cisco 300-735 Exam Questions
Questions for the 300-735 were updated on : Jun 28 ,2025
Page 1 out of 4. Viewing questions 1-15 out of 59
Question 1
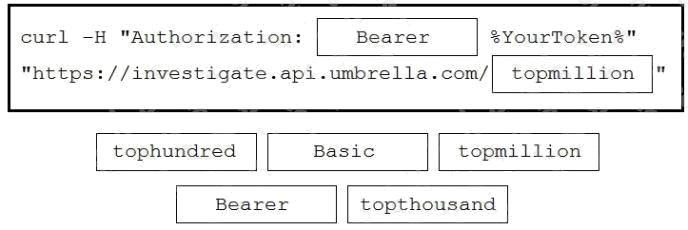
DRAG DROP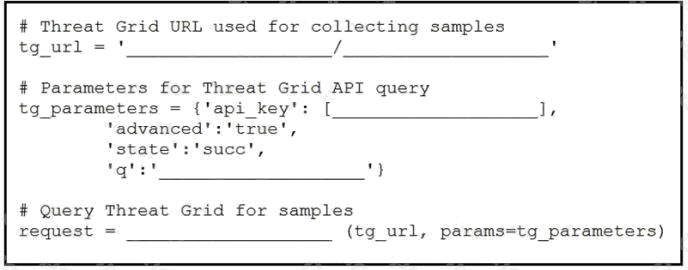
Refer to the exhibit.
Drag and drop the elements from the left onto the script on the right that queries Cisco ThreatGRID for indications of
compromise.
Select and Place: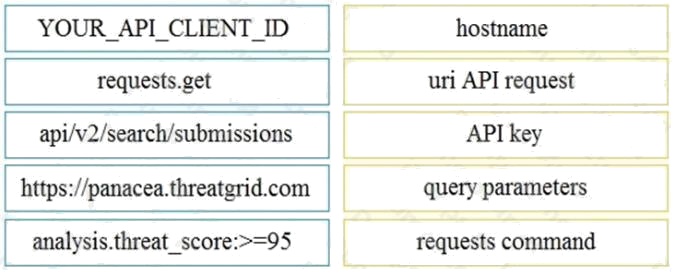
Answer:
Explanation:
Reference: https://community.cisco.com/t5/endpoint-security/amp-threat-grid-api/m-p/3538319
Question 2
Which API capability is available on Cisco Firepower devices?
- A. Firepower Management Center - Sockets API
- B. Firepower Management Center - eStreamer API
- C. Firepower Management Center - Camera API
- D. Firepower Management Center - Host Output API
Answer:
B
Question 3
Which API is designed to give technology partners the ability to send security events from their platform/service/appliance
within a mutual customer's environment to the Umbrella cloud for enforcement?
- A. Cisco Umbrella Management API
- B. Cisco Umbrella Security Events API
- C. Cisco Umbrella Enforcement API
- D. Cisco Umbrella Reporting API
Answer:
C
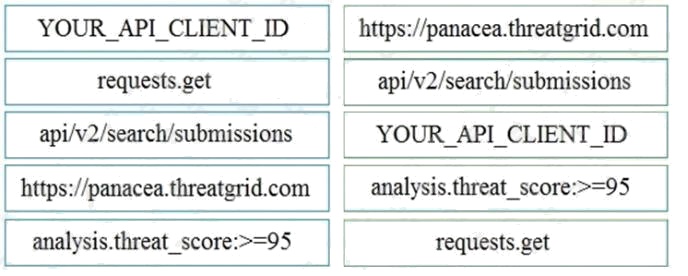
Question 4
Refer to the exhibit. The security administrator must temporarily disallow traffic that goes to a production web server using
the Cisco FDM REST API. The administrator sends an API query as shown in the exhibit.
What is the outcome of that action?
- A. The given code does not execute because the mandatory parameters, source, destination, and services are missing.
- B. The given code does not execute because it uses the HTTP method "PUT". It should use the HTTP method "POST".
- C. The appropriate rule is updated with the source, destination, services, and other fields set to "Any" and the action set to "DENY". Traffic to the production web server is disallowed, as expected.
