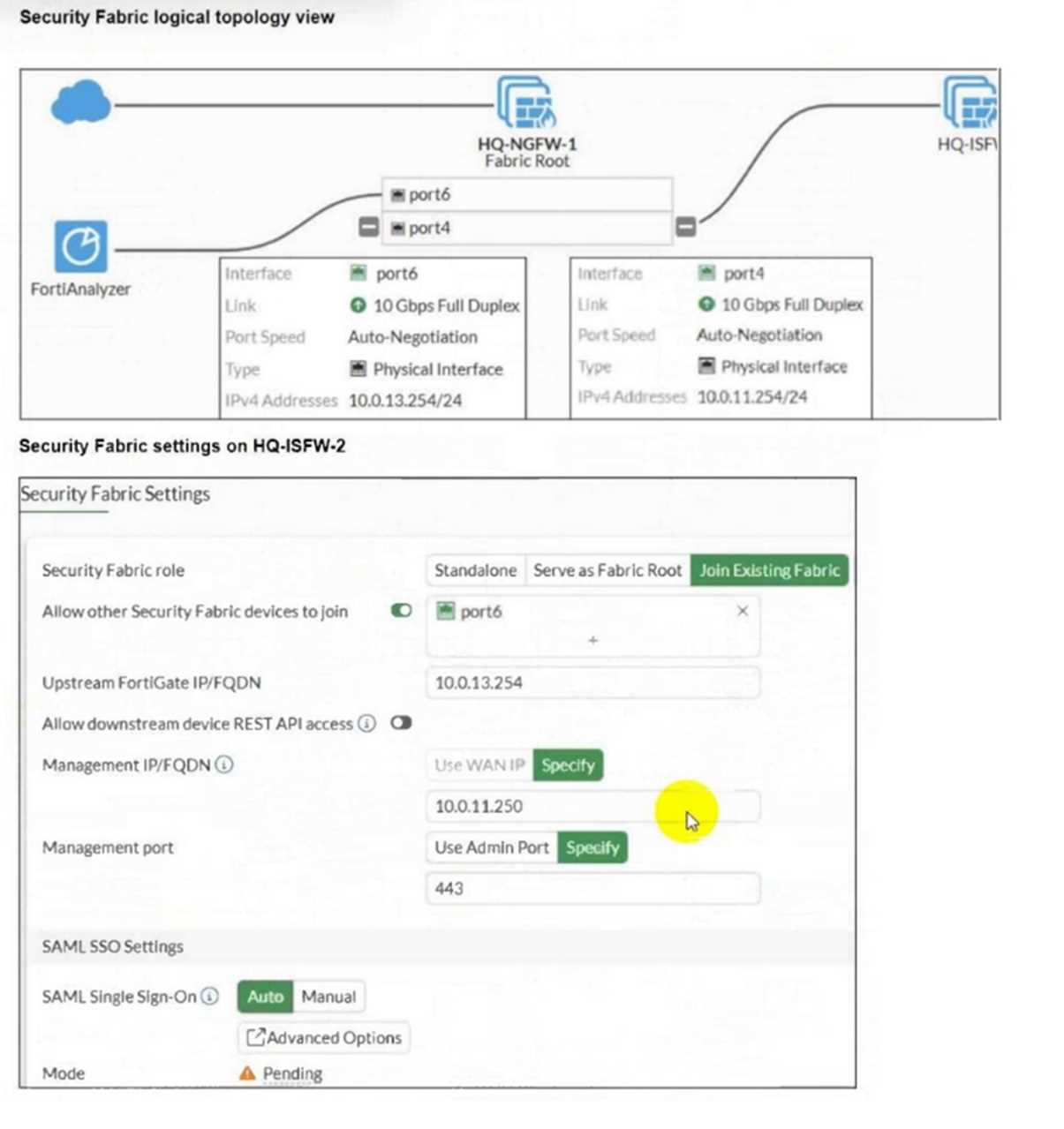
An administrator wants to add HQ-ISFW-2 in the Security Fabric. HQ-ISFW-2 is in the same subnet as
HQ-ISFW. After configuring the Security Fabric settings on HQ-ISFW-2, the status stays Pending.
What can be the two possible reasons? (Choose two.)
- A. Upstream FortiGate IP must be set to 10.0.11.254.
