Fortinet FCP FCT AD 7 2 Exam Questions
Questions for the FCP FCT AD 7 2 were updated on : Feb 22 ,2026
Page 1 out of 4. Viewing questions 1-15 out of 55
Question 1
Which statement about the FortiClient enterprise management server is true?
- A. It receives the configuration information of endpoints from ForuGate.
- B. It provides centralized management of multiple endpoints running FortiClient software.
- C. It enforces compliance on the endpoints using tags
- D. It receives the CA certificate from FortiGate to validate client certrficates.
Answer:
C
Question 2
Which two statements about ZTNA destinations are true? (Choose two.)
- A. FottiClient ZTNA destinations use an existing VPN tunnel to create a secure connection.
- B. FortiClient ZTNA destinations provides access through TCP forwarding.
- C. FortiClient ZTNA destinations do not support a wildcard FQDN.
- D. FortiClient ZTNA destination encryption is disabled by default.
- E. FortiCIient ZTNA destination authentication is enabled by default.
Answer:
C, D
Question 3
Refer to the exhibit, which shows the Zero Trust Tagging Rule Set configuration.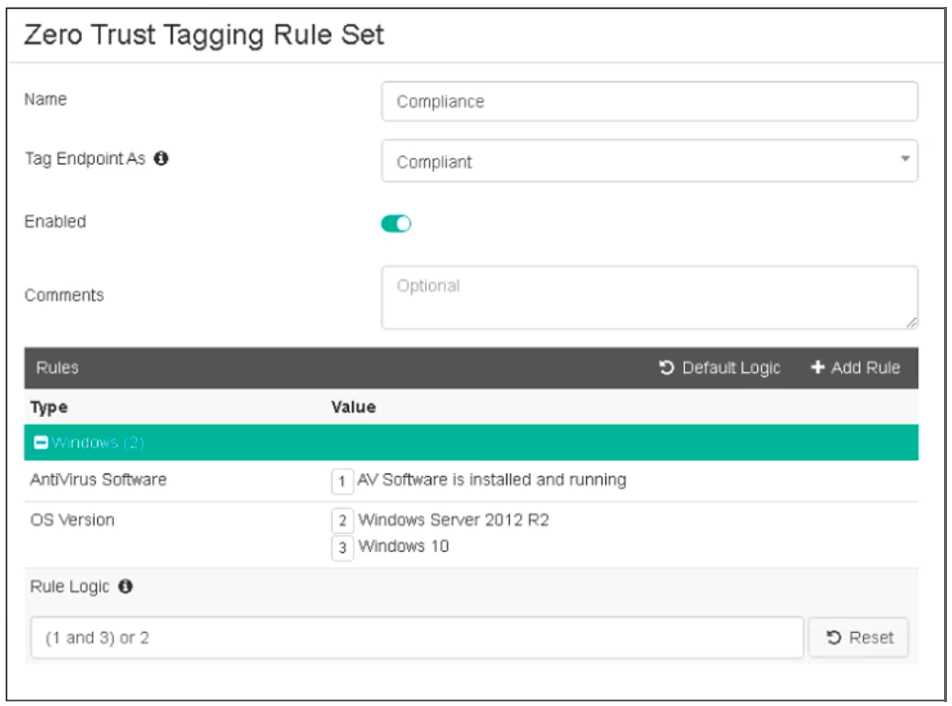
Which two statements about the rule set are true? (Choose two.)
- A. The endpoint must satisfy that only Windows 10 is running.
- B. The endpoint must satisfy that only AV software is installed and running.
- C. The endpoint must satisfy that antivirus is installed and running and Windows 10 is running.
- D. The endpoint must satisfy that only Windows Server 2012 R2 is running.
Answer:
CD
Explanation:
Based on the Zero Trust Tagging Rule Set configuration shown in the exhibit:
The rule set includes two conditions:
AV Software is installed and running
OS Version is Windows Server 2012 R2 or Windows 10
The Rule Logic is specified as "(1 and 3) or 2," meaning:
The endpoint must have antivirus software installed and running and must be running Windows 10.
