comptia CNX-001 Exam Questions
Questions for the CNX-001 were updated on : Feb 22 ,2026
Page 1 out of 6. Viewing questions 1-15 out of 84
Question 1
A network engineer is setting up guest access on a Wi-Fi network. After a recent network analysis,
the engineer discovered that a user could access the guest network and attack the corporate
network, since the networks share the same VLAN. Which of the following should the engineer do to
prevent an attack like this one from happening?
- A. Configure Layer 2 client isolation for the wireless network.
- B. Set up a MAC filtering rule and add the MAC addresses of all corporate devices to the allow list.
- C. Set up a strong password on the guest wireless network.
- D. Set up a captive portal so all guest users have to register before gaining access to the wireless network.
Answer:
A
Explanation:
By enabling client isolation at Layer 2, guest clients can still reach the Internet but cannot directly
communicate with any other device on that VLAN, including your corporate endpoints, stopping
lateral attacks without needing MAC whitelists or overly complex captive-portal setups.
Question 2
A call center company provides its services through a VoIP infrastructure. Recently, the call center set
up an application to manage its documents on a cloud application. The application is causing
recurring audio losses for VoIP callers. The network administrator needs to fix the issue with the least
expensive solution. Which of the following is the best approach?
- A. Adding a second internet link and physically splitting voice and data networks into different routes
- B. Configuring QoS rules at the internet router to prioritize the VoIP calls
- C. Creating two VLANs, one for voice and the other for data
- D. Setting up VoIP devices to use a voice codec with a higher compression rate
Answer:
B
Explanation:
Prioritizing VoIP packets over the document-management traffic ensures that voice gets the
necessary bandwidth and low latency even when the network is congested - all without the cost of
new links or hardware.
Question 3
A network architect is working on a physical network design template for a small education
institution's satellite campus that is not yet built. The new campus location will consist of two small
buildings with classrooms, one screening room with audiovisual equipment, and 200 seats for
students. Which of the following enterprise network designs should the architect suggest?
- A. Hybrid
- B. Dual-layer
- C. Three-tier
- D. Collapsed core
Answer:
D
Explanation:
In a small satellite campus with limited buildings and user density, a collapsed-core (two-tier) design
combines the core and distribution layers into a single set of switches. This minimizes hardware,
simplifies management, and still provides the necessary segmentation and resiliency for the
classrooms, screening room, and student seating areas.
Question 4
A SaaS company's new service currently is being provided through four servers. The company's end
users are having connection issues, which is affecting about 25% of the connections. Which of the
following is most likely the root cause of this issue?
- A. The service is using round-robin load balancing through a DNS server with one server down.
- B. The service is using weighted load balancing with 40% of the traffic on server A, 20% on server B, 20% on server C, and server D is down.
- C. The service is using a least-connection load-balancing method with one server down.
- D. Load balancing is configured with a health check in front of these servers, and one of these servers is unavailable.
Answer:
A
Explanation:
With simple round-robin DNS distributing 25% of requests to each of four servers, a single server
outage directly causes exactly 25% of connections to fail, matching the reported impact.