- B. SAML Single Sign-On must be set to Manual.
- C. HQ-ISFW-2 must be authorized on HQ-ISFW.
- D. Management IP must be set to 10.0.13.254.
Answer:
A, C
Explanation:
The Upstream FortiGate IP should match the IP address of the Fabric Root interface, which is
10.0.11.254, not 10.0.13.254.
The new device (HQ-ISFW-2) must be authorized on the Fabric Root (HQ-ISFW) before it can join the
Security Fabric, otherwise the status remains pending.
Question 8
Refer to the exhibits.
Based on the current HA status, an administrator updates the override and priority parameters on
HQ-NGFW-1 and HQ-NGFW-2 as shown in the exhibit.
What would be the expected outcome in the HA cluster?
- A. HQ-NGFW-1 will synchronize the override disable setting with HQ-NGFW-2.
- B. HQ-NGFW-2 will take over as the primary because it has the override enable setting and higher priority than HQ-NGFW-1.
- C. HQ-NGFW-1 will remain the primary because HQ-NGFW-2 has lower priority.
- D. The HA cluster will become out of sync because the override setting must match on all HA members.
Answer:
B
Explanation:
With override enabled on HQ-NGFW-2 and its higher priority (110 vs. 90), HQ-NGFW-2 will become
the primary device, preempting HQ-NGFW-1 despite the current primary status.
Question 9
Refer to the exhibits.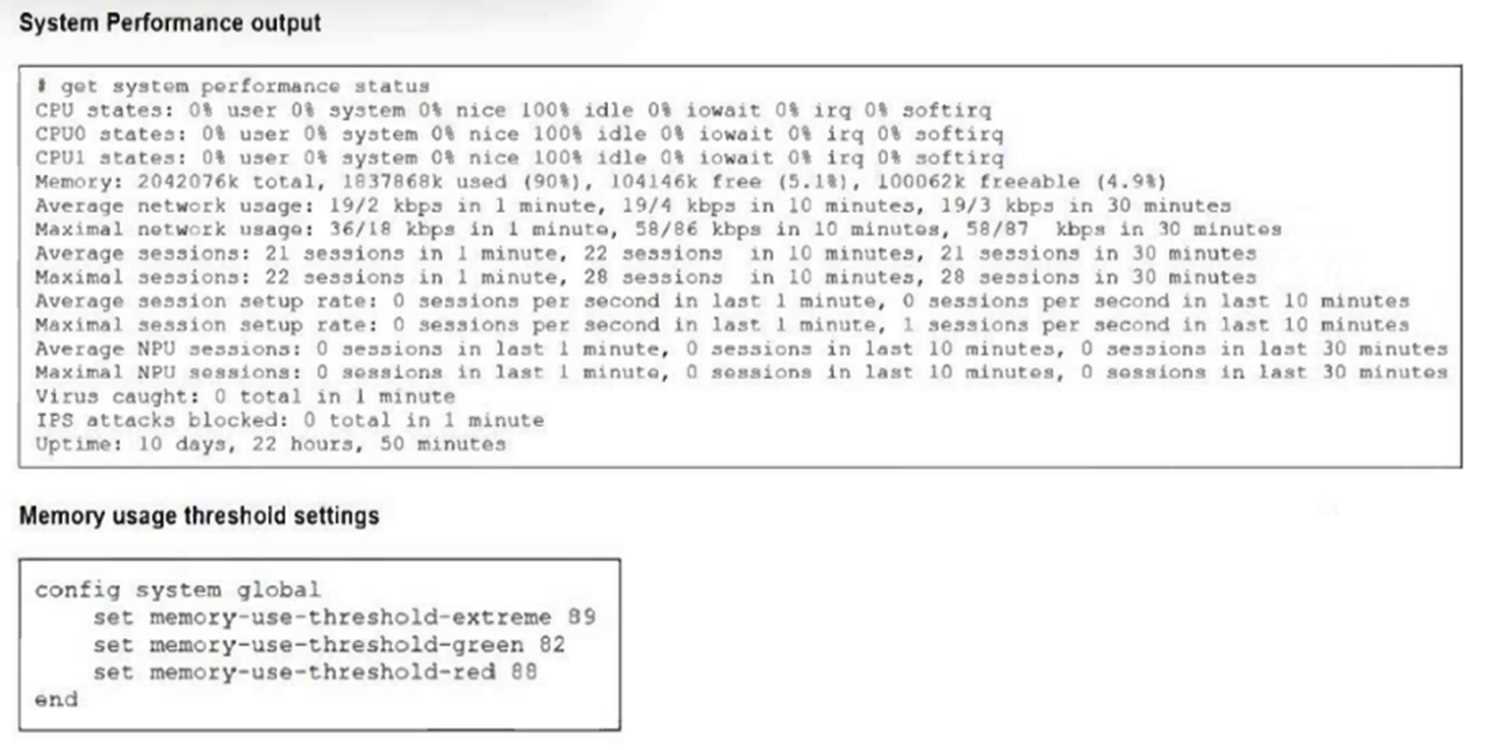
The exhibits show the system performance output and default configuration of high memory usage
thresholds on a FortiGate device.