Alternatively, the endpoint must be running Windows Server 2012 R2.
Therefore, the endpoint must satisfy either:
Antivirus is installed and running and Windows 10 is running.
Windows Server 2012 R2 is running.
Reference
FortiClient EMS 7.2 Study Guide, Zero Trust Tagging Rule Set Configuration Section
Fortinet Documentation on Configuring Zero Trust Tagging Rules and Logic
Question 4
Refer to the exhibit, which shows the endpoint summary information on FortiClient EMS.
What two conclusions can you make based on the Remote-Client status shown above? (Choose two.)
- A. The endpoint is classified as at risk.
- B. The endpoint has been assigned the Default endpoint policy.
- C. The endpoint is configured to support FortiSandbox.
- D. The endpoint is currently off-net.
Answer:
BD
Explanation:
Based on the Remote-Client status shown in the exhibit:
Endpoint Policy: The "Policy" field shows "Default," indicating that the endpoint has been assigned
the Default endpoint policy.
Connection Status: The "Location" field shows "Off-Fabric," meaning that the endpoint is currently off
the corporate network (off-net).
Therefore, the two conclusions that can be made are:
The endpoint has been assigned the Default endpoint policy.
The endpoint is currently off-net.
Reference
FortiClient EMS 7.2 Study Guide, Endpoint Summary Information Section
Fortinet Documentation on Endpoint Policies and Status Indicators
Question 5
Which component or device shares device status information through ZTNA telemetry?
- A. FortiClient
- B. FortiGate
- C. FortiGate Access Proxy
- D. FortiClient EMS
Answer:
A
Explanation:
FortiClient communicates directly with FortiClient EMS to continuously share device status
information through ZTNA telemetry.
Question 6
Which three types of antivirus scans are available on FortiClient? (Choose three )
- A. Proxy scan
- B. Full scan
- C. Custom scan
- D. Flow scan
- E. Quick scan
Answer:
B, C, E
Explanation:
FortiClient offers several types of antivirus scans to ensure comprehensive protection:
Full scan: Scans the entire system for malware, including all files and directories.
Custom scan: Allows the user to specify particular files, directories, or drives to be scanned.
Quick scan: Scans the most commonly infected areas of the system, providing a faster scanning
option.
These three types of scans provide flexibility and thoroughness in detecting and managing malware
threats.
Reference
FortiClient EMS 7.2 Study Guide, Antivirus Scanning Options Section
Fortinet Documentation on Types of Antivirus Scans in FortiClient
Question 7
An administrator installs FortiClient on Windows Server.
What is the default behavior of real-time protection control?
- A. Real-time protection must update AV signature database
- B. Real-time protection sends malicious files to FortiSandbox when the file is not detected locally
- C. Real-time protection is disabled
- D. Real-time protection must update the signature database from FortiSandbox
Answer:
C
Explanation:
When FortiClient is installed on a Windows Server, the default behavior for real-time protection
control is:
Real-time protection is disabled: By default, FortiClient does not enable real-time protection on
server installations to avoid potential performance impacts and because servers typically have
different security requirements compared to client endpoints.
Thus, real-time protection is disabled by default on Windows Server installations.