- D. A new rule is created with the source, destination, services, and other fields set to "Any" and the action set to "DENY". Traffic to the production web server is disallowed, as expected.
Answer:
C
Question 5
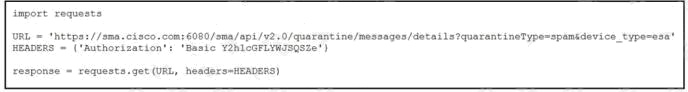
Refer to the exhibit. A security engineer attempts to query the Cisco Security Management appliance to retrieve details of a
specific message.
What must be added to the script to achieve the desired result?
- A. Add message ID information to the URL string as a URI.
- B. Run the script and parse through the returned data to find the desired message.
- C. Add message ID information to the URL string as a parameter.
- D. Add message ID information to the headers.
Answer:
C
Question 6
What is the purpose of the snapshot APIs exposed by Cisco Stealthwatch Cloud?
- A. Report on flow data during a customizable time period.
- B. Operate and return alerts discovered from infrastructure observations.
- C. Return current configuration data of Cisco Stealthwatch Cloud infrastructure.
- D. Create snapshots of supported Cisco Stealthwatch Cloud infrastructure.
Answer:
B
Question 7
Which two event types can the eStreamer server transmit to the requesting client from a managed device and a
management center? (Choose two.)
- A. user activity events
- B. intrusion events
- C. file events
- D. intrusion event extra data
- E. malware events
Answer:
B D
Question 8
For which two programming languages does Cisco offer an SDK for Cisco pxGrid 1.0? (Choose two.)
- A. Python
- B. Perl
- C. Java
- D. C
- E. JavaScript
Answer:
C D
Question 9
DRAG DROP
Drag and drop the items to complete the curl request to the ThreatGRID API. The API call should request the first 10 IP
addresses that ThreatGRID saw samples communicate with during analysis, in the first two hours of January 18th (UTC
time), where those communications triggered a Behavior Indicator that had a confidence equal to or higher than 75 and a
severity equal to or higher than 95.
Select and Place: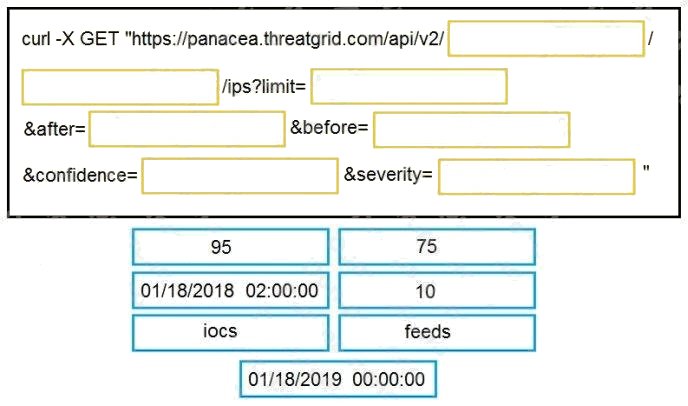
Answer:
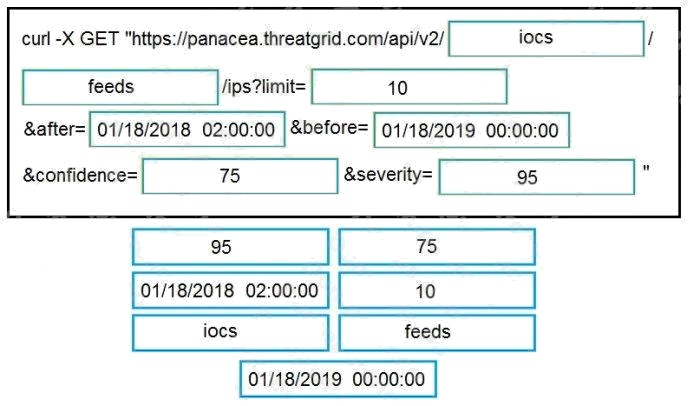
Explanation:
Reference:
https://support.umbrella.com/hc/en-us/articles/231248768-Cisco-Umbrella-Cisco-AMP-Threat-Grid-Cloud-Integration-Setup-
Guide
Question 10
DRAG DROP
Drag and drop the code to complete the curl command to query the Cisco Umbrella Investigate API for the umbrella
popularity list. Not all options are used.