Based on the system performance output, what are the two possible outcomes? (Choose two.)
- A. FortiGate has entered conserve mode.
- B. Administrators can access FortiGate only through the console port.
- C. Administrators can change the configuration.
- D. FortiGate drops new sessions.
Answer:
C, D
Explanation:
Since memory usage is at 90%, exceeding the red threshold (88%), FortiGate enters a state where
configuration changes are still allowed.
In this state, FortiGate drops new sessions to preserve resources and maintain stability.
Question 10
Refer to the exhibits.
The exhibits show a diagram of a FortiGate device connected to the network, and the firewall
configuration.
An administrator created a Deny policy with default settings to deny Webserver access for Remote-
User2.
The policy should work such that Remote-User1 must be able to access the Webserver while
preventing Remote-User2 from accessing the Webserver.
Which additional configuration can the administrator add to a deny firewall policy, beyond the
default behavior, to block Remote-User2 from accessing the Webserver?
- A. Disable match-vip in the Allow_access policy
- B. Configure a One-to-One IP Pool object in a new policy.
- C. Set the Destination address as Webserver in the Deny policy.
- D. Set the Destination address as Deny_IP in the Allow_access policy.
Answer:
C
Explanation:
To block Remote-User2's access to the Webserver, the deny policy must explicitly specify the
Webserver as the destination address; otherwise, it denies traffic to all destinations, which is not the
desired behavior.
Question 11
Refer to the exhibits.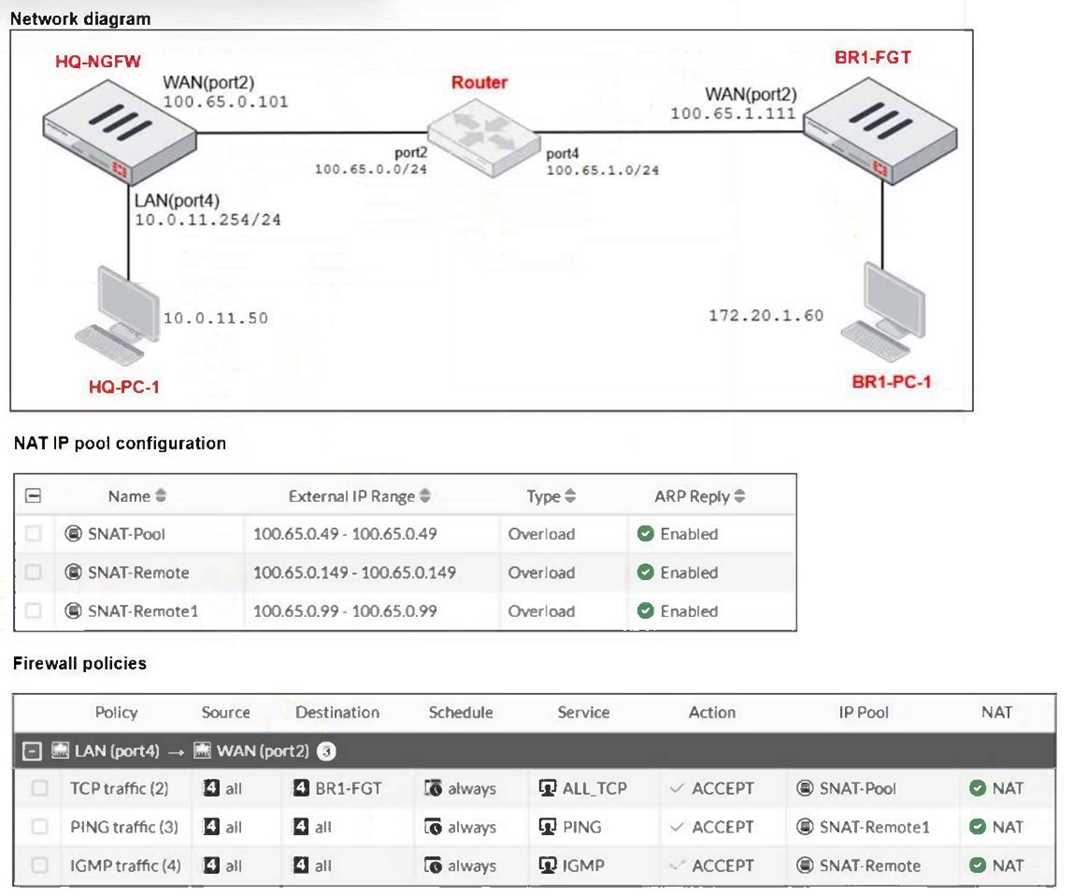
The exhibits show a diagram of a FortiGate device connected to the network, as well as the IP pool
configuration and firewall policy objects.
The WAN (port2) interface has the IP address 100.65.0.101/24.
The LAN (port4) interface has the IP address 10.0.11.254/24.
Which IP address will be used to source NAT (SNAT) the traffic, if the user on
HQ-PC-1 (10.0.11.50) pings the IP address of BR-FGT (100.65.1.111)
- A. 100.65.0.101
- B. 100.65.0.49
- C. 100.65.0.99
- D. 100.65.0.149
Answer:
C
Explanation:
The ping traffic policy uses the IP pool named SNAT-Remote1, which has the external IP range
100.65.0.99. Therefore, traffic matching this policy (ping from HQ-PC-1 to BR1-FGT) will use
100.65.0.99 for source NAT.
Question 12
What are three key routing principles in SD-WAN? (Choose three.)
- A. By default. SD-WAN rules are skipped if the included SD-WAN members do not have a valid route to the destination.
- B. SD-WAN rules have precedence over any other type of routes.
- C. Regular policy routes have precedence over SD-WAN rules.
- D. By default. SD-WAN rules are skipped if only one route to the destination is available.
- E. By default. SD-WAN rules are skipped if the best route to the destination is not an SD-WAN member.
Answer:
A, B, E
Explanation:
SD-WAN rules are skipped if none of the SD-WAN members have a valid route to the destination.
SD-WAN rules take precedence over other route types.
SD-WAN rules are skipped if the best route to the destination is not an SD-WAN member by default.
Question 13
You have configured the FortiGate device for FSSO. A user is successful in log-in to windows, but their
access to the internet is denied.
What should the administrator check first?
- A. Whether the user is assigned to the correct AD group.
- B. The FortiGate firewall policy settings for SSL decryption.
- C. The FortiGate FSSO active users list for user’s IP address.
- D. The windows event viewer for failed login attempts.
Answer:
C
Explanation:
Checking the active users list verifies if FortiGate correctly associates the user with their IP address,
ensuring proper policy enforcement for internet access.
Question 14
Which statement correctly describes NetAPI polling mode for the FSSO collector agent?
- A. The collector agent uses a Windows API to query DCs for user logins.
- B. NetAPI polling can increase bandwidth usage in large networks.
- C. The NetSessionEnum function is used to track user logouts.
- D. The collector agent must search Windows application event logs.
Answer:
B
Explanation:
NetAPI polling mode involves frequent queries to domain controllers, which can cause increased
bandwidth usage, especially in large networks with many login events.