Reference
FortiClient EMS 7.2 Study Guide, Real-time Protection Section
Fortinet Documentation on FortiClient Default Settings for Server Installations
Question 8
Refer to the exhibit.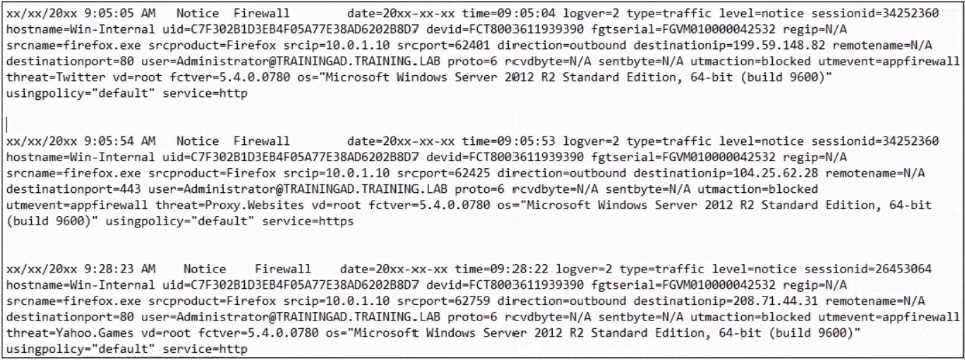
Based on the FortiClient logs shown in the exhibit which application is blocked by the application
firewall?
- A. Twitter
- B. Facebook
- C. Internet Explorer
- D. Firefox
Answer:
D
Explanation:
Based on the FortiClient logs shown in the exhibit:
The first log entry shows the application "firefox.exe" trying to access a destination IP, with the threat
identified as "Twitter."
The action taken by the application firewall is "blocked" with the event type "appfirewall."
This indicates that the application firewall has blocked access to Twitter.
Reference
FortiClient EMS 7.2 Study Guide, Application Firewall Logs Section
Fortinet Documentation on Interpreting FortiClient Logs
Question 9
Refer to the exhibit.
Based on the settings shown in the exhibit which statement about FortiClient behavior is true?
- A. FortiClient quarantines infected files and reviews later, after scanning them.
- B. FortiClient blocks and deletes infected files after scanning them.
- C. FortiClient scans infected files when the user copies files to the Resources folder
- D. FortiClient copies infected files to the Resources folder without scanning them.
Answer:
A
Explanation:
Action On Virus Discovery Warn the User If a Process Attempts to Access Infected Files Quarantine
Infected Files. You can use FortiClient to view, restore, or delete the quarantined file, as well as view
the virus name, submit the file to FortiGuard, and view logs. Deny Access to Infected Files Ignore
Infected Files
Question 10
Which statement about FortiClient enterprise management server is true?
- A. It provides centralized management of FortiGate devices.
- B. lt provides centralized management of multiple endpoints running FortiClient software.
- C. It provides centralized management of FortiClient Android endpoints only.
- D. It provides centralized management of Chromebooks running real-time protection
Answer:
B
Explanation:
FortiClient EMS is designed to provide centralized management and control of multiple endpoints
running FortiClient software. It serves as a central management server that allows administrators to
efficiently manage and configure a large number of FortiClient installations across the network.
Question 11
Refer to the exhibit.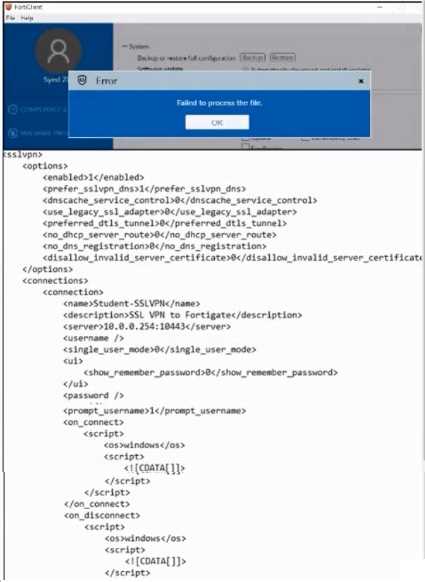
An administrator has restored the modified XML configuration file to FortiClient and sees the error
shown in the exhibit.
Based on the XML settings shown in the exhibit, what must the administrator do to resolve the issue
with the XML configuration file?
- A. The administrator must resolve the XML syntax error.
