Dell EMC DEA-2TT3 Exam Questions
Questions for the DEA-2TT3 were updated on : Jun 23 ,2025
Page 1 out of 6. Viewing questions 1-15 out of 84
Question 1
What refers to an agreement between provider and consumer that states the terms of service
usage?
- A. Service contract
- B. Service template
- C. Chargeback
- D. Showback
Answer:
A
Question 2
What is an advantage of adopting a microservices strategy in an application development
environment?
- A. All microservices of an application are always updated at the same time for maintaining consistency in the application
- B. Every microservice can be deployed, upgraded, scaled, and restarted independent of other services in the application
- C. Microservices are tightly coupled so it is easy to scale all the services at once to meet business demands
- D. Microservices provide the application platform to implement DevOps in the organization easily and at low cost
Answer:
B
Question 3
Which role in service portfolio management determines and delivers the services that provide value
and strategic advantage to the provider?
- A. Cloud Service Account Manager
- B. Cloud Automation Engineer
- C. Cloud Administrator
- D. Cloud Auditor
Answer:
C
Explanation:
Cloud administrators responsible for service portfolio management decide and deliver the services
that provide value and strategic advantage to the provider.
Question 4
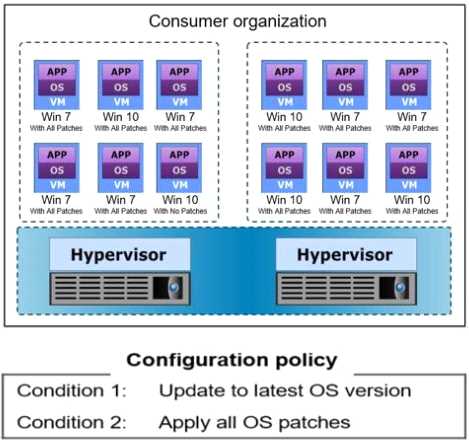
Refer to the exhibit, which represents a consumer environment consisting of multiple VMs running
Windows operating systems (OSs).
For compliance reasons, the cloud service provider maintains version control over the OS provided to
the consumer. The service provider also ensures that the configurations of the VMs comply with the
configuration policy for the OS version. The configuration policy includes the two conditions shown in
the exhibit. A monitoring tool verifies VM configurations against the configuration policy and
provides the compliance results shown.
What is the percentage of compliance non-adherence?
- A. 30.12%
- B. 33.34%
- C. 58.33%
- D. 66.67%
Answer:
D
Question 5
Which management process ensures business continuity by eliminating single points of failure in a
data center?
- A. Availability management
- B. Security management
- C. Capacity management
- D. Performance management
Answer:
A
Question 6
Which Dell EMC product is used for a disk-based backup and recovery solution that provides inherent
source-based data deduplication?
- A. NetWorker
- B. ProtectPoint
- C. Data Domain
- D. Avamar
Answer:
D
Question 7
Which phase of the cloud service lifecycle involves making business use case decisions for the cloud
service offering portfolio?
- A. Service Termination
- B. Service Planning
- C. Service Creation
- D. Service Operation
Answer:
B
Question 8
Which software-defined storage controller function gathers data about the components and brings
them under its control and management?
- A. Storage provisioning
- B. Storage discovery
- C. Resource abstraction and pooling
- D. Storage component management
Answer:
B
Explanation:
The SDS controller discovers various types of physical storage systems available in a data center. It is
to gather data about the components and bring them under its control and management. Data
collected during the discovery includes information on the storage pools and the storage ports for
each storage system.
Question 9
The incident management team is unable to determine the root cause of an incident. To which team
should the error-correction activity be transferred?
- A. Performance Management
- B. Change Management
- C. Availability Management
- D. Problem Management
Answer:
D
Explanation:
consumers can report incidents through a service desk. If the service desk is unsuccessful in
providing solutions against the incidents, they are escalated to other incident management support
groups or to problem management.
Question 10
What capability is provided by the Open and extensible attribute of software-defined infrastructure
(SDI)?
- A. Uses APIs to integrate multivendor resources into the SDI environment
- B. Optimizes resource usage and generates value reports about the SDI environment
- C. Provides a control point for the entire SDI environment
- D. Provides multitenancy that enables consumers to share resources in the SDI environment
Answer:
A
Explanation:
An extensible architecture enables integrating multivendor resources, and external management
interfaces and applications into the SDI environment by using APIs
Question 11
What mechanism does RSA SecurID use?
- A. Single sign-on authentication
- B. Policy-based authorization
- C. Multi-factor authentication
- D. Role-based authorization
Answer:
C
Explanation:
RSA SecurID is a 2-factor authentication mechanism used to protect the network resources.
Question 12
What is the function of a monitoring and alerting tool?
- A. Focus on examining the usage of resources by customers and service providers and provide notification to optimize and manage workloads
- B. Control charges for cloud usage by optimizing cloud resource utilization
- C. Automate tasks and IT processes and manage the IT environment
- D. Enable people to work closely together on a common project, in real time, by making communication among them easier
Answer:
A
Question 13
DRAG DROP
Match each information security concept with its description.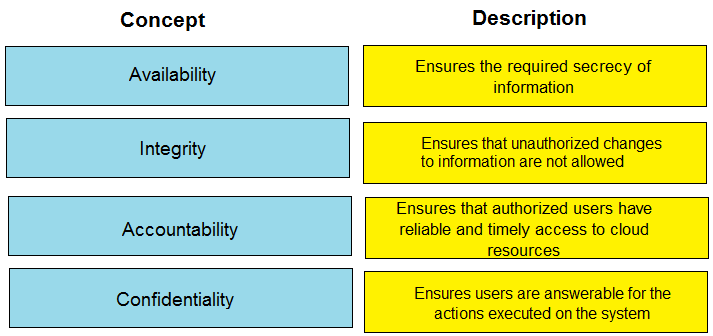
Answer:
None
Explanation:
Availability Ensures that authorized users have reliable and timely access to cloud resources
Integrity Ensures that unauthorized changes to information are not allowed
Accountability Ensures users are answerable for the actions executed on the system
Confidentiality Ensures the required secrecy of information
Question 14
What capability does an orchestration workflow provide?
- A. Helps administer the cloud infrastructure, such as adding resources to a resource pool, billing, and reporting
- B. Helps to consolidate all the IT resources in the cloud environment
- C. Enables the administrator to control the underlying physical infrastructure using a single unified management console
- D. Creates an automated set of tasks to update the service catalog by cloud consumers without requiring manual intervention
Answer:
A
Explanation:
The orchestration workflows are not only meant for fulfilling requests from consumers. It also helps
for administering cloud infrastructure, such as adding resources to a resource pool, billing, and
reporting and so on.
Question 15
What can an IT department do to better meet IT challenges and support digital businesses?
- A. Become more technology centric
- B. Focus on delivery and management of digital assets
- C. Become more service centric within cost constraints
- D. Focus on providing services without being distracted by costs
Answer:
C