Question 15
Refer to the exhibits.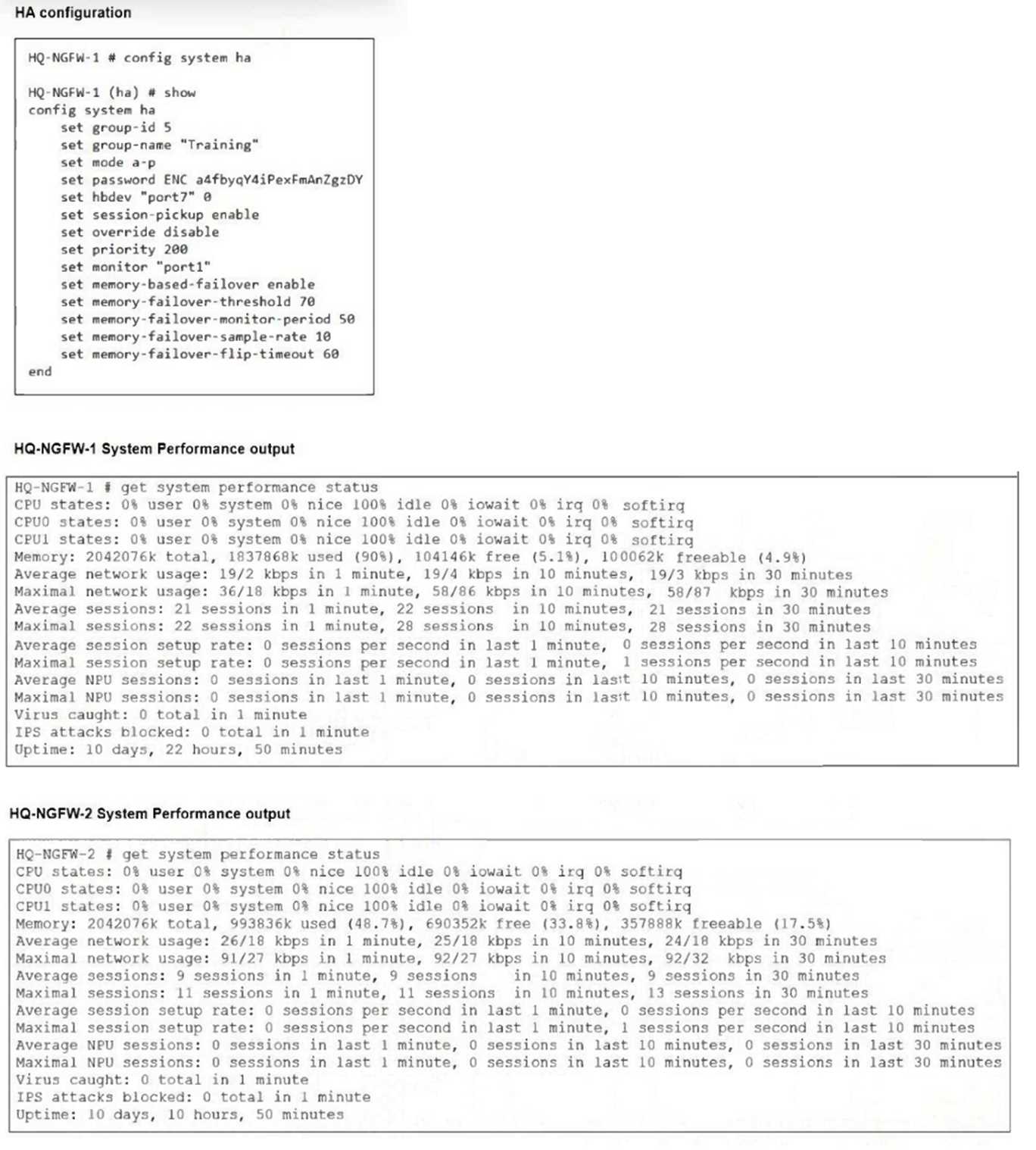
An administrator has observed the performance status outputs on an HA cluster for 55 seconds.
Which FortiGate is the primary?
- A. HQ-NGFW-2 with the parameter memory-failover-threshold setting
- B. HQ-NGFW-2 with the parameter priority setting
- C. HQ-NGFW-1 with the parameter memory-failover-flip-timeout setting
- D. HQ-NGFW-1 with the parameter override setting
Answer:
D
Explanation:
The HA configuration shows that override is disabled (set override disable), but despite this, HQ-
NGFW-1 has the higher priority (200) and is acting as the primary, as indicated by its higher resource
usage and uptime. Override allows the device with higher priority to take over as primary, so HQ-
NGFW-1 is the primary device.