- B. The administrator must use a password to decrypt the file
- C. The administrator must change the file size
- D. The administrator must save the file as FortiClient-config conf.
Answer:
A
Explanation:
Based on the error message and the XML configuration file shown in the exhibit:
The error "Failed to process the file" typically indicates an issue with the XML syntax.
Upon reviewing the XML content, it is crucial to ensure that all tags are correctly formatted, properly
opened and closed, and that there are no syntax errors.
Resolving any XML syntax errors will allow FortiClient to successfully process and restore the
configuration file.
Therefore, the administrator must resolve the XML syntax error to fix the issue.
Reference
FortiClient EMS 7.2 Study Guide, Configuration File Management Section
General XML Syntax Guidelines and Best Practices
Question 12
Which two VPN types can a FortiClient endpoint user inmate from the Windows command prompt?
(Choose two)
- A. L2TP
- B. PPTP
- C. IPSec
- D. SSL VPN
Answer:
C, D
Explanation:
FortiClient supports initiating the following VPN types from the Windows command prompt:
IPSec VPN: FortiClient can establish IPSec VPN connections using command line instructions.
SSL VPN: FortiClient also supports initiating SSL VPN connections from the Windows command
prompt.
These two VPN types can be configured and initiated using specific command line parameters
provided by FortiClient.
Reference
FortiClient EMS 7.2 Study Guide, VPN Configuration Section
Fortinet Documentation on Command Line Options for FortiClient VPN
Question 13
Refer to the exhibit.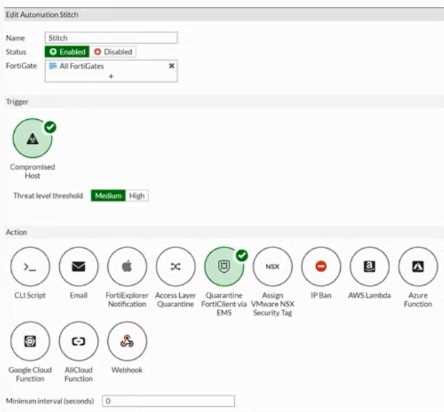
Based on the Security Fabric automation settings, what action will be taken on compromised
endpoints?
- A. Endpoints will be quarantined through EMS
- B. Endpoints will be banned on FortiGate
- C. An email notification will be sent for compromised endpoints
- D. Endpoints will be quarantined through FortiSwitch
Answer:
A
Explanation:
Based on the Security Fabric automation settings shown in the exhibit:
The automation stitch is configured with a trigger for a "Compromised Host."
The action specified for this trigger is "Quarantine FortiClient via EMS."
This indicates that when an endpoint is detected as compromised, FortiClient EMS will quarantine
the endpoint as part of the automation process.
Therefore, the action taken on compromised endpoints will be to quarantine them through EMS.
Reference
FortiGate Security 7.2 Study Guide, Automation Stitches and Actions Section
Fortinet Documentation on Configuring Automation Stitches and Quarantine Actions
Question 14
Which statement about FortiClient comprehensive endpoint protection is true?
- A. It helps to safeguard systems from email spam
- B. It helps to safeguard systems from data loss.
- C. It helps to safeguard systems from DDoS.
- D. lt helps to safeguard systems from advanced security threats, such as malware.
Answer:
D
Explanation:
FortiClient provides comprehensive endpoint protection for your Windows-based, Mac-based, and
Linuxbased desktops, laptops, file servers, and mobile devices such as iOS and Android. It helps you
to safeguard your systems with advanced security technologies, all of which you can manage from a
single management console.