Question 5
A network engineer at an e-commerce organization must improve the following dashboard due to a
performance issue on the website: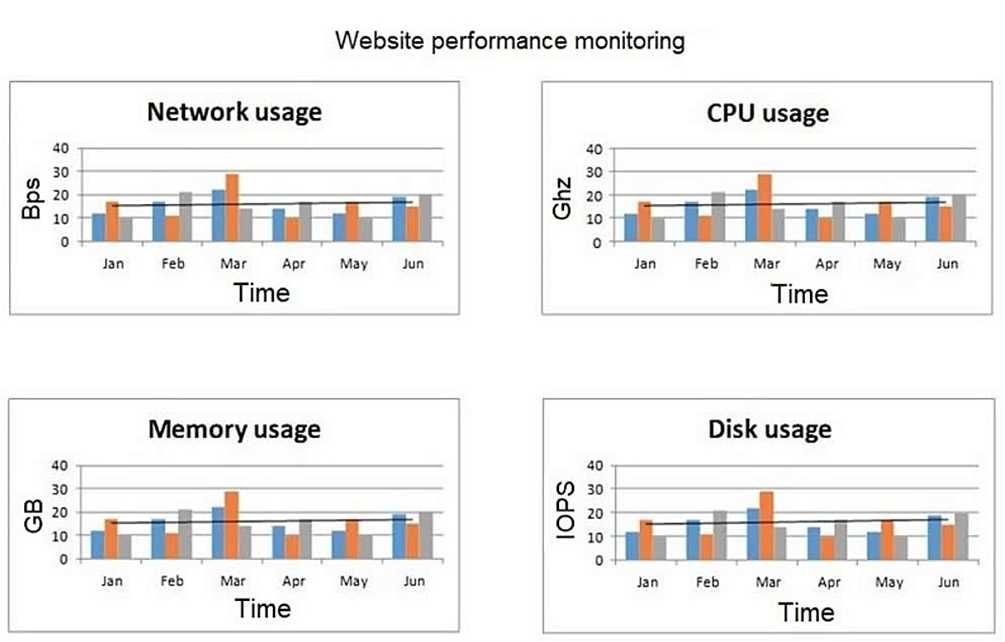
Which of the following is the most useful information to add to the dashboard for the operations
team's?
- A. 404 errors
- B. Concurrent users
- C. Number of orders
- D. Number of active incidents
Answer:
B
Explanation:
Adding a concurrent-user count gives you the key context you’re missing: it ties spikes in CPU,
memory, disk I/O, and network traffic directly to how many people are actively hitting the site. You
can then see whether performance issues align with increases in user load, enabling more targeted
capacity planning and troubleshooting.
Question 6
A network administrator must connect a remote building at a manufacturing plant to the main
building via a wireless connection. Which of the following should the administrator choose to get the
greatest possible range from the wireless connection? (Choose two.)
- A. 2.4GHz
- B. 5GHz
- C. 6GHz
- D. Omnidirectional antenna
- E. Patch antenna
- F. Built-in antenna
Answer:
A, E
Explanation:
2.4 GHz: The lower-frequency 2.4 GHz band propagates farther and better penetrates obstacles than
5 GHz or 6 GHz, giving you greater link distance.
Patch antenna: A directional (patch) antenna focuses RF energy into a narrow beam, maximizing gain
and range between two fixed points – the best for a long-haul wireless link.
Question 7
An administrator must ensure that credit card numbers are not contained in any outside messaging
or file transfers from the organization. Which of the following controls meets this requirement?
- A. Intrusion detection system
- B. Egress filtering
- C. Data loss prevention
- D. Encryption in transit
Answer:
C
Explanation:
Data Loss Prevention solutions inspect outbound communications and file transfers for sensitive data
patterns, such as credit card numbers, and block or quarantine any messages that contain them,
ensuring that no payment card details leave the organization.
Question 8
A company provides an API that runs on the public cloud for its customers. A fixed number of VMs
host the APIs. During peak hours, the company notices a spike in usage that results in network
communication speeds slowing down for all customers. The management team has decided that
access for all customers should be fair and accessible at all times. Which of the following is the most
cost-effective way to address this issue?
- A. Use an allow list for customers using APIs.
- B. Increase the number of VMs running APIs.
- C. Enable throttling on APIs.
- D. Increase the MTU on the VMs.
Answer:
C
Explanation:
Implementing request throttling (rate limiting) lets you cap how many requests each customer can
make per time unit. This ensures no single user can saturate the API servers, providing fair access
across all customers without the recurring costs of adding more VMs.
Question 9
An organization with an on-premises data center is adopting additional cloud-based solutions. The
organization wants to keep communication secure between remote employees' devices and
workloads. Which of the following ZTA features best achieves this goal?
- A. Secure service edge
- B. Cloud access security broker
- C. Principle of least privilege
- D. Identity as the perimeter
Answer:
D
Explanation:
Shifting to “identity as the perimeter” means that each remote user and device’s identity (and
context) becomes the basis for granting secure, encrypted access directly to workloads, regardless of
the underlying network, ensuring communications are authenticated and authorized per-session.