Select and Place: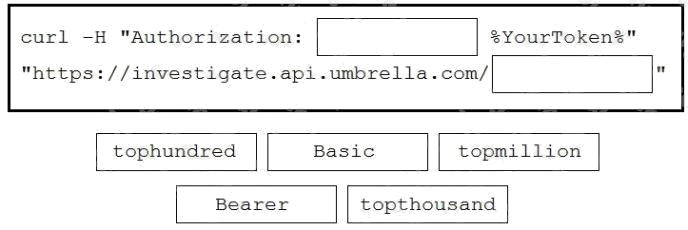
Answer:
Explanation:
Reference: https://docs.umbrella.com/investigate-api/reference
Question 11
What are two benefits of Ansible when managing security platforms? (Choose two.)
- A. End users can be identified and tracked across a network.
- B. Network performance issues can be identified and automatically remediated.
- C. Policies can be updated on multiple devices concurrently, which reduces outage windows.
- D. Anomalous network traffic can be detected and correlated.
- E. The time that is needed to deploy a change is reduced, compared to manually applying the change.
Answer:
C E
Question 12
Which request searches for a process window in Cisco ThreatGRID that contains the word “secret”?
- A. /api/v2/search/submissions?term=processwindow&title=secret
- B. /api/v2/search/submissions?term=processwindow&q=secret
- C. /api/v2/search/submissions?term=window&title=secret
- D. /api/v2/search/submissions?term=process&q=secret
Answer:
D
Question 13
After changes are made to the Cisco Firepower Threat Defense configuration using the Cisco Firepower Device Manager
API, what must be done to ensure that the new policy is activated?
- A. Submit a POST to the /api/fdm/latest/operational/deploy URI.
- B. Submit a GET to the /api/fdm/latest/operational/deploy URI.
- C. Submit a PUT to the /api/fdm/latest/devicesettings/pushpolicy URI.
- D. Submit a POST to the /api/fdm/latest/devicesettings/pushpolicy URI.
Answer:
A
Question 14
Which two APIs are available from Cisco ThreatGRID? (Choose two.)
- A. Access
- B. User Scope
- C. Data
- D. Domains
- E. Curated Feeds
Answer:
C E
Question 15
Which snippet describes the way to create an URL object in Cisco FDM using FDM REST APIs with curl?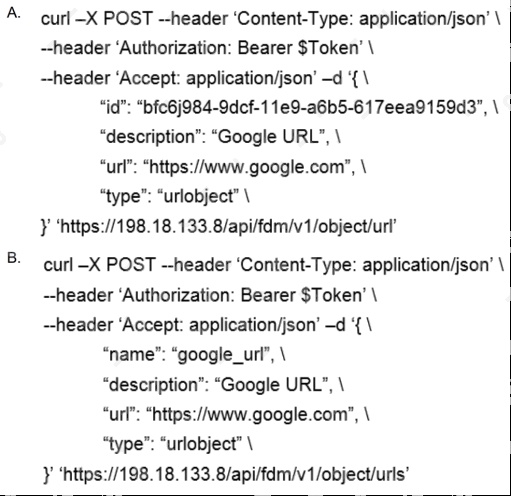
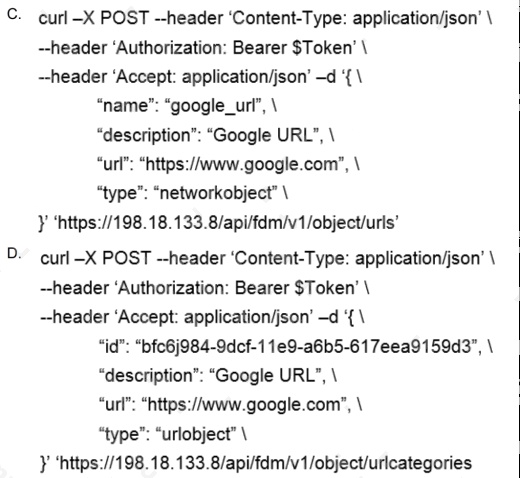
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer:
B