Question 15
Refer to the exhibits.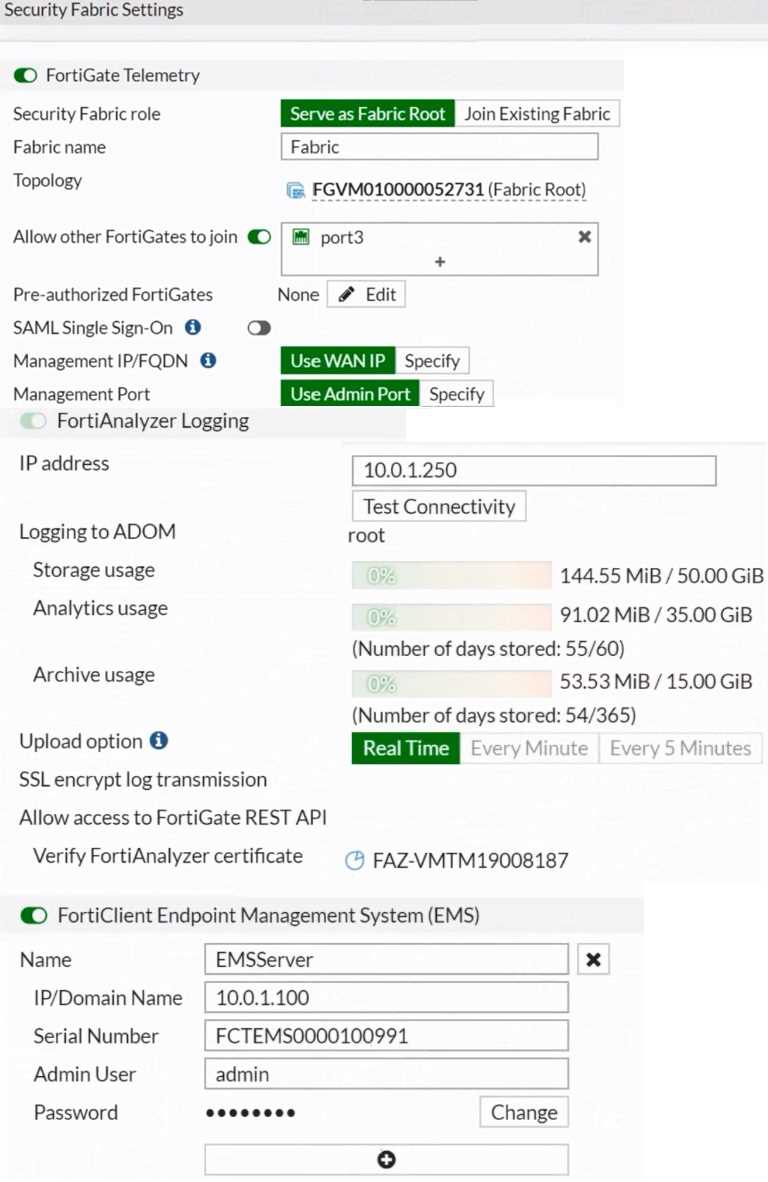

Based on the FortiGate Security Fabric settings shown in the exhibits, what must an administrator do
on the EMS server to successfully quarantine an endpoint. when it is detected as a compromised
host (loC)?
- A. The administrator must enable remote HTTPS access to EMS.
- B. The administrator must enable FQDN on EMS.
- C. The administrator must authorize FortiGate on FortiAnalyzer.
- D. The administrator must enable SSH access to EMS.
Answer:
A
Explanation:
Based on the FortiGate Security Fabric settings shown in the exhibits, to successfully quarantine an
endpoint when it is detected as a compromised host (IOC), the following step is required:
Enable Remote HTTPS Access to EMS: This setting allows FortiGate to communicate securely with
FortiClient EMS over HTTPS. Remote HTTPS access is essential for the quarantine functionality to
operate correctly, enabling the EMS server to receive and act upon the quarantine commands from
FortiGate.
Therefore, the administrator must enable remote HTTPS access to EMS to allow the quarantine
process to function properly.
Reference
FortiGate Infrastructure 7.2 Study Guide, Security Fabric and Integration with EMS Sections
Fortinet Documentation on Enabling Remote HTTPS Access to FortiClient EMS