Question 10
A cafe uses a tablet-based point-of-sale system. Customers are complaining that their food is taking
too long to arrive. During an investigation, the following is noticed:
Every kitchen printer did not print the orders.
Payments are processing correctly.
The cloud-based system has record of the orders.
This issue occurred when the cafe was busy.
Which of the following is the best way to mitigate this issue?
- A. Updating the application
- B. Adding an access point exclusively for the kitchen
- C. Upgrading the kitchen printers' wireless dongles
- D. Assigning the kitchen printers static IP addresses
Answer:
B
Explanation:
By dedicating a separate Wi-Fi access point to the printers, you isolate their traffic from the
customer-facing tablets. This prevents congestion during busy periods, ensuring orders reliably print
even when the main network is under heavy load.
Question 11
A network architect is designing a new network for a rural hospital system. Given the following
requirements:
* Highly available
* Consistent data transmission
* Resilient to simultaneous failures
Which of the following topologies should the architect use?
- A. Collapsed core
- B. Hub-and-spoke
- C. Mesh
- D. Star
Answer:
D
Explanation:
A full-mesh topology provides multiple redundant, direct paths between every site, eliminating
single points of failure, ensuring consistent transmission even if one or more links fail, and
maximizing overall availability.
Question 12
A global company has depots in various locations. A proprietary application was deployed locally at
each of the depots, but issues with getting the consolidated data instantly occurred. The Chief
Information Officer decided to centralize the application and deploy it in the cloud. After the cloud
deployment, users report the application is slow. Which of the following is most likely the issue?
- A. Throttling
- B. Overutilization
- C. Packet loss
- D. Latency
Answer:
D
Explanation:
Centralizing the application in the cloud introduces longer round-trip times for geographically
dispersed users. The increased propagation delay (“latency”) is the most likely cause of the perceived
slowness.
Question 13
A network load balancer is not correctly validating a client TLS certificate. The network architect
needs to validate the certificate installed on the load balancer before progressing. Which of the
following commands should the architect use to confirm whether the private key and certificate
match?
- A. openssl-list -noout -modulus -in cert.crt | openssl md5 openssl rsa -noout -modulus -in privkey.txt | openssl md5
- B. openssl req -in certificate.csr -verify openssl-verify -noout -modulus -in privkey.txt | openssl md5
- C. openssl-rsa -noout -modulus -in cert.crt | openssl md5 openssl-verify -noout -modulus -in privkey.txt | openssl md5
- D. openssl x509 -noout -modulus -in cert.crt | openssl md5 openssl rsa -noout -modulus -in privkey.txt | openssl md5
Answer:
D
Explanation:
If the MD5 hashes match, the certificate and private key correspond correctly.
Question 14
An administrator needs to add a device to the allow list in order to bypass user authentication of an
AAA system. The administrator uses MAC filtering and needs to discover the device's MAC address to
accomplish this task. The device receives an IP address from DHCP, but the IP address changes daily.
Which of the following commands should the administrator run on the device to locate its MAC
address?
- A. ipconfig /all
- B. netstat -an
- C. arp -a
- D. nslookup
Answer:
A
Explanation:
Running ipconfig /all on the device will display the physical (MAC) address of each network adapter,
allowing you to copy the correct MAC for your allow-list entry.
Question 15
A company hosts its application s on the cloud and is expanding its business to Europe. The company
must comply with General Data Protection Regulation to limit European customers' access to dat
a. The network team configures the firewall rules but finds that some customers in the United States
can access data hosted in Europe. Which of the following is the best option for the network team to
configure?
- A. SASE
- B. Network security groups
- C. CDN
- D. Geofencing rule
Answer:
D
Explanation:
Using a geofencing (geo-restriction) policy lets you block or allow traffic based on the client’s
geographic location. This ensures that only users in approved regions (e.g., the United States) can
reach the European-hosted data, effectively preventing unintended European customer access
without complex IP ACLs.